In today’s application development era, where enterprises are leveraging numerous third-party dependencies, compliance is no longer a one-time checkbox at the end of the year. Modern organizations are now operating in a highly regulated, ever-expanding security framework where compliance has become a continuous requirement. From SOC 2, PCI DSS, and GDPR to ISO 27001 and HIPAA, each standard has its own requirements and audit process.
Enterprises usually leverage traditional approaches to manually collect evidence and perform interval audits, which is no longer sufficient. Based on reports, organisations spend 4000+ hours per year on compliance activity, and more than 50% of it is consumed during manual evidence collection and report generation.
This is where QINA Pulse shines by addressing all the difficulties and automating the complete process. Through native integration, it offers continuous compliance monitoring, automated evidence collection, and streamlined reporting. This guide explores how QINA Pulse is automating compliance reporting and why continuous compliance reports have become a necessity.
The Hidden Cost of Manual Compliance Reporting
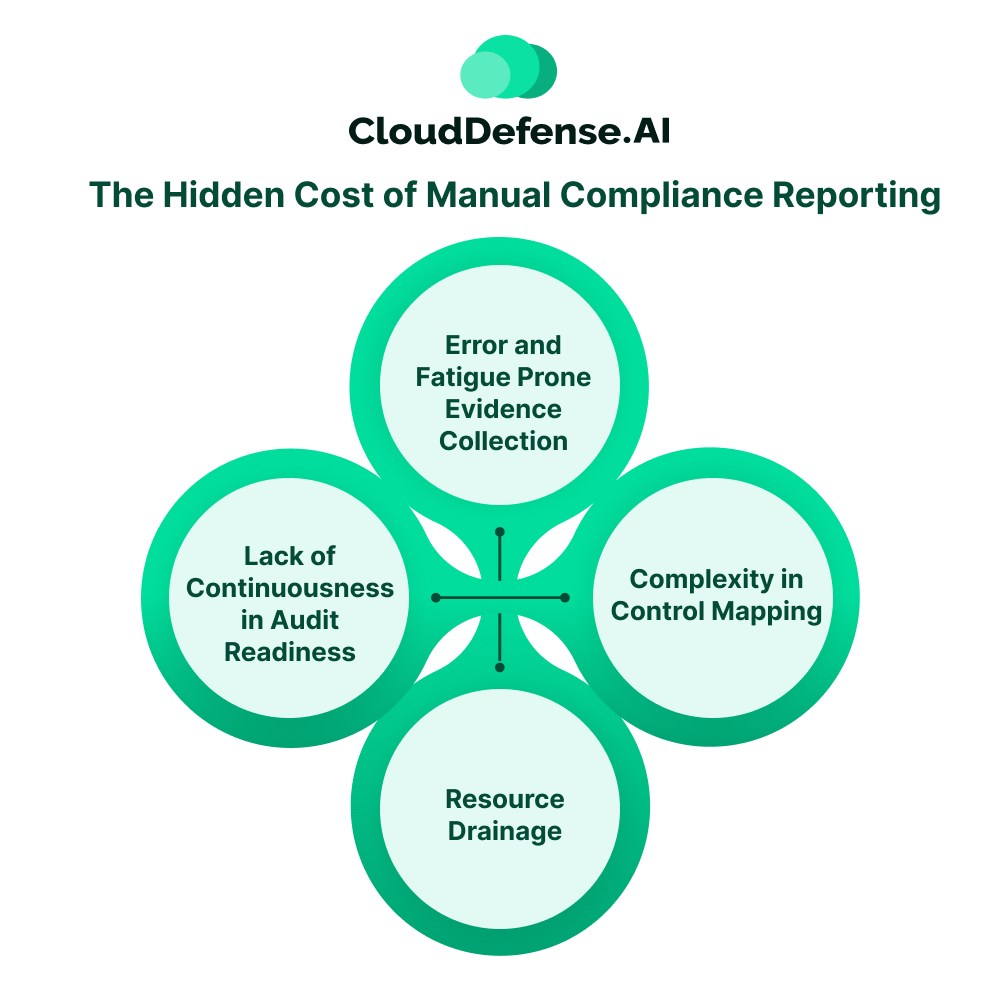
Traditional compliance workflow has been the backbone of most organizations. However, the journey to audit is filled with manual workflow- gathering evidence, mapping findings, and creating reports.
