Well, they're both about making software development faster and better, but there's a key difference. In this article, we'll look at how DevOps vs DevSecOps differs and what that means for developers and companies.
Understanding DevOps and DevSecOps
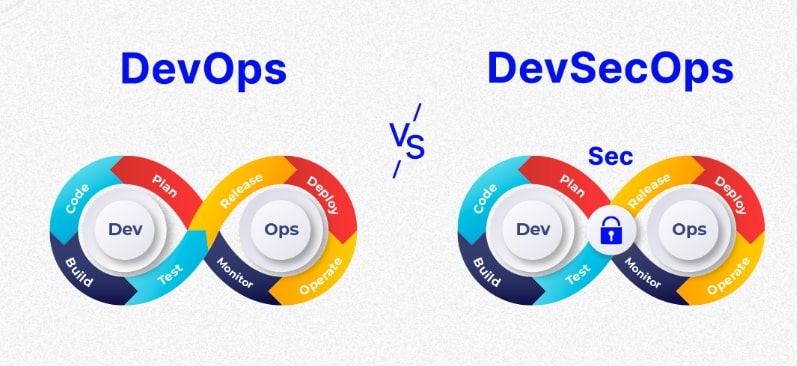
Let’s break down what DevOps and DevSecOps really mean. These concepts are crucial in the tech world today, especially for teams looking to enhance their software development processes.
DevOps is all about developing collaboration between development and operations teams to improve efficiency. Here’s what you need to know:
- Collaboration: Think of DevOps as a bridge between developers and IT operations. It’s all about getting these teams to work closely together, sharing knowledge and goals.
- Speed and Quality: The ultimate aim? To deliver software faster without compromising on quality. It’s a delicate balance, but it’s crucial in today’s fast-paced world.
- Culture Shift: Adopting DevOps means embracing a culture where open communication and collaboration are key. No more working in silos—everyone is in this together!
- Continuous Improvement: With practices like continuous integration and continuous delivery (CI/CD), DevOps teams can roll out updates and improvements regularly, keeping things fresh and relevant.
Now, let’s switch gears and talk about DevSecOps. This is where things get even more interesting:
- Security Integration: DevSecOps takes the principles of DevOps and adds a vital ingredient—security. It’s about making sure security is part of the conversation from day one, not something you think about at the end.
- Proactive Measures: The beauty of DevSecOps is its proactive approach. By identifying potential vulnerabilities early in the development process, teams can address issues before they become headaches down the line.
- Compliance Assurance: Staying compliant with industry regulations is no easy feat, but DevSecOps helps organizations weave security checks into their workflow, making compliance less of a chore. By aligning with frameworks like the NIST Cybersecurity Framework, PCI DSS, and CIS Controls, organizations can ensure security is built into the development process from the start, turning it into an ongoing priority rather than an afterthought.
- Holistic Approach: In DevSecOps, security is everyone’s responsibility. This holistic view fosters a shared commitment to keeping applications safe and sound.
So, how does DevOps Differs from DevSecOps?
Okay, now let me explain this with a real-world scenario:
Imagine you’re working at a company that makes a popular mobile app. Let’s call it “QuickShop” – it’s an app where people can buy groceries and have them delivered.
In a traditional setup, you might have:
- The dev team writing code for new features
- The ops team managing the servers and making sure the app stays up
- The security team checking for vulnerabilities after everything’s done
With DevOps, things start to improve. The dev and ops teams work more closely, and they use tools to automate many processes. Now, when the dev team adds a new feature—let’s say, a way to schedule future deliveries—they can push it out faster. The ops team was involved earlier, so they’re ready to scale the servers if the feature is a hit. Everything moves quicker, and there’s less friction between teams.
But here’s the thing – security is still kind of separate. They might only check things at the end, which can lead to delays if they find issues.
This is where DevSecOps comes in. Now, security is baked into every step:
- When the idea for the scheduled delivery feature comes up, someone’s already thinking, “How do we keep this secure?”
