The number of security threats in the world is increasing at a rapid pace, and so is the volume of alerts. Even though modern cybersecurity has come a long way, development and security teams are still drowning in thousands of alerts. Most alerts are prioritized based on static rules, which are inefficient against modern cyberthreats.
As a result, teams must manually triage every alert—slowing down incident response and making security strategies fall short against machine-speed attacks. Organizations need to step up their incident management strategy with a smarter, more proactive approach.
This is where artificial intelligence (AI) steps in with intelligent security sorting. AI not only automates the incident prioritization process but also understands context, risk, and business impact. With AI-driven incident prioritization, teams can Prioritize Incidents Smartly, focusing on what truly matters instead of reacting to noise. For modern organizations, using AI for intelligent and faster incident prioritization is no longer a luxury—it has become a necessity.
This article explains how organizations can leverage AI-driven incident prioritization to Prioritize Incidents Smartly and respond to threats quickly and effectively.
The Crisis With Traditional Incident Prioritization
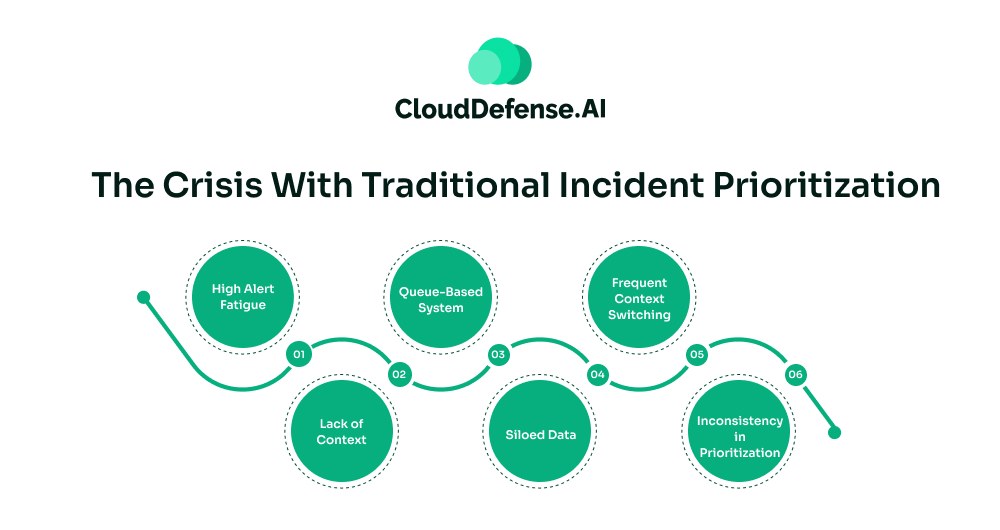
For years, enterprises have been relying on a traditional rule-based approach for prioritization and responding to incidents. However, the modern development environment involves microservices, public repositories, and numerous distributed components. The increasing complexity has made the approach inefficient.
The main crises with the traditional approach are:
- High Alert Fatigue: Traditional security scanners run on a rule-based approach, making it label every alert as an urgent issue. Moreover, the scanners and SIEMs generate alerts for every minor deviation. As a result, the development team receives thousands of alerts with “high priority” tags- drowning them in endless triage work.
- Lack of Context: Most legacy scanners and SIEMs analyse every alert based on preset patterns. These tools lack the contextual analysis needed to understand the business and developer’s intent behind any specific code. Due to this, these tools aren’t able to understand the severity of any vulnerability it has in the application.
- Queue-Based System: Even though many security dashboards have evolved, some of them still operate on modified first-in & first-out systems. The tickets are queued according to their arrival or other tags. Due to this, many major security threats are submerged under the long queue of monitor security hiccups. It not only diminishes the incident response time but also makes the application vulnerable.
- Siloed Data: Legacy tools during alert prioritization only utilize a definite set of patterns, without cross-referencing other data sources. Since these tools don’t cross-reference tools, many critical alerts are falsely prioritized as low priority due to unconnected events. However, when all the dots are connected, it tells the complete story: what happened, what has been affected, and how it is advancing.