However, in today’s high-velocity development approach, the manual process is no longer sufficient because:
- Error and Fatigue Prone Evidence Collection: Traditionally, compliance teams have to collect screenshots, collect security logs, get CSV files, and perform other tasks to maintain compliance. Not only is this process labor-intensive, but also time-consuming, which often stretches up to 12 weeks for audit preparation. Moreover, manual evidence also leads to data staleness, where data acquired during collection may not highlight the same control state during audit.
- Lack of Continuousness in Audit Readiness: Most enterprises follow a yearly or half-yearly compliance program where audits take place after 6 months or at the end of the year. Since these traditional programs lack any continuous audit readiness, the compliance posture starts deteriorating once the audit is over. Lack of strict control, policy lapses, and misconfigurations create gaps in the compliance program that go unnoticed until the preparation for the next audit.
- Resource Drainage: A significant issue with manual compliance reporting is the resource drainage. To prepare for audits, security and development teams have to spend hours out of their work to gather evidence and prepare everything for the audit. It not only leads to the drainage of resources but also shifts the focus of teams from their productive work.
- Complexity in Control Mapping: Modern enterprises have to comply with numerous regulatory standards like GDPR, HIPAA, SOC 2, and others to perform their business. Every framework has its specific set of requirements and controls. To maintain compliance, teams have to manually map the controls and cross-reference the requirements. It is not only labor-intensive but also leads to redundancy and human errors.
QINA Pulse: The AI-Powered Security Co-Pilot for Automating Compliance Reporting
QINA Pulse is an enterprise-grade security tool that helps organizations with automated compliance reports and continuous monitoring. It serves as a central security system that automatically collects all the data from across the ecosystem and aggregates them for complying with different regulatory standards. A distinguishing aspect that gives Pulse the edge over others is the built-in compliance automation for all popular frameworks.
