Web App Security
The Ultimate Web App Security
Strengthen your web applications with CloudDefense.AI’s top-notch security solutions. Protect your digital assets, ensure buttery smooth operations, and maintain your reputation with our cutting-edge technology.

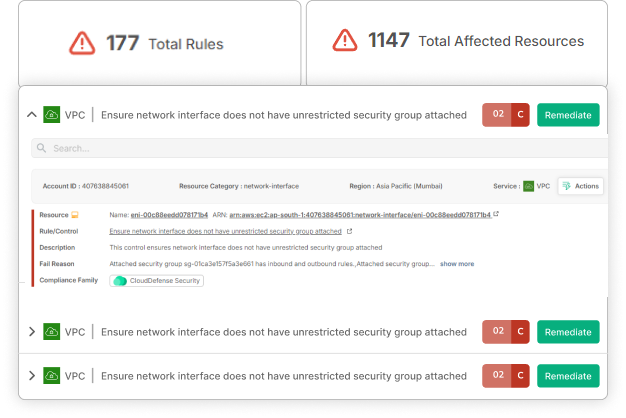
Cloud Security Risk Assessment
Find out which misconfigurations are lurking in your cloud
EMPOWER YOUR BUSINESS
One Solution, Complete Web App Security: Protect Your Applications Everywhere!
Say goodbye to vulnerabilities and protect your web applications against the most sophisticated threats. With CloudDefense.AI, your critical assets are protected, and your business remains resilient, no matter where risks emerge.

Comprehensive Web App Protection
Secure your applications across all environments—cloud, on-premises, or hybrid—with CloudDefense.AI’s unified platform.

Immediate Threat Minimization
Prevent security breaches with CloudDefense.AI’s real-time detection and response, stopping threats before they impact your operations.

