What Is Alert Fatigue in Cybersecurity?
Alert fatigue in cybersecurity occurs when security teams become overwhelmed by a high volume of alerts generated by monitoring systems. This leads to desensitization, delayed responses, or even missed critical threats.
What It Does:
- Increases the likelihood of overlooking real security threats.
- Reduces the efficiency of cybersecurity teams.
- Wastes time on low-priority or false-positive alerts.
- Leads to burnout among security professionals.
- Weakens the overall security posture of an organization.
If your team can’t focus on what truly matters, your defenses are effectively down. Reducing alert fatigue means implementing smarter systems, automating low-risk tasks, and ensuring your team can act on the alerts that truly matter. It’s time to rethink how your organization approaches cybersecurity.
Why Is Alert Fatigue a Problem?
More than just an inconvenience—alert fatigue is a cybersecurity threat multiplier. When analysts are overwhelmed, critical issues are missed. This doesn’t just put data at risk; it jeopardizes the entire organization.
Here are some stats that show the real impact of alert fatigue:
- 83% of security professionals say their team experiences burnout due to alert fatigue.
- 45% of IT incidents are either ignored or responded to too late because of overwhelming alert volumes.
- The International Data Corporation estimates that cybersecurity teams at companies with more than 5,000 employees tend to ignore about 23% of their alerts.
Here’s why it’s a problem:
- Missed Critical Threats: Teams overwhelmed by constant alerts start to assume most are false positives, leading to real incidents slipping through undetected.
- Delayed Responses: Excessive alerts dilute focus, increasing the time it takes to react to genuine threats. This gives attackers more time to exploit vulnerabilities.
- Burnout in Security Teams: Analysts work long hours under immense pressure. Add alert fatigue, and you have a recipe for mistakes, turnover, and lower team morale.
- Resource Drain: Managing redundant alerts wastes hours and diverts resources from proactive security measures like threat hunting.
Every minute spent on a false alert is a minute attackers could use to breach your systems. Alert fatigue creates cracks in your defenses that can be exploited. Addressing it isn’t optional—it’s essential to building an effective cybersecurity strategy.
What Causes Alert Fatigue?
Alert fatigue doesn’t just happen out of nowhere. It’s a serious issue that comes from a combination of problems. Let’s be clear about what’s causing it—and why it’s a big deal.
Too Many Alerts
- Volume: Security tools are creating way too many alerts. A lot of these are unnecessary and simply add to the noise.
- False Positives: Roughly 50-60% of alerts turn out to be false alarms. Over time, this makes teams less likely to react when something real happens.
No Clear Prioritization
- Lack of Severity Ranking: Alerts come in without clear rankings of importance. Everything gets treated the same, which means the critical issues get buried under less important ones.
- Multiple Tools: Using too many tools leads to duplicate alerts. This only increases the confusion and makes it harder for teams to stay focused.
Staffing and Resource Issues
- Understaffed Teams: Security teams just don’t have enough people to handle all the alerts. This slows things down and leads to burnout.
- No Automation: Without automation, teams have to deal with every alert manually. This eats up time and makes everything more difficult.
Complex IT Environments
- Cloud and Multi-cloud Systems: More cloud and hybrid systems mean more alerts. It’s harder to track everything, and more alerts come in from every angle.
- Old Systems: Legacy systems still in play can trigger excessive alerts. These systems don’t always work well with newer tech, which creates more noise for the team.
Lack of Effective Cloud Security Solutions
- No Noise Reduction: Many cloud security solutions don’t have the capability to reduce noise. This means teams are flooded with irrelevant alerts.
- Poor Reporting: Without proper reporting and clear analysis, it’s impossible to make sense of all the alerts. This makes it even harder to take quick action when needed.
Alert fatigue happens when there are too many alerts, no way to prioritize them, not enough resources, and old or ineffective systems in place. If you want to fix it, you need smarter tools that focus on what really matters and give your team the resources to act fast.
The Consequences and Risks of Alert Fatigue
When security teams are overwhelmed by constant alerts, real security threats get lost in the noise. Let’s break down what’s at stake:
1. Missed Threats Lead to Major Breaches
Alert fatigue is causing security teams to ignore or overlook real threats. When you have 17,000 malware alerts per week and only 19% are reliable, it’s no surprise some critical issues are missed. This leads to breaches that could have been prevented. In 2022, the cost of a data breach hit an average of $3.86 million. That’s a massive price to pay because of missed alerts, and it’s a direct result of alert fatigue.