Using this tool, CISOs and GRC teams can generate and maintain audit-readiness for different frameworks with just simple English commands.
Key Capabilities of QINA Pulse for Compliance Automation
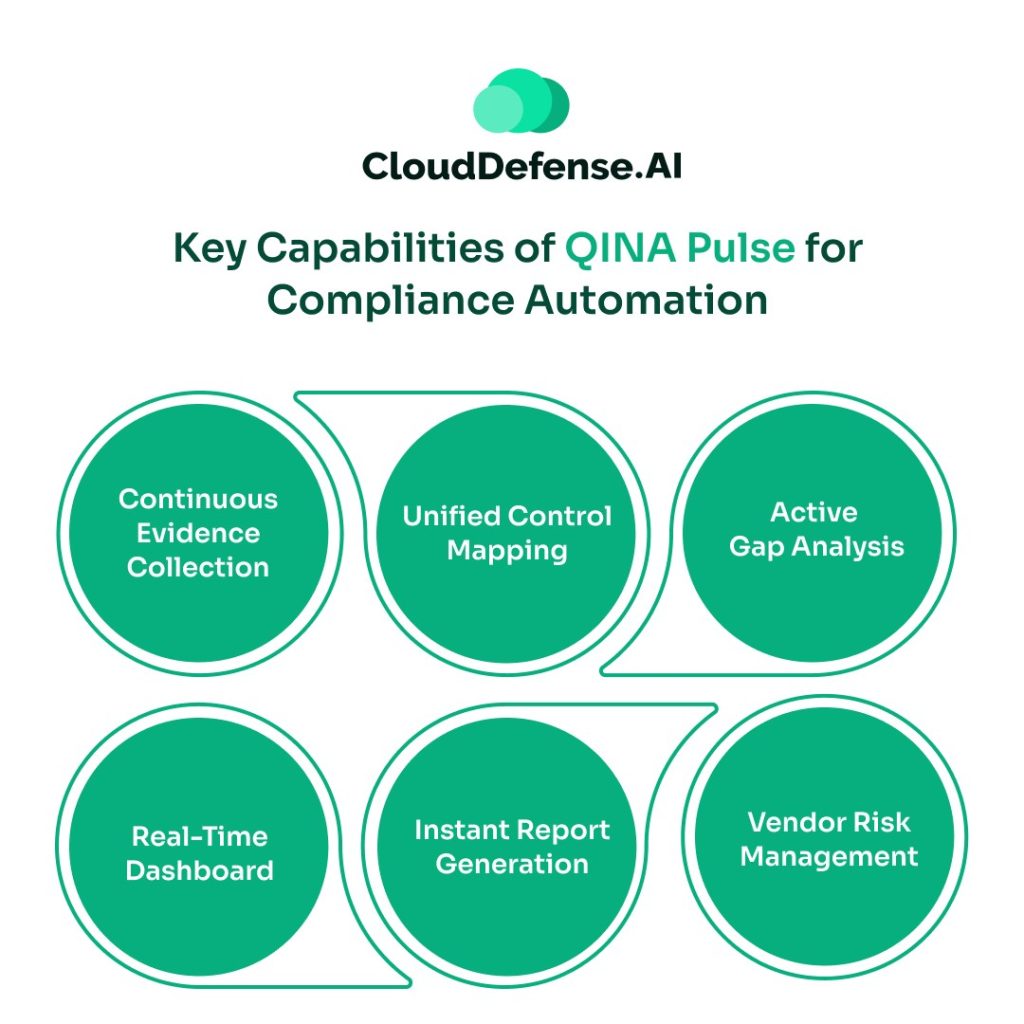
- Continuous Evidence Collection: QINA Pulse is built with SOC 2, PCI DSS, HIPAA, and many other compliance monitoring systems. Furthermore, the security assistant natively integrates with numerous enterprise tools, infrastructure stacks, and AppSec tools. This enables Pulse to pull compliance evidence continuously without requiring intervention.
- Unified Control Mapping: A significant aspect of Pulse is that it utilizes an intelligent control mapping process to map security findings to all the required regulatory frameworks. It maintains a single control implementation that adheres to the requirements of all standards simultaneously.
- Active Gap Analysis: What makes this security co-pilot stand out from others is its capability to perform automated gap analysis. Pulse, with the help of AI and LLM, compares the current state of the data storage, business stage, and overall security against the specific regulatory requirements.
- Real-Time Dashboard: Pulse provides all the teams and stakeholders in the enterprise with a real-time dashboard to get a complete overview of the compliance posture. The dashboard allows teams to collaborate and work on the reports of the gap analysis to ensure an optimum compliance posture.
- Instant Report Generation: It holds the capability to generate compliance reports along with executive summaries within a few seconds. All the teams have to do is just command Pulse to generate them, and it will deliver the report in the dashboard instantly.
- Vendor Risk Management: Through command, Pulse enables teams to automate the process of third-party risk management. It plays a significant role in maintaining compliance from the vendor end without affecting the overall operation.
