Healthcare
Secure Your Healthcare Data with CloudDefense.AI
Healthcare data breaches are a serious and growing problem, costing more than in any other industry. Cybercriminals are drawn to healthcare because of the valuable patient information it holds. And with new technologies getting integrated into patient care, they can also bring new security challenges. So it’s more important than ever to have strong security. CloudDefense.AI offers a comprehensive platform to secure your cloud environment, protect sensitive data, and maintain industry compliance—all tailored to meet the unique needs of healthcare organizations.

Cloud Security Risk Assessment
Find out which misconfigurations are lurking in your cloud
Stop Cyberattacks
Stop Cyberattacks from Crippling Your Healthcare Infrastructure
Your healthcare data is your most valuable asset. Can your healthcare organization withstand the pressure? Protect it like never before with CloudDefense.AI. Our comprehensive security solutions create an impenetrable barrier against cyberattacks.

Get Complete Visibility
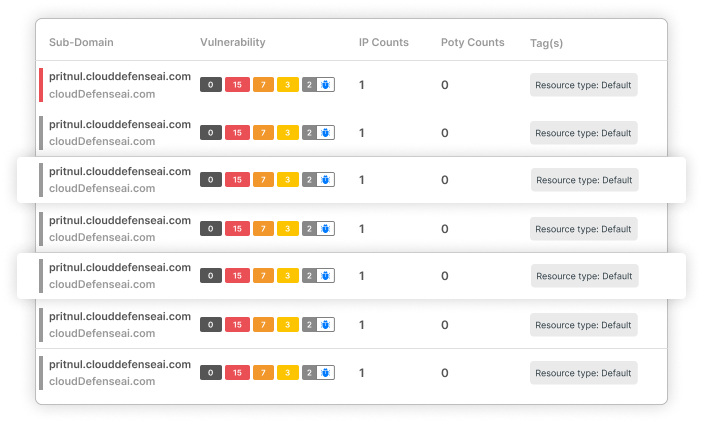
Get a crystal-clear view of your entire healthcare ecosystem. From virtual machines to the latest serverless functions, we expose every nook and cranny without slowing you down. Your complex environment becomes an open book in minutes.

Stop Threats Before They Strike
Don’t just identify risks; dismantle and fix them. Our platform connects the dots between vulnerabilities, user identities, and network weak spots, revealing hidden attack paths. We prioritize threats so you can focus on what truly matters.