2. Delayed Response Time Drives Costs Up
It’s simple: the longer a breach goes undetected, the more damage it causes. The Ponemon Institute found it takes an average of 280 days to identify and contain a breach. That’s 277 days of hackers doing damage, stealing data, and increasing the cost of the breach. Alert fatigue makes this problem worse. Delays add millions to the final cost, and we can’t afford that kind of risk.
3. Financial Losses Skyrocket
Alert fatigue is driving up costs in a big way. The longer a breach stays hidden, the more it costs. This doesn’t just hurt the bottom line—it can destroy a business. Alert fatigue is a key reason breaches are more costly than ever. It’s time to take action and fix it.
4. Wasted Resources on False Alerts
Security teams are wasting too much time on false alerts—30% of them go uninvestigated. That’s hours and resources spent on things that don’t matter. Instead of focusing on real threats, teams are burning out, making mistakes, and letting vulnerabilities slip by. Time and money are being lost because the alert system is broken, and it’s getting worse.
5. Burnout Leads to High Turnover
Security teams are getting burned out. When analysts deal with nonstop alerts, it leads to stress and exhaustion. They miss important issues, and they start leaving. This creates a huge gap in the team, and your security gets weaker. Alert fatigue causes a high turnover rate, and this leaves organizations exposed. We need to fix the problem before it becomes a bigger issue.
How to Reduce and Prevent Alert Fatigue
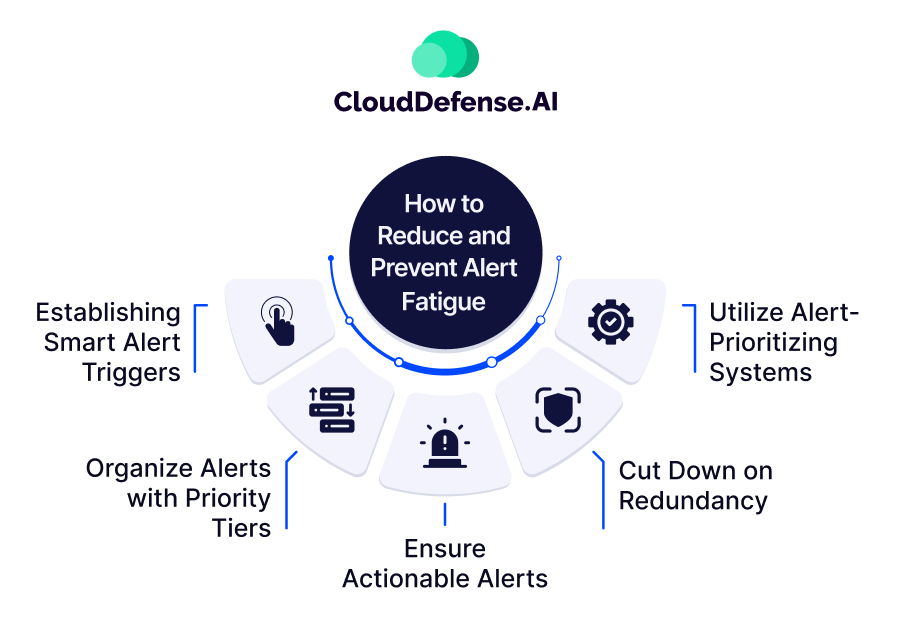
1. Establish Smart Alert Triggers
It’s crucial to set proper thresholds for alerts. Not every alert needs immediate attention. Take login attempts—should every single failure trigger an alert? No. Instead, set a threshold to notify you only after multiple failed attempts. This way, you can spot real threats, like a potential brute-force attack, without being bombarded by minor events. When alert triggers are set smartly, security teams focus on what matters, reducing the constant flood of notifications that lead to burnout.
2. Organize Alerts with Priority Tags
It’s crucial to prioritize alerts. Not every alert needs to be acted on right away. Some issues can wait, and others need immediate attention. Create a system where the most critical problems—like an intrusion—are addressed first, and the less urgent things can wait. This keeps your team focused on what really matters. Prioritizing alerts is one of the most effective ways to prevent alert fatigue.
3. Ensure Actionable Alerts
Your alerts need to be clear and useful. If an alert is just a generic message like “Suspicious Activity Detected,” it’s not helping your team make decisions. Make sure your alerts include important details: which system is affected, what’s happening, and what needs to be done. This helps your team act fast and with confidence. Without clear information, you’re wasting time, and time is critical.
4. Cut Down on Redundancy
Don’t let your team get overwhelmed by duplicate alerts. If two systems report the same issue, treat it as one. This simplifies everything. It saves time, and it saves your team from getting bogged down in repetitive alerts. The key here is efficiency—cut the redundancy and make sure your team only gets the alerts they need.