How QINA Pulse helps with Automated Compliance Reports
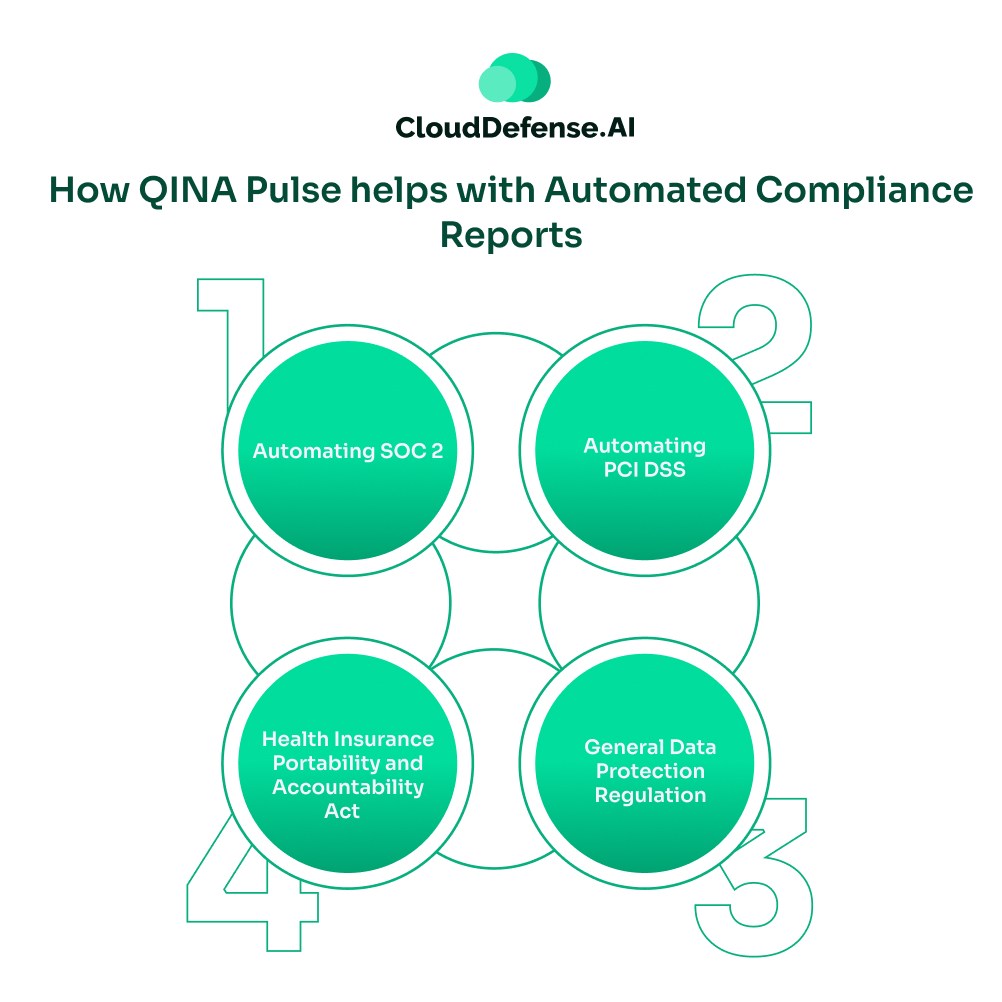
QINA Pulse is designed to help teams generate compliance reports automatically and maintain adherence to all regulatory standards.
But how does it generate automated compliance reports? Let’s find out:
Automating SOC 2
SOC 2, or System and Organization Control 2, is a global compliance standard that evaluates how an enterprise manages customer data. SOC 2 is conducted by the AICPA, and the evaluation of the services is based on
- Security
- Availability
- Processing integrity
- Privacy
- Confidentiality.
During Type 1 evaluation, only the control design at a specific time is assessed. However, the Type 2 evaluation assesses the operational effectiveness over a long period of time.
Pulse automates the process of monitoring common criteria controls, which includes tracking of unauthorized access attempts and a trail of security alerts along with system changes. Furthermore, it tracks authentication enforcement, incident detection & response, encryption, and many other aspects. It maps all the common criteria controls to technical controls to ensure continuous evolution.
QINA Pulse also automatically ingests log data from security controls, encryption audits, SIEM alerts, pull request approval, access review logs, and many sources. This provides active visibility in policy enforcement to ensure real-time adherence to SOC 2.