- Frequent Context Switching: When teams manually triage and prioritize any alert, they have to frequently switch to different dashboards to find out about the vulnerability. It not only slows the prioritisation process but also makes it error-prone and delays the overall Mean Time to Remediate. Moreover, developers have to brainstorm about certain vulnerabilities that are not common to them.
- Inconsistency in Prioritization: Manual incident prioritization depends largely on the security expertise of the teams. In a team, especially in the development group, the security expertise varies from individual to individual. Thus, the priorities for security alerts are completely subjective and often inconsistent. The lack of sound knowledge on different types of threats makes the whole prioritization process inconsistent. As a result, it leads to misclassification of security alerts, which ultimately leads to missed threats.
AI-Driven Incident Prioritization: The Game Changer
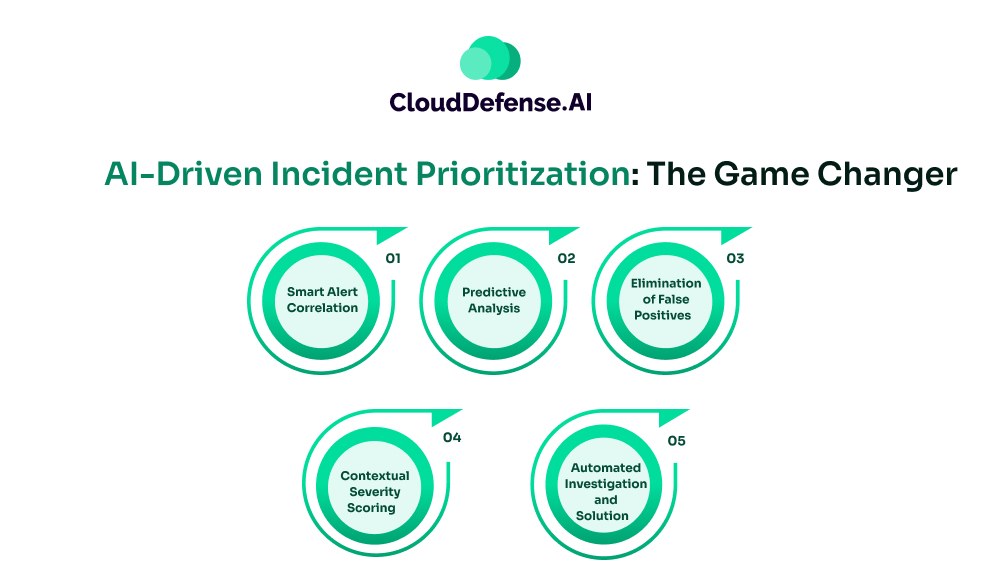
The integration of AI has revolutionised how development and security teams deal with incident prioritization. AI-driven incident prioritization moves beyond a standard rule-based approach; it leverages AI along with ML to understand threat coverage and business impact.
It looks at the “how”, “where”, and “why” of the security incident. Previously, only alert severity and threat tags were utilized for prioritisation, but modern AI agents go beyond it. From asset criticality to threat activity, it considers a lot of factors to accurately prioritize security incidents.
What makes the AI-driven incident prioritization a game-changer? Here are the main reasons:
Smart Alert Correlation
During AI-driven incident prioritization, the AI doesn’t show thousands of alerts for a similar incident. Rather, it recognizes all the similar patterns in the threats and merges them into a single alert. It correlates all the siloed data from different sources- logs and metrics, enabling the AI incident prioritization tool to identify the root cause.
It enables the teams to respond to the real cause, rather than responding to disparate low-priority threats of the same pattern. Importantly, it helps in identifying advanced threats, which are mostly identified through threat data correlation.
Predictive Analysis
Modern AI not only learns from live threat-data streams but also from historical databases. It continuously learns from varied threat databases and other vulnerable patterns affecting the code. This allows the AI to identify threats that are likely to amplify into larger anomalies.
Security analysts can respond to these threats and mitigate them before they turn into a high-impact vulnerability. AI completely analyzes the path and predicts the complete impact radius of the threat. It is highly useful for eliminating any major flaws in an application before the customer notices.
Elimination of False Positives
During smart security sorting, correlation of similar threat events helps the AI to merge them into one incident alert. Besides, the AI also checks the execution path of the vulnerable findings. It analyzes whether the vulnerable code makes an impact on the application. If it is dead code, then it quickly eliminates the vulnerable finding from the alert queue.
