Cuckoo Integration with CloudDefense.AI
Integrating Cuckoo with CloudDefense.AI enhances threat analysis and incident response capabilities, providing real-time insights and proactive security measures for better protection against advanced malware and cyber attacks.
Integration of Cuckoo with CloudDefense.AI
What is Cuckoo?
Cuckoo is an open-source, automated malware analysis system designed to detect and analyze malicious software. It provides a platform for examining potentially harmful files and URLs in a secure virtual environment. Cuckoo dynamically monitors and reports the behavior of files and processes, helping cybersecurity professionals understand and respond to threats effectively.
Benefits of integrating Cuckoo with CloudDefense.AI
Integrating Cuckoo with CloudDefense.AI offers several advantages for enhancing cloud security. Firstly, Cuckoo's advanced malware analysis capabilities enable effective identification and isolation of potential threats within a cloud environment. This integration enables CloudDefense.AI to provide enhanced threat intelligence and detection capabilities, ensuring robust protection against malware attacks.
Secondly, the combination of Cuckoo and CloudDefense.AI enables proactive threat hunting and response. With Cuckoo's comprehensive analysis and CloudDefense.AI's real-time monitoring and scanning capabilities, security teams can quickly identify and mitigate potential vulnerabilities, minimizing the risk of data breaches and other security incidents.
Lastly, the integration with CloudDefense.AI allows for seamless automation and orchestration of security processes. By combining the malware analysis capabilities of Cuckoo with CloudDefense.AI's suite of DevSecOps tools, security operations can be streamlined and automated, improving overall efficiency and reducing the time taken to identify and respond to threats.
How does CloudDefense.AI help secure your cloud infra and applications through dev sec ops tools that scan code in repositories, scans web apps and cloud tools like ciem, cspm, attack graph and more?
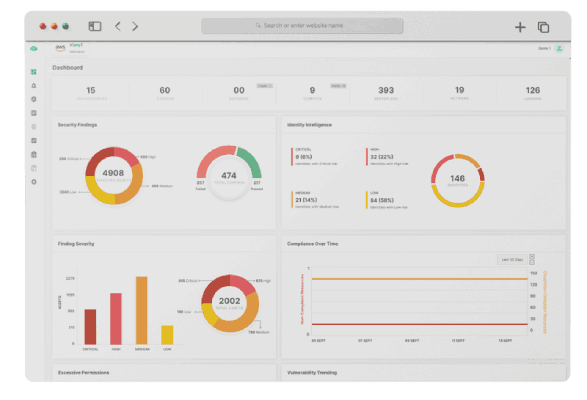
CloudDefense.AI offers a range of development security operations (DevSecOps) tools that aid in securing cloud infrastructure and applications. These tools scan code in repositories, web applications, and cloud-native tools such as cloud infrastructure and configuration as code, cloud security posture management (CSPM), and attack graphs.
By scanning code in repositories, CloudDefense.AI can detect potential vulnerabilities and insecure coding practices, allowing developers to address them before deployment. This proactive approach enhances the security of cloud applications and reduces the risk of exploitation by malicious actors.
Furthermore, CloudDefense.AI's scanning of web applications ensures that vulnerabilities within the application layer are identified and remediated. This helps in preventing attacks such as cross-site scripting (XSS), SQL injection, and other common web application vulnerabilities that can be exploited by threat actors.
CloudDefense.AI's integration with cloud tools like Cloud Infrastructure and Entitlements Management (CIEM) and cloud security posture management (CSPM) provides visibility into and control over the security posture of cloud infrastructures. It helps in identifying misconfigurations, access control issues, and compliance gaps, and provides recommendations to ensure a secure cloud environment.
Additionally, the integration with attack graph technology allows security teams to visualize and understand the potential attack surface within the cloud infrastructure. This helps in prioritizing security efforts, identifying weak points, and implementing appropriate mitigation measures.
In summary, CloudDefense.AI's DevSecOps tools, combined with its integration with various scanning capabilities, enhance cloud infrastructure and application security by detecting vulnerabilities, ensuring proper coding practices, and providing a holistic view of the security posture.
Instructions for integrating Cuckoo with CloudDefense.AI
Installing Cuckoo in CloudDefense.AI's dev sec ops platform is a seamless process, providing powerful malware analysis capabilities. With just a few steps, Cuckoo integrates effortlessly, allowing for efficient and comprehensive threat detection and analysis in the cloud environment.
Book A Live Demo
Integrating your cloud infrastructure with Cuckoo and CloudDefense.AI is seamless and straightforward, ensuring robust protection against cyber threats. Cuckoo is an open-source malware analysis sandbox that provides advanced insights and analysis into potentially malicious files and URLs.
Book A Live Demo