Understanding and managing the components of your application are absolutely critical to comprehensive software development. This is where the Software Bill of Materials (SBOM) plays a role. Much as a traditional manufacturer relies on a Bill of Materials (BOM) to keep tabs on the components of a physical product, the software domain utilizes SBOM to meticulously list and organize the diverse elements constituting a software application.
That being said, in this blog, we’re delving into the pivotal concept of SBOM and exploring its seamless integration into your software development lifecycle. We’ll guide you through the steps of generating SBOM with Azure DevOps Pipeline, enhancing your ability to manage and secure your software supply chain effectively.
Let’s dive right in!
What is an Azure DevOps pipeline?
The Azure DevOps Pipeline is a game-changer in the software development world. It’s a cloud-based platform by Microsoft that takes the whole idea of building, testing, and deploying software and makes it a breeze.
Imagine this – You’re a developer, and you have got your hands full with code. Now, instead of drowning in repetitive tasks, the Azure DevOps Pipeline steps in to save the day.
What’s attractive about it is that it allows you to define and manage your CI/CD pipelines as code. Think of it as—you lay out the steps, and the magic happens. This not only brings consistency to the table but also ensures that whatever you’re doing in your development phase can be repeated and scaled up effortlessly.
So, why does this matter?
Well, because it lets you focus on what matters—delivering value to your end-users. No more getting bogged down by the details. The Azure DevOps Pipeline takes care of the heavy lifting, allowing you to concentrate on crafting software that people will love.
In a nutshell, Azure DevOps Pipeline is like your trusty sidekick in the world of software development—making sure your journey from code to deployment is smooth, efficient, and maybe even a bit enjoyable.
Steps in the Azure Pipeline
The Azure pipeline involves several interconnected steps, each playing a crucial role in ensuring the efficient and reliable deployment of applications. Here are the key steps in the Azure Pipeline:
- Triggering
- Manual Trigger: Initiated by a user or a scheduled trigger.
- Continuous Integration (CI): Automatically triggered upon code commits to the repository.
- Source
- Source Code Retrieval: Fetching the latest code from the version control system.
- Artifact Fetching: Downloading any dependencies or artifacts required for the build.
- Build
- Compilation: Compiling the source code into executable artifacts.
- Unit Testing: Running automated tests to ensure code quality.
- Artifact Generation: Creating deployable artifacts for subsequent stages.
- Test
- Integration Testing: Verifying the interaction between components.
- Functional Testing: Assessing the application’s functionality against requirements.
- Code Analysis: Evaluating code for adherence to coding standards.
- Package
- Artifact Packaging: Preparing the application for deployment.
- Dependency Management: Including all necessary libraries and dependencies.
- Deploy
- Infrastructure Provisioning: Setting up the necessary infrastructure.
- Application Deployment: Deploying the application to the target environment.
- Configuration Management: Configuring application settings for the specific environment.
- Release
- Rolling Deployment: Gradual release to minimize impact on users.
- Monitoring: Continuous monitoring of application performance and health.
- Rollback Handling: Strategies for reverting to a previous version in case of issues.
- Post-Deployment
- Automated Testing: Running additional tests post-deployment.
- Notification: Communicating deployment status to relevant stakeholders.
- Logging and Auditing: Capturing logs and audit trails for analysis.
5 Tools to Automate SBOM Creation
In the preceding section, we explored the sequential steps of an Azure DevOps pipeline and their significance in the software development lifecycle. Now, let’s explore the tools for automating SBOM generation within this pipeline. Employing dedicated tools streamlines the process, enhances efficiency, and ensures the accuracy of SBOM data.
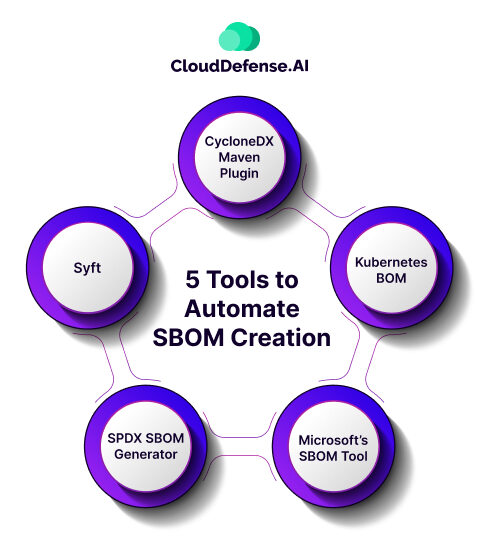
1. CycloneDX Maven Plugin
The CycloneDX Maven plugin is a valuable tool for automating SBOM generation within the build process. Specifically designed for Maven-based projects, this plugin seamlessly integrates SBOM creation, allowing developers to incorporate it directly into their existing build workflows. Its inclusion supports a standardized approach to SBOM generation, contributing to the overall consistency of the development pipeline.