- As developers write the code, they’re using tools that automatically check for common security issues.
- The ops team will set up the infrastructure with security in mind from the start.
- Everyone in the team gets some basic security training, so they’re all thinking about it.
- Security tests are run automatically alongside other tests, so problems are caught early.
- If a security issue does come up after release, the whole team is ready to respond quickly.
The result? The new feature gets out just as fast (or maybe even faster), but it’s a lot more secure from the get-go. And if some hacker tries to mess with your scheduled deliveries, you’re in a much better position to catch it and fix it fast.
This is the real difference between DevOps vs DevSecOps. It’s not just about adding a security team to the mix. It’s about making security a part of everyone’s job, at every stage. It’s a mindset shift that can make a huge difference in how safe and reliable your software is.
DevOps vs DevSecOps: The Similarities
When you look closely at DevOps vs DevSecOps, you’ll find they share a lot of common ground, making them both valuable frameworks in the software development lifecycle.
Here’s a breakdown of their similarities:
| Aspect | DevOps | DevSecOps |
| Collaborative Environment | Promotes teamwork between developers and operations to optimize processes. | Expands collaboration to include security teams, fostering a culture of shared responsibility. |
| Focus on Automation | Advocates for automating testing and deployment tasks to enhance efficiency. | Integrates security automation, including vulnerability scanning, to ensure secure processes. |
| Continuous Integration and Delivery | Utilizes CI/CD pipelines for faster software releases and updates. | Incorporates security checks into CI/CD processes for safer deployments. |
| Cultural Transformation | Encourages a culture of shared ownership and transparency among teams. | Requires a cultural shift that emphasizes security awareness and collective collaboration. |
| Efficiency in Delivery | Aims to accelerate time to market by streamlining operations. | Shares this goal but includes security measures to ensure compliance and resilience. |
| Responsibility Across Teams | Encourages collective responsibility for quality and performance. | Extends this to include security, making it a shared duty throughout the SDLC. |
| Feedback Loops | Emphasizes iterative feedback for continuous improvement. | Incorporates security feedback into the development cycle, allowing for quicker adjustments. |
DevOps vs. DevSecOps: The Differences
DevOps vs DevSecOps both aim to boost software development, but they go about security in pretty different ways. DevOps is all about getting dev and ops teams to work together and crank out code quickly. The downside? It often overlooks solid security, treating it like an afterthought instead of something that needs to be built in from the get-go.
For instance, a DevOps crew might rush to launch their software and then realize they’ve left themselves wide open to vulnerabilities because they waited too long to test security. In contrast, DevSecOps makes sure security is part of the conversation from day one, embedding it into every step of the development process.
Here’s a breakdown of their differences:
| Aspect | DevOps | DevSecOps |
| Security Emphasis | Focuses primarily on speed and efficiency without rigorous security checks. | Prioritizes security throughout the software development lifecycle. |
| Security Practices | Security is often considered at the end of the development process. | Integrates security practices from the start to prevent vulnerabilities. |
| Responsibility | Security responsibility typically falls to a separate team post-deployment. | Promotes shared responsibility for security among all team members. |
| Risk Management | Risk assessment may be limited, leading to potential oversights. | Emphasizes proactive risk management and continuous security assessments. |
