DevOps Integration with CloudDefense.AI
Integrating DevOps with CloudDefense.AI enhances security by automating vulnerability scanning, threat detection, and incident response, ensuring continuous protection throughout the software development lifecycle.
Integration of DevOps with CloudDefense.AI
What is DevOps?
DevOps is a software development approach that combines development and operations teams to foster collaboration and improve the overall efficiency of software delivery. It emphasizes communication, automation, and shared responsibility throughout the software development lifecycle. By integrating development and operations processes, DevOps aims to speed up release cycles, enhance productivity, and deliver high-quality applications.
Benefits of integrating DevOps with CloudDefense.AI
Integrating DevOps with CloudDefense.AI offers several significant advantages. First and foremost, it enhances security throughout the software development process. By integrating security into the development pipeline, vulnerabilities and weaknesses can be identified and addressed early on, reducing the risk of security breaches and ensuring compliance with industry standards and regulations.
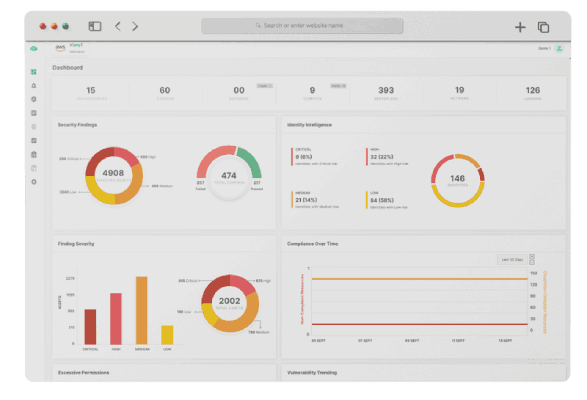
Additionally, the combination of DevOps and CloudDefense.AI facilitates seamless deployment and management of cloud infrastructure and applications. CloudDefense.AI provides a range of robust dev sec ops tools that scan code in repositories, web applications, and various cloud tools such as CIEM (Cloud Infrastructure Entitlement Management) and CSPM (Cloud Security Posture Management). These tools enable automated scanning for security flaws, potential risks, and unauthorized access, ensuring the integrity and protection of cloud environments.
Furthermore, CloudDefense.AI's attack graph and other advanced features empower organizations to visualize potential attack vectors and plan effective security strategies. By identifying vulnerabilities and understanding potential threats, DevOps teams can proactively strengthen their cloud infrastructure's security posture, minimizing the possibility of cybersecurity incidents and improving overall resilience.
In summary, integrating DevOps with CloudDefense.AI enhances security, streamlines cloud infrastructure deployment, and provides valuable insights into potential vulnerabilities and risks, leading to a more secure and efficient software development lifecycle.
Instructions for integrating DevOps with CloudDefense.AI
Installing DevOps in CloudDefense.AI's dev sec ops platform is a breeze; with its seamless integration and powerful automation tools, implementing DevOps practices becomes effortless, ensuring efficient collaboration between development, security, and operations teams for a streamlined software delivery process. DevOps is a software development methodology that emphasizes collaboration, communication, and automation between software development, IT operations, and security teams. Its goal is to deliver high-quality software faster and more reliably by breaking down silos and implementing continuous integration, delivery, and monitoring practices.
Book A Live Demo
Integrating your cloud infrastructure with DevOps and CloudDefense.AI is a seamless process, ensuring efficient and secure development and deployment. DevOps is a collaborative approach that combines development and operations, using automation and continuous delivery for faster software development and deployment.
Book A Live Demo