User-Centric Interface
Effortlessly manage your application security with CloudDefense.AI’s intuitive platform, designed for both cybersecurity experts and beginners.
Your Retail Empire is Under Attack
Retail is a battlefield. Every day, cybercriminals target your business, ready to steal your hard-earned revenue and damage your reputation.
The Numbers Don’t Lie!
24%
You’re a Top Target
Retailers face a staggering 24% of all cyberattacks, making you a prime target for hackers.
-$250,000
The Price of Inaction
A single data breach can cost your business anywhere from $100,000 to $250,000. That’s money straight out of your bottom line.
20%
The Growing Threat
E-commerce security incidents have skyrocketed by 20% in just one year. The threat is real, and it’s escalating.
Can you afford to be a Casualty?
Don’t let these statistics become your reality. Protect your business, your customers, and your bottom line with our strong retail and e-commerce security solutions.
Our Holistic Approach to Web App Security
CloudDefense.AI’s approach to web app security integrates state-of-the-art technology, expert guidance, and continuous monitoring to defend your applications from threats, ensuring resilience and compliance.
Real-Time Threat Detection and Response
At CloudDefense.AI, we empower businesses with the tools to quickly identify and neutralize security threats within their web applications, transforming them into proactive and resilient organizations. Our platform’s intelligence-driven approach ensures effective and immediate protection.
Rapid Threat Reduction
Detect and eliminate security threats instantly, positioning your organization among the elite few capable of handling web app vulnerabilities with confidence.
Optimized Operations
Simplify your security processes and minimize downtime with our rapid threat detection and response framework.
Data-Driven Defense
Use intelligent data to stay ahead of threats and protect your applications proactively.
Competitive Security Edge
Stay at the forefront of cybersecurity by focusing on both prevention and quick recovery for lasting resilience.
Zero Trust Security Framework
Enhance your web app security with comprehensive, trust-free scans that identify and minimize risks before they can cause harm. CloudDefense.AI’s technology ensures foolproof protection against modern threats targeting your web applications.
Trust-Free Security
Eliminate vulnerabilities tied to trust dependencies, securing your web applications against sophisticated attacks.
Automated Threat Minimization
Strengthen your defenses automatically by minimizing common intrusion points and enhancing your security posture.
Transparency and Accountability
Provide stakeholders with assurance through verifiable internal checks and segregation of duties.
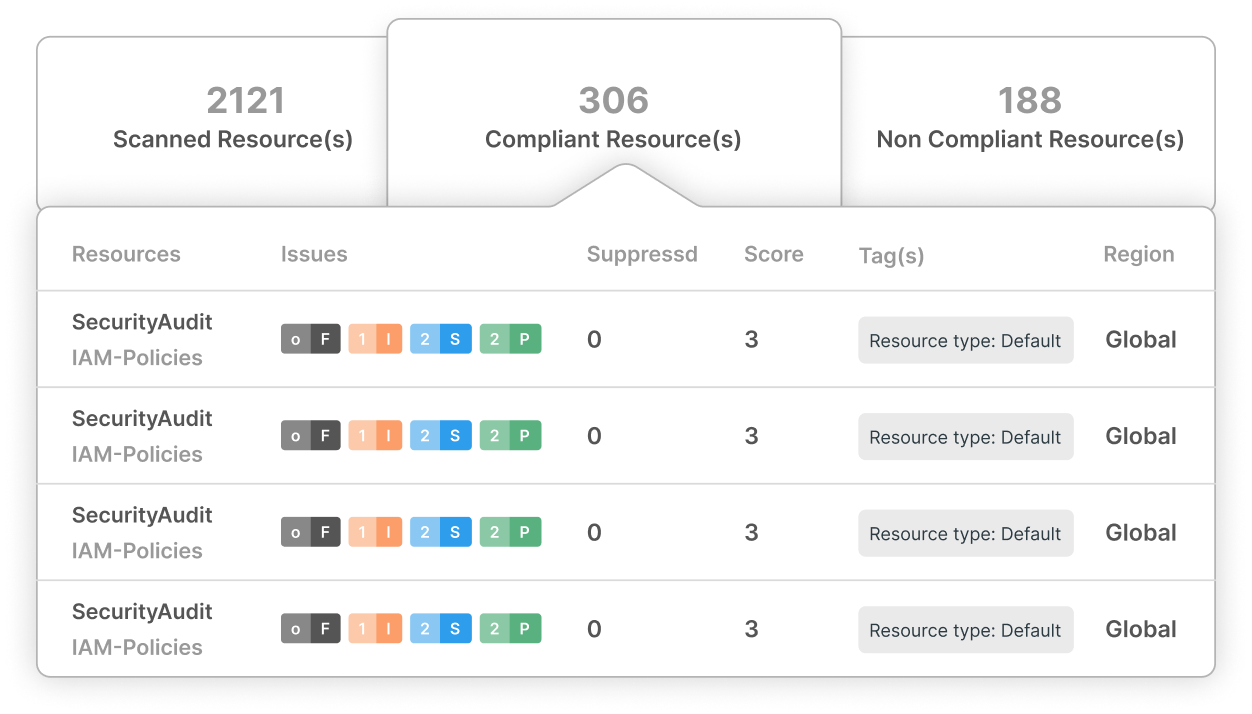
Made-Easy Compliance Management
Navigate complex regulatory requirements with ease using CloudDefense.AI’s compliance management tools. Our platform ensures your web applications remain compliant while securing against potential threats.
Effortless Compliance
Manage regulatory standards with our comprehensive Airtight Checklists, covering PCI DSS, FINRA, NYDFS, FERPA, HIPAA, GDPR, and CCPA.
Insightful Reporting
Access detailed, actionable reports that empower informed decision-making.
Priority-Focused Compliance
Identify and address compliance gaps effectively, optimizing time and resources.
User-Friendly Experience
Simplify compliance management with our intuitive platform, accessible to all levels of expertise.
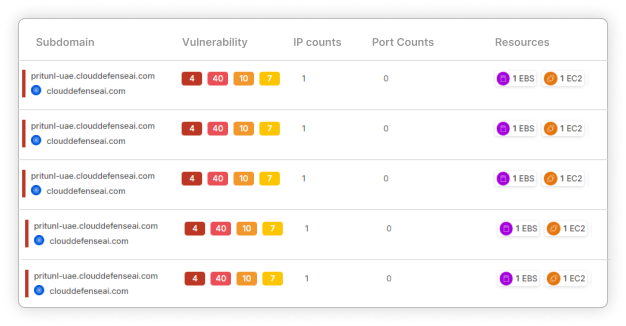
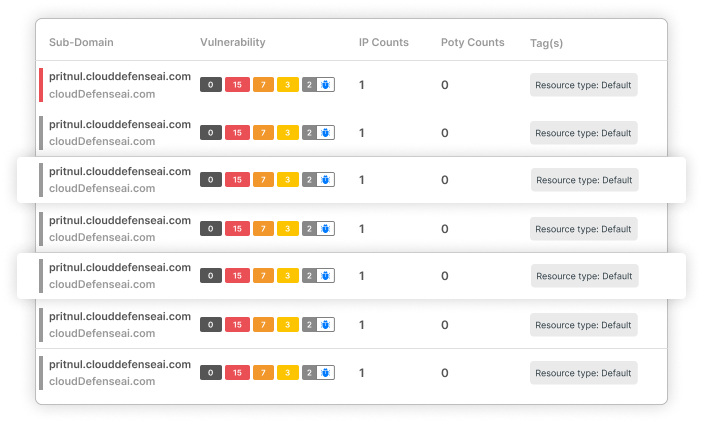
End-to-End Web App Protection
CloudDefense.AI provides rigorous security for your web applications by continuously monitoring and auditing all aspects of your digital infrastructure. Our SAST technology ensures ongoing vigilance and resilience against attacks.
Continuous Monitoring
Our SAST technology constantly scans for vulnerabilities, ensuring your web applications remain secure.
Comprehensive Protection
Establish a strong security perimeter from initial intrusion attempts to full remediation.
Proactive Web App Management
Stay ahead of potential threats with CloudDefense.AI’s proactive security measures, ensuring uninterrupted business continuity.
Experience Unrivaled Web App Security
Discover how CloudDefense.AI can enhance the security of your web applications. Join us for a live demonstration and see our protection in action.