| Compliance | Compliance checks are often reactive and not embedded in the process. | Incorporates compliance measures into every stage of development. |
| Response to Threats | Reacts to threats post-deployment, which can lead to increased downtime. | Implements strategies to identify and address threats continuously. |
| Collaboration Depth | Collaboration mainly between development and operations. | Collaboration extends to security teams, creating a comprehensive team dynamic. |
| Tools and Practices | Utilizes CI/CD tools primarily for development and operations tasks. | Incorporates security tools for vulnerability scanning, monitoring, and compliance. |
| Feedback Mechanism | Feedback is often focused on development and operations performance. | Includes security feedback, ensuring security vulnerabilities are addressed promptly. |
Transitioning from DevOps to DevSecOps
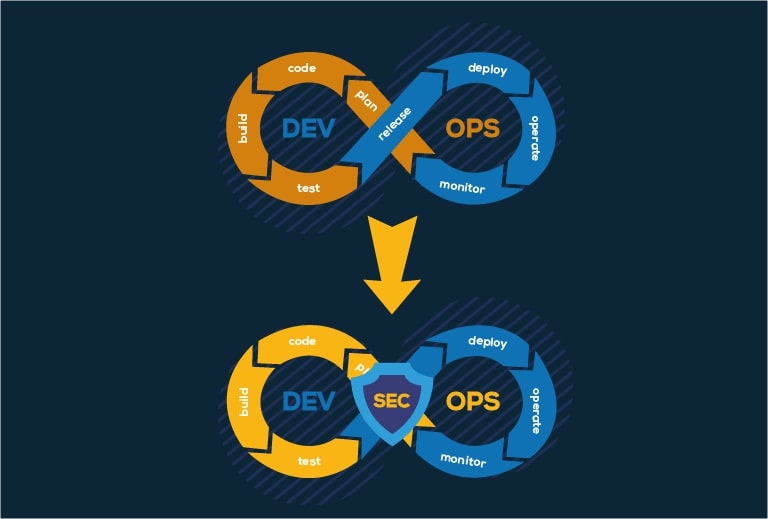
So, you’re thinking about moving from DevOps to DevSecOps? Let’s start with the basics:
Why make the switch?
Well, think about it. We’re living in a world where cyber-attacks are making headlines every other day. Your customers are getting more and more concerned about their data. And let’s be honest, fixing security issues after your product is live is a nightmare. It’s expensive, it’s time-consuming, and it can seriously damage your reputation. So it’s mandatory to make this switch as soon as possible.
Alright, let’s talk about how to make the switch from DevOps to DevSecOps. This isn’t something that happens overnight, but with some planning and effort, you can definitely make it work. Here’s how you might go about it:
Start with a Reality Check
Before you dive in, you need to figure out where you’re at right now. What security measures do you already have in place? Where are the gaps? This isn’t about pointing fingers or finding blame – it’s about getting a clear picture of your starting point.
Get everyone in a room – devs, ops, security folks – and hash it out. Be honest about what’s working and what’s not. Maybe your security testing is hit or miss, or perhaps you’re not really thinking about security until the end of your development cycle. Whatever it is, get it all out in the open.
Get Buy-In from the Top
Let’s face it, any big change needs support from the higher-ups. You’re going to need resources, time, and maybe some new tools to make this transition work. So you’ve got to sell it to the bosses.
Focus on the benefits – better security, fewer vulnerabilities, happier customers. And don’t shy away from the risks of not making the change. In today’s world, a major security breach can be a company-killer. Make sure the decision-makers understand what’s at stake.
Bring Security into the Mix Early
Now, it’s time to start shaking things up. Instead of security being the thing that happens in the end, bring your security folks into the planning stages of your projects. Get them involved in design discussions, sprint planning, all of it.
This might feel weird at first. Your developers might feel like they’re being policed, and your security team might feel out of their depth. That’s okay – it’s all part of the process. The goal is to get everyone thinking about security from day one.
Automate, Automate, Automate
If you’re doing DevOps, you’re probably already big on automation. Now it’s time to bring that same mindset to security. Look for tools that can automatically scan your code for vulnerabilities, check your containers for security issues, that sort of thing.
The key here is to make security checks just another part of your pipeline. Just like you automatically run tests before deploying, you should be automatically checking for security issues, too.
Invest in good DevSecOps Solutions
If you’re serious about streamlining this transition, investing in a complete DevSecOps suite is crucial. Look for solutions that offer complete suite of application security solutions like DAST, SAST, and SCA. A platform like CloudDefense.AI can give you all of that in one place, helping you build security into every stage without slowing down your dev cycles.
