GDPR
GDPR Compliance: Your Data, Our Commitment
It’s not a secret that data breaches can cripple a business, which makes GDPR compliance not just a regulatory requirement but a strategic priority. With CloudDefense.AI, you gain a partner dedicated to protecting your data with state-of-the-art security measures that go beyond the basics. From pinpointing threats, before they escalate to ensuring compliance, we’re here to keep your business protected and GDPR-ready.

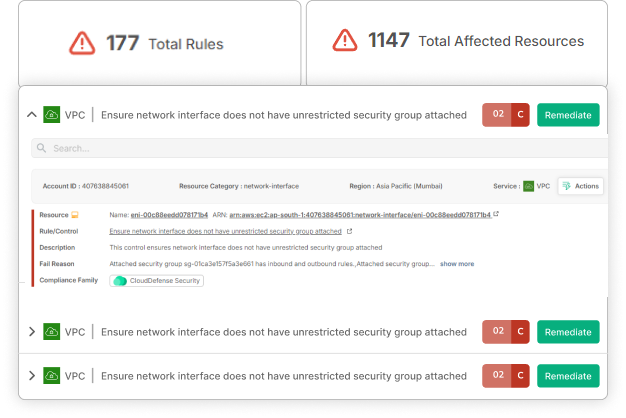
Cloud Security Risk Assessment
Find out which misconfigurations are lurking in your cloud
EMPOWER YOUR BUSINESS
Stay Ahead of Threats. Stay GDPR-Compliant. Book Your Live Demo Today!
Time is ticking, and every delay in security could mean missed opportunities. CloudDefense.AI’s application security solutions embed protection into every stage of your DevOps pipeline so that you can release updates quickly and confidently. Fast, secure, and effortlessly smooth—just how it should be!

The Open Source Dilemma: Balancing Innovation and Compliance
Open source technology fuels the future from cutting-edge apps to Mars exploration. Yet, as powerful as open source is, it presents unique challenges when it comes to GDPR compliance. Aligning the flexibility of open source with the strict demands of GDPR requires a well-calculated approach one that CloudDefense.AI is expertly equipped to deliver.

Master GDPR Compliance with the Best Patch Management
Data breaches often start with a single overlooked vulnerability. In late 2020, three-quarters of breaches stemmed from just one unpatched flaw in Windows. Avoiding such pitfalls is essential to preventing hefty GDPR fines and reputational damage. CloudDefense.AI’s intelligent patch management system empowers you to address critical vulnerabilities swiftly, keeping your digital environment secure and compliant.
How CloudDefense.AI Ensures GDPR Readiness
Advanced Threat Detection
Our scanners outperform national databases, identifying even the smallest breaches before they become a threat.
Priority-Driven Updates
Focus on what matters most—critical vulnerabilities with verified proof-of-concept exploits, so you’re never caught off guard.
Holistic Security Coverage
Use our SCA, SAST, and DAST tools for comprehensive, automated GDPR compliance across your codebase.
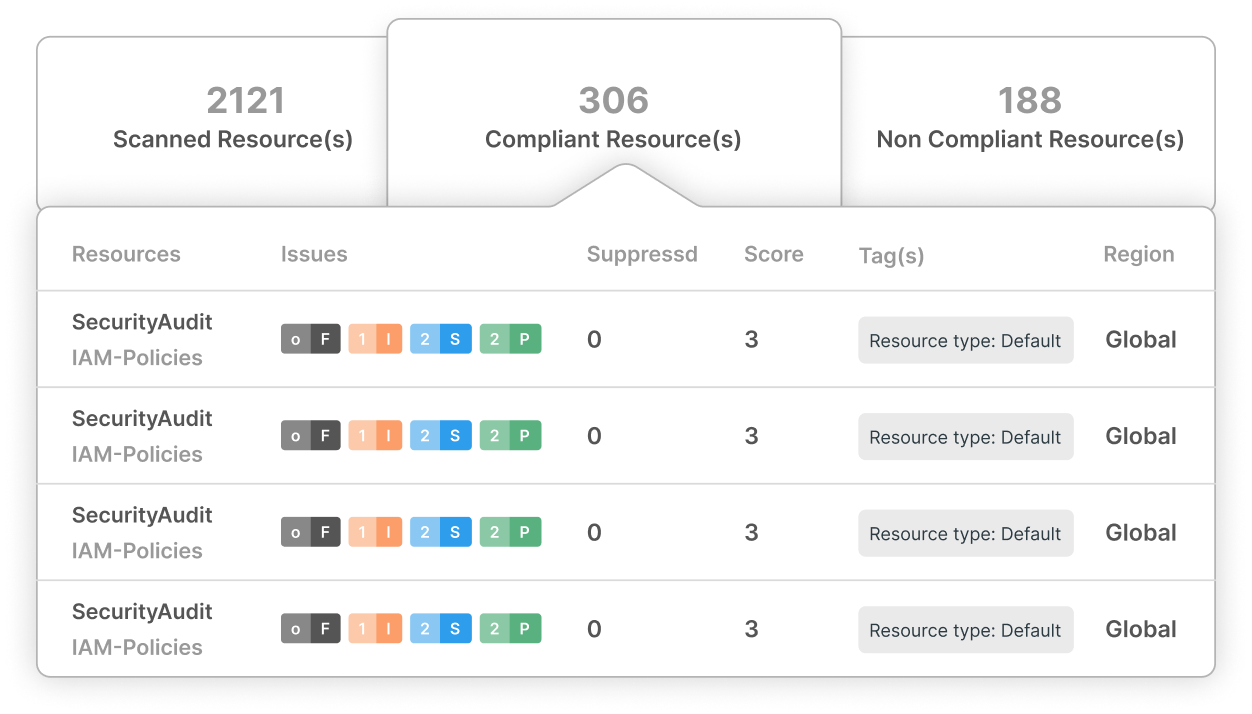
Continuous Compliance Monitoring
We track and address vulnerabilities throughout the software development lifecycle, particularly in open-source components.
Seamless Integration
Automate patch management with live repository syncing, ensuring your systems remain compliant at all times.
Exceeding Industry Standards
Meet and exceed insurer requirements, protecting against data breaches like those that hit industry giants.
Why Patching is Your First Line of Defense
With open-source components making up 60-80% of most codebases, addressing known vulnerabilities is essential. CloudDefense.AI helps you implement patches promptly, reducing the risk of prolonged audits and other GDPR-related disruptions. Rapid response to novel threats—within the crucial 72-hour window—ensures that your business remains compliant and protected from legal liabilities.
Connecting GDPR Requirements to CloudDefense.AI Solutions
Article 25
Data Protection by Design Our SCA tool embeds GDPR compliance into every phase of development, offering a robust defense that surpasses basic national standards.
Article 32
Security of Processing Maintain appropriate security levels by minimizing risks through rigorous access control and entitlement reviews.
Article 83
General Conditions for Fines Rely on transparent security practices and thorough internal audits to protect against fines of up to 4% of global revenue for GDPR violations.
Trust CloudDefense.AI as Your GDPR Compliance Partner to Protect Your Data.
Join us for a live demonstration and see the difference in action.