Contextual Severity Scoring
AI agents during AI-driven incident prioritizations go beyond technical severity scoring of high, medium, or low. It looks at the business logic, the developer’s code intent, historical data, and other contextual aspects. It performs contextual analysis on the vulnerable findings and understands their severity.
Based on all the context, it determines the severity scoring of each security incident. An incident affecting the customer-facing login process is tagged with a higher severity score than an incident that is found in the sandbox environment. All the dynamic scoring is done in real time.
Automated Investigation and Solution
Besides offering incident priority AI support, many AI-based tools also offer teams seamless investigation and easy-to-implement incident solutions. The AI agent automatically runs diagnostic commands, analyzes the incident, and provides tailored solutions for the specific incident to the team.
It usually provides them with a step-by-step guideline that enables the team to easily implement the fix. Many advanced AI-powered security tools not only help in automating the investigation process but also fix it.
QINA Pulse: The Next Generation AI-Powered Tool for Incident Prioritization
QINA Pulse is an excellent AI-powered security co-pilot that helps in faster response through AI-driven incident prioritization. Unlike other AI tools that offer AI-based prioritization to a certain degree, Pulse stands out with its context-aware smart security sorting process. It serves as a smart AI agent that understands your organizational requirements.
It offers a comprehensive solution for smart incident management, and that too using simple English commands. It not only helps developers with intelligently prioritised incident alerts but also filters out all the noise.
Importantly, the security assistant provides the team with a detailed suggestion on how to respond to the incident, often with a detailed code snippet. Thus, developers as well as security analysts can quickly respond to the incidents without facing any hassle. But what makes QINA Pulse different from other solutions?
Here are some vital reasons that have made the security co-pilot the finest choice for most enterprises:
- Context-Aware Triage: Most security assistants prioritize security incidents based on CVSS score. But Pulse goes beyond it by prioritizing the security incident based on the developer’s workflow, business logic, permission level, and many other aspects. This allows the security assistant to understand that a non-executable, flawed code is less critical than a security incident found in the payment gateway. In addition, it also utilizes advanced behavioural analysis to understand and predict the impact of the incident. This helps the tool in prioritizing the vital security incidents according to their impact level while eliminating false positives.
- Continuous Learning: QINA Pulse is always evolving. It is continuously learning from every security incident, fixes, feedbacks and emerging threat patterns from real-time data streams. It is able to identify nuanced and zero-day incidents that standard tools can’t identify. As a result, Pulse can refine its AI-driven incident prioritization logic and accurately prioritize security incidents. With Pulse, security and development teams can strategically manage and respond to security incidents before they make any impact.
- Workflow Orchestration: A significant aspect of Pulse is that it doesn’t operate in silo. It natively integrates with different IDEs, security tools, and AppSec platforms. It ingests all the data for better understanding and generates response to security incidents that coincide with the organization’s requirements. From triggering smart security sorting to automating incident response, it enables the team to orchestrate all incident management tasks from one place. Importantly, it also enhances shift-left integration and helps the developers to identify incidents at the earliest.
- Interaction in Natural Language: Pulse has simplified the incident management process by enabling teams to interact with the security assistant in plain English. Specialists, especially from the development team, won’t have to learn complex queries to initiate incident prioritization. This security assistant utilizes NLP to enable teams to give commands in plain language. It not only simplifies smart security sorting but also enhances incident response time.
Bottom Line
In this modern era, where cyber threats are evolving rapidly, organizations can no longer rely on a manual approach for prioritizing security incidents. The team doesn’t need to work harder but triage smartly to eliminate all the obstacles that cost money, time, and security.
AI-driven incident prioritization is the need of the hour for all enterprises. It can handle all the heavy lifting of smart security sorting- enabling teams to quickly respond to security incidents. With the adoption of AI-based incident prioritizations, teams can achieve:
- Improve MTTD and MTTR to minutes.
- Minimal false positive rate.
- Automated incident response.
The speed of the business is largely dictated by the speed at which organizations respond to security incidents. It is essential for organizations to adopt AI-powered incident prioritization to end the burden of massive alerts and start responding to threats at high velocity.