Upskill Your Team
This is a big one. Your developers need to learn about secure coding practices. Your ops folks need to get up to speed on security configurations. And your security team needs to learn how to work in this fast-paced, automated environment.
This doesn’t mean everyone needs to become a security expert overnight. Start with the basics and build from there. Bring in trainers, send people to conferences, set up internal workshops. Make learning about security a priority.
Start Small and Iterate
Don’t try to boil the ocean. Pick a small project or a single team to start with. Use this as your DevSecOps pilot. Try out new tools, new processes, new ways of working together.
Learn from what works and what doesn’t. Then, once you’ve ironed out the kinks, start expanding to other teams and projects. This gradual approach can help you avoid overwhelming everyone with too much change at once.
How do you know if it’s working?
You need to keep track of how things are going. Are you catching more vulnerabilities earlier in the process? Is your time-to-deployment still on track? Are you seeing fewer security incidents in production?
Use these metrics to show the value of what you’re doing, and to figure out where you can improve. Remember, DevSecOps isn’t a destination, it’s a journey. You’ll always be tweaking and refining your approach.
DevOps vs. DevSecOps: Which One Should You Choose?
Alright, let’s break this down. When you think about software development, you might find yourself wondering: Do I go with DevOps or DevSecOps? Both sound great on paper, but they tackle the whole process in different ways. So, what’s the right pick for you? Let’s dive into some questions that might get you thinking.
What Matters Most to Your Team?
First, ask yourself: What is your team’s top priority? If speed and efficiency are at the forefront of your goals, DevOps might seem like the way to go. After all, the mantra of “deliver fast” has never been more popular. But what happens when that speed comes at the cost of security? Are you willing to risk vulnerabilities sneaking into your product?
How Do You Handle Security?
Now, think about how you handle security. Is it an afterthought for your team? If you’re only thinking about security at the end of your development cycle, that could be a red flag. With cyber threats popping up left and right, isn’t it time to consider DevSecOps? It’s all about weaving security into every part of your development journey. Doesn’t that sound like a smarter approach?
Are You Ready for Change?
Think about your organization’s culture: Is your team open to change? Transitioning to DevSecOps requires a mindset shift and buy-in from all stakeholders, including developers, operations, and security teams. Are you ready to foster a culture of collaboration and continuous learning? If not, sticking with traditional DevOps might seem easier. But is easy what you really want?
How Do You Measure Success?
Next, reflect on how you measure success: Are you focusing solely on speed and deployment frequency? While these are important metrics, what about security incidents, customer trust, and long-term stability? DevSecOps encourages a broader view of success—one that includes security metrics and risk management. Could this shift in perspective lead to more sustainable growth for your organization?
What’s at Stake if You Don’t Adapt?
Finally, what about the risks of staying in your comfort zone? Can your organization afford a major security breach? The fallout from such an event can be brutal, both financially and for your reputation. DevSecOps aims to catch vulnerabilities early, so you’re not scrambling after the fact. Isn’t it worth it to take a proactive stance?
So, What’s Your Choice?
Ultimately, the choice between DevOps vs DevSecOps boils down to your priorities and how much risk you’re willing to take. Are you ready to tackle the challenges of DevSecOps to improve security, or is the quick and easy path of DevOps more your style? Whatever you decide, it’s crucial to think about what will truly benefit your team and organization in the long run.
Final Words
In the DevOps vs DevSecOps debate, it’s clear that DevSecOps takes security to the next level by integrating it early on. But transitioning to DevSecOps isn’t easy. It takes time, effort, and patience. But in the end, you’ll have a development process that’s not just fast and efficient, but secure too. Since you prioritize security early on, you can actually save money in the long run. Imagine the cost of a major security breach: lost data, damaged reputation, and hefty fines.
DevSecOps helps you catch and fix vulnerabilities before they become expensive problems. So, why wait? Book a free demo with us today and take the first step in streamlining your transition!