Automating PCI DSS
Payment Card Industry Data Security Standard is a widely followed standard from PCI SSC that requires organizations to maintain stringent security in the payment environment. Every enterprise that is storing, processing, and handling customers’ financial or payment data has to adhere to the PCI DSS standard.
QINA Pulse helps organizations to continuously and seamlessly adhere to all the requirements through automated compliance reports. Pulse ensures every organization maintains compliance with the six primary control objectives of PCI DSS:
- Protection of account data.
- Maintenance of a secure system and network.
- Implementation of a vulnerability management program.
- Continuous monitoring and testing of all networks.
- Enforcement of access control measures.
- Creating and maintaining an information security policy.
Pulse integrates with asset control and network mapping systems to track and maintain Cardholder Data Environment scoping with a complete auditable trail. Moreover, Pulse performs automated assessments on the environment to identify misconfigurations and patch them immediately to prevent exposure of customer card data.
Enterprises also benefited from the streamlined evidence collection that Pulse has on offer. It automatically collects scanning rules, role assignment logs, SIEM alert data, least-privilege access reports, and many other data for automated compliance reports.
Besides, QINA Pulse also helps organizations with automated compliance reports and audit automation for other security standards.
Health Insurance Portability and Accountability Act
HIPAA is a primary regulatory standard that is followed by organizations associated with handling and storing of Protected Health Information. It doesn’t require organizations to follow preset technical implementation; rather, it provides a standard to protect sensitive data.
It also requires organisations to maintain complete data flow visibility and ensure constant tracking of IAM to ensure strict authorized access to sensitive data. Importantly, Pulse also constantly monitors and verifies the encryption of patient data at rest and in transit, and adheres to the security standard. Through this security tool, teams can also automate the process of annual risk assessment and pulling of vendor risk records for a structured risk report.
General Data Protection Regulation
GDPR is a globally recognized standard that requires organizations to follow a privacy by design standard. Every organization that processes and stores EU residents’ data is required to follow stringent requirements like law processing of data, data protection by design, logs of processing activities, data subject rights, etc.