2. Kubernetes BOM
For organizations leveraging Kubernetes for container orchestration, Kubernetes BOM (Bill of Materials) tools aid in automating SBOM creation within Kubernetes environments. These tools assist in identifying and documenting the various components and dependencies present in Kubernetes applications, fostering transparency and traceability in containerized deployments.
3. Microsoft’s SBOM Tool
Microsoft provides its SBOM tool, offering native integration with Azure DevOps. This tool simplifies the SBOM generation process by aligning with the Azure DevOps pipeline. Leveraging Microsoft’s SBOM tool ensures seamless integration of SBOM generation into the broader Azure DevOps environment, aligning with Microsoft’s commitment to enhancing development practices.
4. SPDX SBOM Generator
The Software Package Data Exchange (SPDX) specification is widely adopted for standardizing SBOM formats. The SPDX SBOM generator automates the creation of SBOMs, following the SPDX specification. Its compatibility with Azure DevOps pipelines allows for straightforward integration, ensuring that SBOMs adhere to industry standards for improved interoperability and understanding.
5. Syft
Syft, an open-source SBOM tool, specializes in analyzing container images and filesystems to generate comprehensive SBOMs. Its integration capabilities with Azure DevOps enable developers to automatically incorporate SBOM generation into their containerized workflows. Syft contributes to the security and compliance aspects of the development pipeline by providing visibility into software components.
Benefits of Generating SBOM with Azure DevOps Pipeline
Creating the right SBOM with Azure DevOps Pipeline comes with a host of advantages that significantly boost the effectiveness, security, and overall success of the software development journey. Let’s dive into why it’s so crucial to weave SBOM generation into the Azure DevOps Pipeline.
End-to-End Automation
The Azure DevOps Pipeline takes care of the entire software delivery process, automating everything from merging code to deployment. By seamlessly blending SBOM generation into this automation, we’re cutting down on manual work and sidestepping potential errors.
Traceability and Transparency
SBOMs lay out a detailed list of all the software components and their dependencies. When you generate SBOMs right in the Azure DevOps Pipeline, development teams get a clear view of the entire software stack, making it a breeze to keep tabs on and manage dependencies.
Security Assurance
SBOMs assist in identifying vulnerabilities in third-party components. Integrating SBOM generation into Azure DevOps means automated vulnerability scans, catching potential security hiccups early in the development game.
Compliance and Standards
In many industries, being transparent about your software supply chain is a must. SBOMs align with these compliance standards, making it a walk in the park for organizations to effortlessly meet regulatory requirements.
Rapid Issue Resolution
SBOMs are like a detective’s toolkit, helping spot and isolate issues with software components in record time. When you whip up SBOMs within the Azure DevOps Pipeline, development teams can swiftly zero in on and tackle problems, slashing the time it takes to fix things.
Enhanced Collaboration
SBOMs create a united front, making sure everyone—development, operations, and security teams—are on the same page about the software makeup. By weaving SBOM generation into the Azure DevOps Pipeline, different teams can join forces more efficiently.
Continuous Improvement
The Azure DevOps Pipeline promotes a continuous feedback loop. Incorporating SBOM generation allows for continuous improvement in managing dependencies, security practices, and overall software quality based on real-time insights provided by SBOMs.
Risk Mitigation
SBOMs enable proactive risk management by identifying potential security vulnerabilities and licensing issues. Azure DevOps integration ensures that risk assessments become an integral part of the development process, mitigating potential threats.
How to Generate SBOM with Azure DevOps Pipeline
Generating an SBOM with Azure DevOps Pipeline involves configuring the pipeline to include specific tasks and tools that extract information about the software components and their dependencies. Below is a general guide on how to set up SBOM generation within an Azure DevOps Pipeline.
1. Choose SBOM Generation Tools
Select tools that are compatible with Azure DevOps for SBOM generation. For example, you can choose tools like CycloneDX Maven plugin, Kubernetes BOM, Microsoft’s SBOM tool, SPDX SBOM Generator, or Syft.
2. Integrate SBOM Tools into the Pipeline
In your Azure DevOps Pipeline configuration, add steps to integrate the chosen SBOM generation tools. This may involve adding a specific task or script to execute the tool as part of the build or release process.