HIPAA Compliance Made Easy
Easily assess your environment against HIPAA and other compliance standards with our built-in frameworks. Generate comprehensive compliance reports with a single click, simplifying audits and ensuring you stay compliant.
Healthcare Data: The Most Valuable Target for Hackers
$9.77 M
For more than a decade, Healthcare has been the most expensive industry for data breaches, with the average breach costing $9.77 million, a position held since 2011.
67% Surge
In 2024, 67% of healthcare organizations experienced ransomware attacks, up from 60% in 2023, highlighting increasing threats in the sector.
31 Million
Over 31 million Americans were affected by major healthcare cyberattacks and data breaches in the first half of the year, highlighting the extensive reach of these threats.
Future-Proof Your Healthcare Infrastructure: Implement End-to-end Cloud Security to Tackle Evolving Threats
Are you tired of guessing where your next cyberattack will come from? CloudDefense.AI offers a proactive approach to securing your healthcare organization. With our advanced features, you can gain complete visibility, automate compliance, protect sensitive data, and empower your team to prevent breaches.
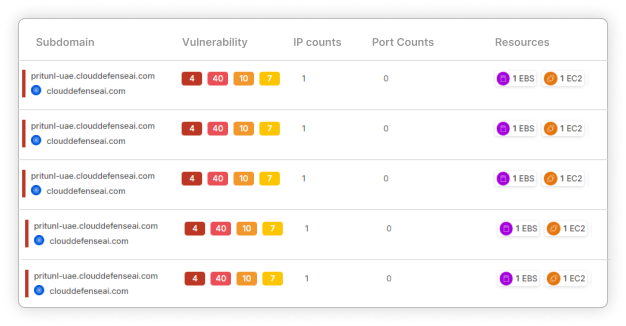
Scan Your Entire Cloud Infrastructure
No Blind Spots
We've got eyes everywhere in your cloud setup; no agents are required. From virtual machines to containers to serverless functions, our agentless approach covers it all.
Smart Alerts
Our Security Graph doesn't just flag issues; it connects the dots. We give you the full context, so you're not drowning in a sea of meaningless pings. Focus on what truly matters for your healthcare data.
One-Stop Risk View
Imagine seeing your entire cloud landscape at a glance, across all platforms. That's what we deliver. Spot potential threats, vulnerabilities, and compliance gaps in one unified view. It's like having a security command center at your fingertips.
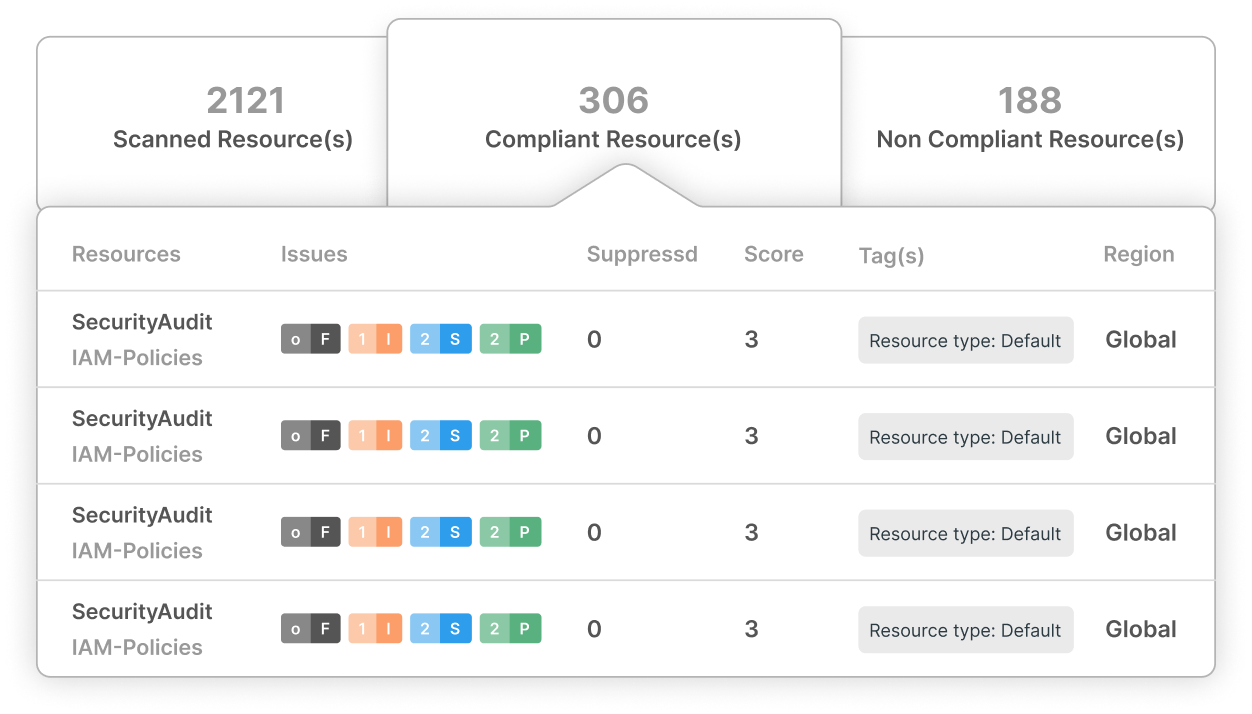
Compliance Made Easy
Always-On Checks
HIPAA compliance isn't a one-and-done deal. Our system keeps a constant eye on your setup, measuring it against over various frameworks, including HIPAA, PCI DSS, NIST, and more. Sleep easy knowing you're always audit-ready.
Tailor-Made Frameworks
Your organization is unique, and your compliance needs might be too. That's why we let you build custom frameworks or tweak existing ones. Mix and match policies to create the perfect fit for your healthcare setup. It's compliance, your way.
One-Click Reports
Our system generates comprehensive, granular reports in seconds. No more scrambling or last minute preparing documentation. We've got your back when it counts.
Advanced Attack Path Analysis
Comprehensive Vulnerability Mapping
Our system maps out how different vulnerabilities, user accounts, and sensitive data connect. It's not just about individual weak points – we show you how they could create a perfect storm for attackers.
Focus on the Real Threats
Not all risks are created equal. We help you zero in on the attack paths that could really hurt. It's like having a threat radar that cuts through the noise, showing you where to strehten your defenses for maximum impact.
Think Like a Hacker
Ever wonder how hackers think? Our system lets you identify potential attacks, showing how intruders might hop from one system to another. It's like having a crystal ball that reveals the moves of your adversaries before they make them.
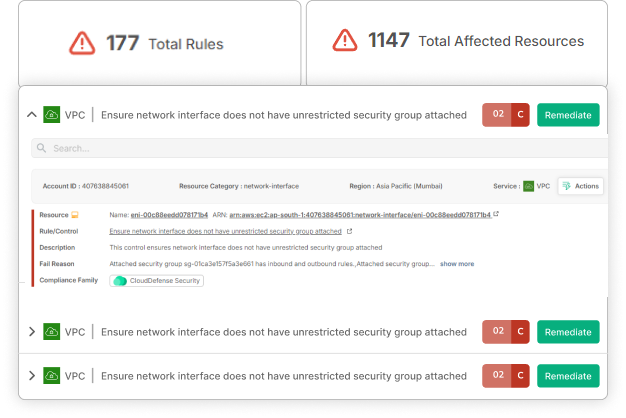
Efficient Auto remediation
Automated Vulnerability Mitigation
Why waste time on repetitive fixes? Our platform automatically resolves common vulnerabilities and misconfigurations. This frees up your team to focus on more complex security challenges while ensuring that basic issues are addressed promptly and consistently.
Comprehensive Remediation Guidance
When we spot an issue, we don't just flag it - we show you exactly how to fix it. Step-by-step remediation guidance means anyone on your team can contribute to strengthening your security posture.
Continuous Improvement
Our autoremediation features don't just fix problems – they help your team learn. By providing context and explanations for each fix, we help build security knowledge across your organization. This leads to better practices and fewer issues over time.