Emerging Threats Integration with CloudDefense.AI
Integrating Emerging Threats with CloudDefense.AI enhances cybersecurity readiness and protection by leveraging up-to-date threat intelligence for proactive defense and mitigation against emerging cyber threats.
Integration of Emerging Threats with CloudDefense.AI
What is Emerging Threats?
Emerging Threats encompass the latest and evolving risks and vulnerabilities in the field of cybersecurity. These threats may include new types of malware, hacking techniques, phishing attacks, or any other form of security breach that poses a potential danger to computer systems, networks, or data. Staying informed about emerging threats is crucial for organizations to effectively protect their sensitive information and maintain a robust security posture.
Benefits of integrating Emerging Threats with CloudDefense.AI
Integrating Emerging Threats with CloudDefense.AI offers several key benefits. Firstly, it enhances the threat intelligence capabilities of CloudDefense.AI, ensuring that it stays up-to-date with the latest and emerging security risks. This enables organizations to proactively detect and respond to threats before they can cause significant damage.
Moreover, by leveraging Emerging Threats through CloudDefense.AI, organizations can implement more comprehensive security measures. They can gather insights about new attack vectors, vulnerabilities, and trends, allowing them to fortify their defenses and tailor their cybersecurity strategies accordingly. This integration also facilitates the automation of threat intelligence analysis, enabling faster response times and reducing the overall risk exposure.
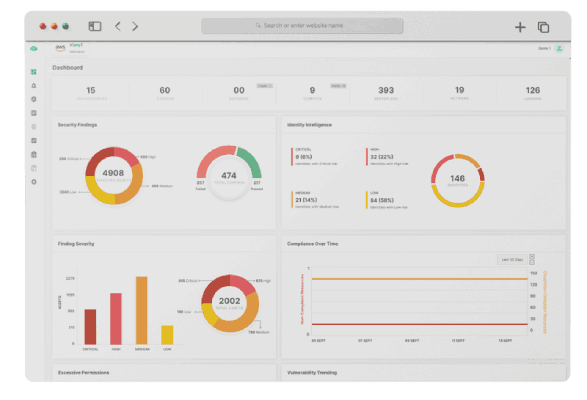
How CloudDefense.AI enhances cloud infrastructure and application security
CloudDefense.AI safeguards cloud infrastructures and applications through a suite of state-of-the-art dev sec ops tools. These tools enable organizations to scan code in repositories, web applications, and cloud tools like CIEM (Cloud Infrastructure and Entitlement Management) and CSPM (Cloud Security Posture Management).
By scanning code in repositories, CloudDefense.AI identifies any potential vulnerabilities, code flaws, or malicious code present in the software development lifecycle. This allows organizations to rectify these issues proactively, ensuring that their applications are secure from the ground up.
Furthermore, CloudDefense.AI scans web applications and cloud tools like CIEM and CSPM to identify misconfigurations, compliance violations, or any security gaps that could expose sensitive information. This comprehensive approach helps organizations maintain a strong security posture and minimize the risk of unauthorized access or data breaches.
CloudDefense.AI also offers capabilities like attack graph analysis, which visualizes the relationship between vulnerabilities and potential attack paths within the cloud infrastructure. By understanding these attack paths, organizations can prioritize and implement remediation strategies effectively, enhancing the overall security of the cloud environment.
Instructions for integrating Emerging Threats with CloudDefense.AI
Installing Emerging Threats in CloudDefense.AI's dev sec ops platform is incredibly easy, offering seamless integration and enhancing the platform's security capabilities. Emerging Threats provides comprehensive threat intelligence, enabling proactive threat detection and prevention for robust cybersecurity measures.
Book A Live Demo
Integrating your cloud infrastructure with Emerging Threats and CloudDefense.AI is seamless, ensuring comprehensive protection against emerging threats. Emerging Threats is a leading threat intelligence platform that delivers real-time information about the latest cybersecurity risks and vulnerabilities.
Book A Live Demo