5. Utilize Alert-Prioritizing Cloud Security Solutions
Take advantage of modern tools like CloudDefense.AI to handle alerts more effectively. These tools help prioritize alerts based on their context and severity. Instead of sorting through noise, your team can focus on what really matters. CloudDefense.AI is changing the way alerts are managed, ensuring that your security team can do their job without getting overwhelmed. It’s a big win.
How CloudDefense.AI Helps
1. Effective Risk Prioritization Tags
CloudDefense.AI automatically assigns risk levels to alerts using clear, actionable tags: Critical, High, Medium, and Low. This allows your team to immediately understand the severity of an issue. When you’re dealing with thousands of alerts, these tags help ensure that critical threats are dealt with first, avoiding wasted time on less important events. The system prioritizes what matters, keeping your focus sharp and your response times fast.
2. Low False Positives
False positives are a major contributor to alert fatigue, but CloudDefense.AI keeps them to a minimum. Its advanced algorithms analyze alerts more accurately, reducing the number of irrelevant notifications. This means your team isn’t wasting time investigating things that aren’t real threats. By minimizing false alarms, CloudDefense.AI lets your team focus on what truly matters, reducing burnout and improving overall efficiency.
3. Auto Remediation
CloudDefense.AI can automatically address certain threats without needing manual intervention. This automation speeds up your response time and frees up your team to focus on more complex issues. For example, if a known threat is detected, the system can take predefined actions to mitigate it, like blocking a malicious IP address. This reduces the chance of human error and ensures rapid response to threats.
4. Attack Path Analysis
CloudDefense.AI goes beyond just detecting threats—it helps you understand the full attack path. By mapping out how an attacker might move through your system, the tool helps identify potential weak points and attack vectors before they’re exploited. This proactive approach gives your team a deeper understanding of the security landscape and allows them to prevent threats before they become critical.
5. Continuous Monitoring
Security threats don’t pause, and neither should your monitoring system. CloudDefense.AI offers continuous, real-time monitoring, ensuring that no threat goes unnoticed. This always-on protection keeps your infrastructure safe 24/7, so your team doesn’t have to play catch-up. With round-the-clock monitoring, CloudDefense.AI ensures that your security posture remains strong, day in and day out.
6. Integration with Existing Systems
CloudDefense.AI integrates seamlessly with your current security tools, creating a unified security ecosystem. This ensures your existing infrastructure is enhanced, not disrupted. Instead of introducing more complexity, it works with what you already have, strengthening your overall security posture without the need for an entire overhaul. It’s a smart, efficient way to enhance your cybersecurity strategy.
Conclusion
This guide should have helped you understand what is alert fatigue, its impacts, and how to overcome them. In the battle against alert fatigue, a quick fix just won’t cut it. We need a proactive approach that tackles the core principles outlined above. The statistics reveal that security staff invest around 30 minutes in each actionable alert, with an additional 32 minutes spent pursuing false leads, underscoring the real impact of alert fatigue.
Astonishingly, companies within the bracket of 500-1,499 employees neglect or overlook 27% of all alerts, revealing a vulnerability that demands attention. As we navigate this complex terrain, it is crucial to adopt proactive measures—setting intelligent thresholds, prioritizing alerts judiciously, and integrating advanced solutions like CloudDefense.AI that tackle alert fatigue.
In doing so, we not only enhance our defense mechanisms but also protect against the threat of alert fatigue, ensuring that each response is swift, targeted, and strengthened against potential breaches.
FAQ
What is a false positive?
In the cybersecurity realm, a false positive is when your security system accidentally raises an alert. It happens when the system thinks there’s a threat, but in reality, it’s just a false alarm. It’s akin to an overzealous security guard mistaking normal activity for something malicious. This hiccup usually occurs due to overly touchy security settings or glitches in the detection algorithms, and if not handled properly, it can lead to an overflow of unnecessary alerts.
What are the types of alerts in cyber security?
Cybersecurity alerts come in all shapes and sizes, each one waving a flag for different potential security issues. You’ve got your intrusion detection alerts, signaling potential unauthorized access; malware detection alerts, shining a spotlight on malicious software; and anomaly alerts, pointing out anything fishy. Then there are vulnerability alerts, highlighting system weaknesses, and compliance alerts, giving you a heads-up about broken security policies or regulations.
What is a fatigue warning?
Consider a fatigue warning in cybersecurity like your computer saying, “Hey, heads up, you might be burning out on alerts!” These warnings act as a reminder for security teams to reevaluate and fine-tune their alerting systems. The advice might include tweaking alert thresholds, adopting better prioritization methods, or integrating tech that fends off the less-than-ideal consequences of alert fatigue, such as being less responsive to critical incidents or facing an increased risk of security breaches.







