API SCANNING
Hassle-Free API Security for Robust Application Security
Our seamless API security solution empowers organizations to proactively safeguard their applications by swiftly identifying and mitigating API misconfigurations and vulnerabilities.
Cloud Security Risk Assessment
Find out which misconfigurations are lurking in your cloud
API SCANNING
Redefining Security Standards: Our Optimized API Scans are Aligned with OpenAPI Specifications
Unparalleled Coverage
Gain an all-encompassing perspective of your application ecosystem’s API attack surface, leaving no room for vulnerabilities, even with newly added assets.

Strategic Risk Management
We offer in-depth API vulnerability insights that help you in assessing potential risks. We provide you with CWE numbers and categorize vulnerabilities as critical, high, medium, or low, keeping you steps ahead of potential dangers.
Fast and Precise

Unite Your CI/CD Pipeline
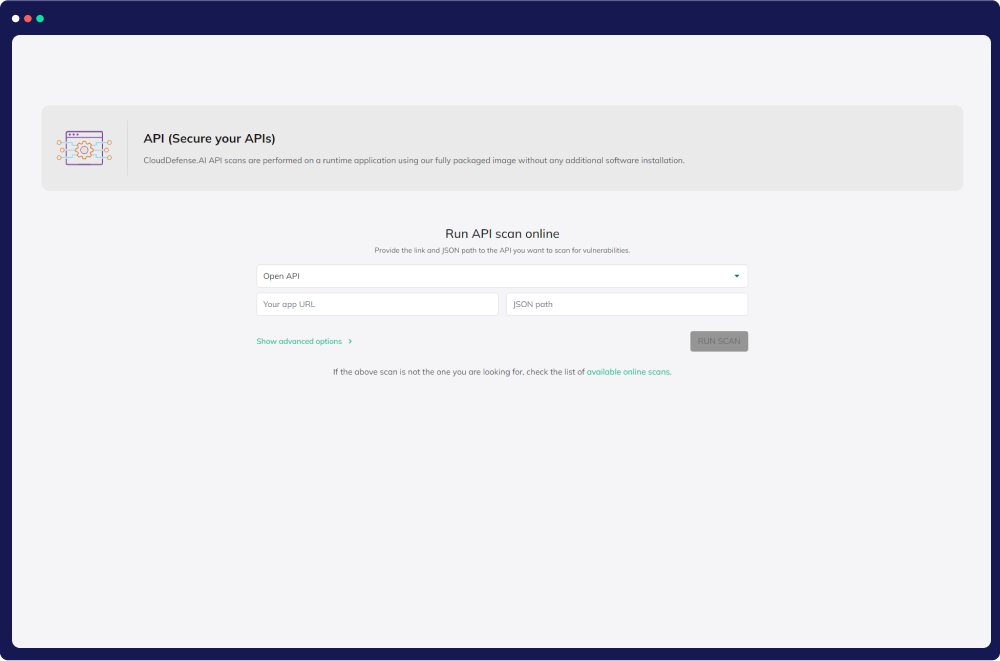
Our Comprehensive Approach to Analyzing APIs for Vulnerabilities
Revolutionize API security with our lightning-fast, agent-free approach. We deliver comprehensive API analysis, strategic risk management, and seamless CI/CD integration, ensuring your digital assets remain protected
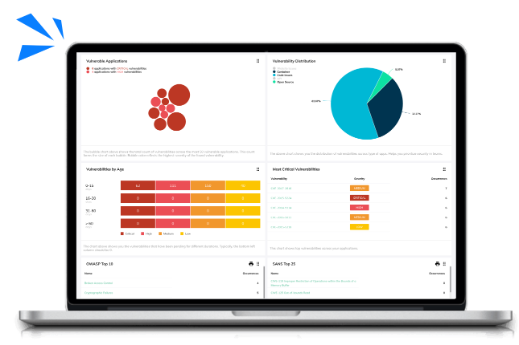
API Security Insights
Monitor, and secure your APIs effortlessly with CloudDefense.AI. Gain real-time insights into your API assets and endpoints, empowering your team to protect your applications seamlessly.
Comprehensive Vulnerability Discovery
Uncover vulnerabilities across your APIs comprehensively. Our advanced scanning tools pinpoint weaknesses, ensuring rapid and effective security improvements.
CWE Number
Get insights into CWE numbers on your dashboard. CWE (Common Weakness Enumeration) is a standardized list of common software weaknesses and vulnerabilities that help organizations identify, understand, and mitigate potential security issues in their software applications.
Vulnerability Severity Prioritization
Easily classify vulnerabilities as critical, high, medium, or low. This empowers you to proactively address potential threats, ensuring efficient security prioritization.
Interactive MAPS API
Explore interactive maps revealing all API endpoints, requests, and server responses for comprehensive insights.
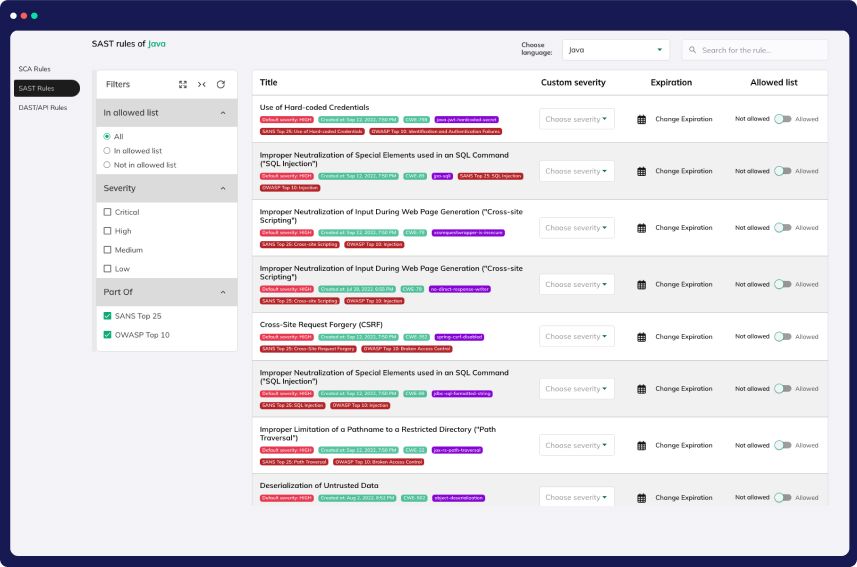
OWASP Top 10 Protection and Beyond
At CloudDefense.AI, we simplify web application and API protection in mixed environments. Our solution provides versatile deployment choices with support for customizing protection against OWASP Top 10 and SANS Top 25 vulnerabilities.
Comprehensive OWASP Top 10 Protection
Safeguard your web applications from critical security risks, including broken authentication, cross-site scripting, and code injection.
Be Compliance Ready
Our adherence to OWASP standards ensures that your applications meet industry best practices and compliance requirements, mitigating legal and regulatory risks.
Continuous Updates
We stay up-to-date with the evolving OWASP guidelines, guaranteeing that your security measures remain effective against emerging threats in real-time.