QINA Pulse enables organizations to maintain all the requirements through automated data mapping and maintenance of RopA. Furthermore, this security assistant also helps with the automated workflow of data subject requests that involves tracking and routing of requests within 30days.
Implementing QINA Pulse for Automated Compliance Reports
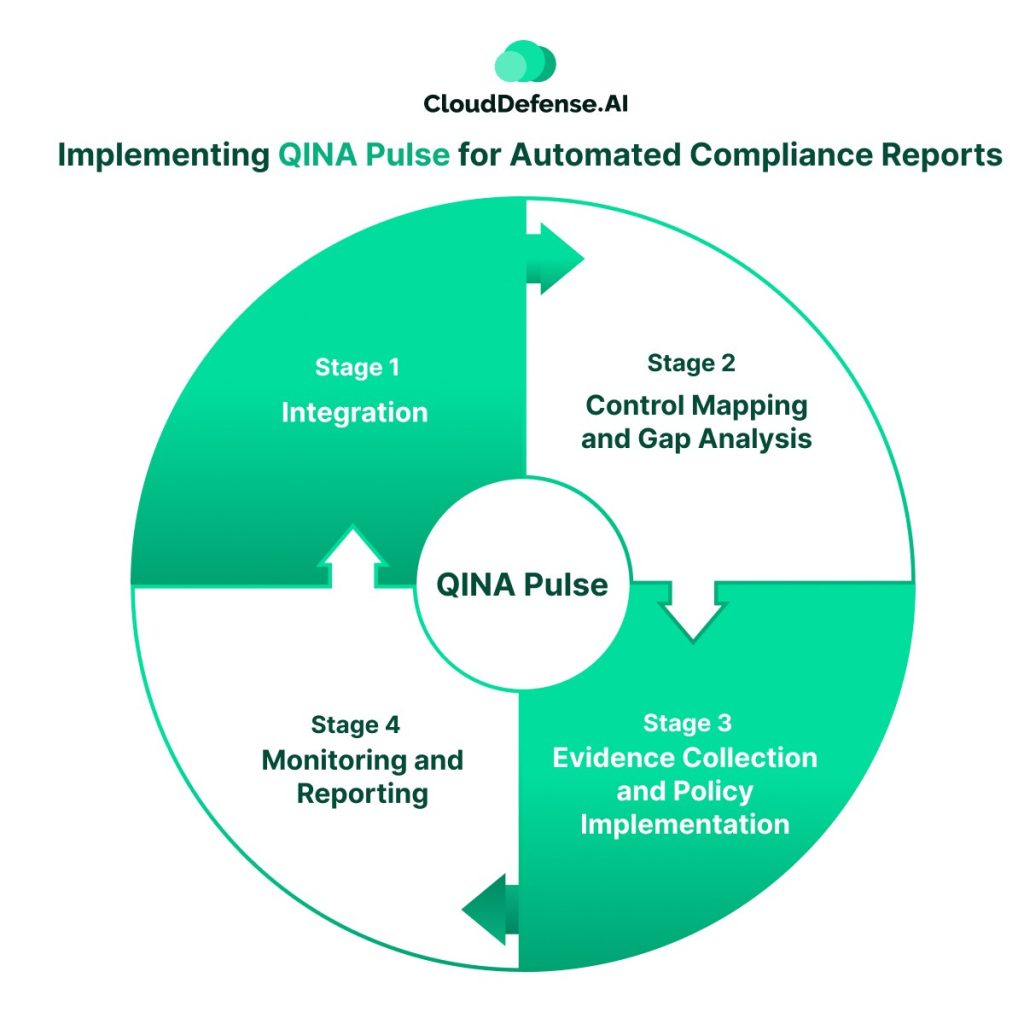
To seamlessly implement QINA Pulse for PCI DSS or SOC 2 report automation, enterprises need to go through four stages of the implementation process:
- Stage 1: Integration- The first step to implement QINA Pulse starts with automated integration and asset discovery. Pulse is designed to natively integrate with 50+ enterprise tools. Most importantly, it also connects with the existing tool stack, which includes security tools, cloud stack, DevOps, and SaaS apps.
- Step 2: Control Mapping and Gap Analysis- Once the integration process is complete, QINA Pulse looks for the target framework. The security co-pilot performs a gap analysis to create a pre-mapped control library. It not only highlights the mapped controls but also the gaps that need to be addressed. The tool produces a detailed analysis report for the team.
- Step 3:Evidence Collection and Policy Implementation- The security and compliance teams need to command Pulse to create automated compliance reports through continuous evidence collection. Once automated, this security assistant will automatically collect evidence from all the sources, including security scans for audits. Meanwhile, the compliance teams need to align all the security policies with the tool and assign control owners. Furthermore, they also need to command Pulse to remediate the gaps that have been identified in the beginning.
- Stage 4: Monitoring and Reporting- After complement configuration, QINA Pulse starts working autonomously for all compliance tasks. It continuously collects evidence and validates it automatically without requiring any command. Automated compliance reports are generated at scheduled intervals, while any control failure triggers real-time alerts.
Bottom Line
In today’s era, where cyber threats are getting sophisticated, the regulatory scrutiny is getting more complex. Whether it is SOC 2, PCI DSS, or GDPR, managing all the compliance requirements manually is no longer efficient. QINA Pulse, with its automated compliance reports capability, transforms the complete compliance process. It upgrades the compliance approach from a reactive to a proactive and automated process.
Pulse is built with SOC 2, HIPAA, PCI DSS, and other vital regulatory standard compliance monitoring capabilities. Moreover, it benefits the team with automated gap analysis and evidence collection, which ultimately helps the enterprise to stay audit-ready beforehand. By turning compliance into an automated and continuous process, organizations can build a robust guardrail that prevents any compliance failure.