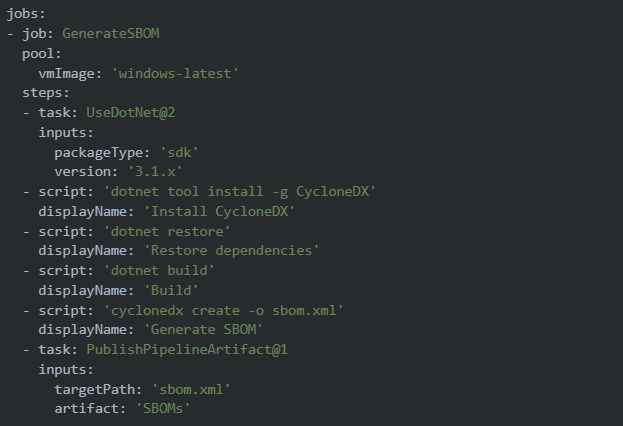
3. Configure SBOM Output
Specify the format and location for the generated SBOM. Common formats include CycloneDX, SPDX, or custom XML or JSON formats. Ensure that the SBOM is stored in a location accessible to other pipeline stages or can be published as an artifact.
4. Integrate SBOM Generation into the CI/CD Process
Depending on your CI/CD process, incorporate SBOM generation into relevant stages. For example, you might generate SBOM during the build stage for CI and during the deployment or release stage for CD.
5. Trigger SBOM Generation Events
Define triggers for SBOM generation events. For example, generate SBOMs on each code commit, scheduled builds, or specific release events. This ensures that SBOMs are regularly updated to reflect changes in the codebase.
6. Implement Quality Checks
Integrate quality checks within the pipeline to ensure the accuracy and completeness of the SBOM. This may include validating the SBOM format, checking for any missing dependencies, or verifying against security policies.
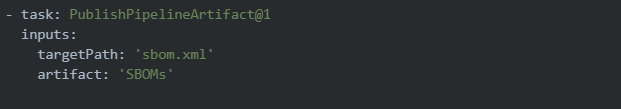
7. Artifact Storage and Sharing
Store the generated SBOM as a pipeline artifact or in a designated location. Ensure that relevant stakeholders have access to the SBOM for auditing, compliance, and security purposes.
8. Documentation and Communication
Document the SBOM generation process within your pipeline. Communicate the importance of SBOMs to the development team and other stakeholders to foster awareness and collaboration.
SBOM Exports in Azure DevOps Pipeline
Once the SBOM is generated within the Azure DevOps Pipeline, it needs to be appropriately exported and stored for further use, auditing, compliance, or communication purposes. Here are key considerations:
1. Artifact Storage
Publishing as Pipeline Artifact: Use Azure DevOps Pipeline tasks to publish the generated SBOM as a pipeline artifact. This ensures that the SBOM is associated with the specific build or release, making it easily accessible for downstream tasks.
Storing in Azure Artifacts or External Repositories: Depending on your organization’s policies, you may choose to store SBOMs in Azure Artifacts or external artifact repositories.
2. Integration with Release Pipelines
If you have a separate release pipeline, ensure that SBOMs are appropriately passed along and stored. Consider triggering SBOM generation during deployment stages to capture environment-specific dependencies.
3. Accessibility and Permissions
Set appropriate permissions for accessing SBOMs. Ensure that relevant stakeholders, such as security teams and compliance officers, have the necessary access to review and analyze the SBOM data.
4. Export Formats
Consider exporting SBOMs in commonly accepted formats such as CycloneDX or SPDX. This ensures compatibility with industry standards and facilitates easy integration with other tools or systems.
Notification and Alerts: Implement notifications or alerts to inform relevant teams or individuals when new SBOMs are generated. This can be achieved through Azure DevOps notifications or external communication channels.
FAQ
How can I monitor the Azure DevOps Pipeline?
You can monitor the progress of your build and release in the Azure DevOps Pipeline dashboard. Additionally, you can utilize logs, metrics, and notifications for real-time monitoring. Take advantage of Azure Monitor to gain advanced insights and analytics.
What is SBOM management?
SBOM management involves creating, updating, and maintaining the Software Bill of Materials. It includes documenting dependencies, versions, and licenses of software components used in a project for transparency, compliance, and security.
Can I use multiple SBOM tools in a single Azure DevOps Pipeline?
Yes, you can use multiple SBOM tools in a single Azure DevOps Pipeline. Choose tools compatible with your project and configure pipeline steps accordingly. This allows for diverse analysis and enhances the accuracy of SBOM generation.
Conclusion
To sum it up, integrating an SBOM with Azure DevOps Pipeline marks a pivotal stride towards elevating the efficiency, security, and transparency of software development processes. The Azure DevOps Pipeline, with its end-to-end automation capabilities, offers a robust foundation for orchestrating SBOM generation at key stages.
Now, the real magic happens when you team up Azure DevOps pipelines with tools like CycloneDX, Kubernetes BOM, Microsoft’s SBOM tool, SPDX SBOM Generator, or Syft. These tools are your go-to thing for automating the documentation of dependencies, making sure you’re not just hitting compliance standards but also beefing up those security measures.
Through continuous monitoring, quality assurance, and collaborative practices, organizations can forge a resilient development pipeline that prioritizes transparency, compliance, and the delivery of secure and reliable software.







