If you are a company that processes payments through cards, you must comply with PCI DSS. Although PCI audits can be challenging for any company handling cardholder data, they are necessary if you want to stay in business.
With 400 controls in place, ensuring compliance can be a challenge for your security team. However, you need to understand that PCI DSS audits are essential to customers and can benefit your company as well.
A quick read of this article will help you understand the PCI audit process and empower you to accelerate your progress with our very own PCI compliance audit checklist.
What is a PCI DSS Compliance?
PCI DSS (Payment Card Industry Data Security Standard) compliance refers to a set of globally recognized security standards established by major credit card companies, including Visa, MasterCard, and American Express.
These standards are designed to ensure that organizations handling payment card information process, transmit, and store it securely to safeguard sensitive cardholder data. The primary goal of PCI DSS compliance is to prevent data breaches, protect cardholder information, and maintain consumer trust.
What is the Purpose of PCI DSS Compliance?
The rise of digital card payments has been extraordinary. In 2020 alone, over 900 million online transactions were processed, and this number is expected to surge to over 2.14 billion by 2025.
However, this increase also creates more opportunities for cybercriminals to exploit vulnerabilities. PCI DSS compliance acts as a critical defense mechanism, mandating strong security protocols for businesses to protect sensitive user data effectively.
From encryption practices to access control measures, PCI DSS compliance lays the foundation for businesses to create a secure payment ecosystem and reduce the risk of fraud and cyberattacks.
What is PCI Compliance Audit?
A PCI compliance audit examines and evaluates an organization’s adherence to the Payment Card Industry Data Security Standard (PCI DSS), a compliance framework instituted in 2004 by major credit card companies: Mastercard, Visa, JCB, American Express, and Discover.
This audit assesses the security measures and practices implemented by businesses that handle payment card data. The objective is to ensure compliance with PCI DSS requirements, which include safeguarding sensitive cardholder information, maintaining a secure network infrastructure, implementing access controls, regularly monitoring and testing systems, and maintaining an information security policy.
The PCI compliance audit helps assess the effectiveness of security controls and ascertain if the organization meets the necessary standards to protect payment card data from potential breaches and unauthorized access. Successful completion of a PCI audit demonstrates a commitment to maintaining a secure environment for handling payment transactions.
What are the PCI DSS Levels?
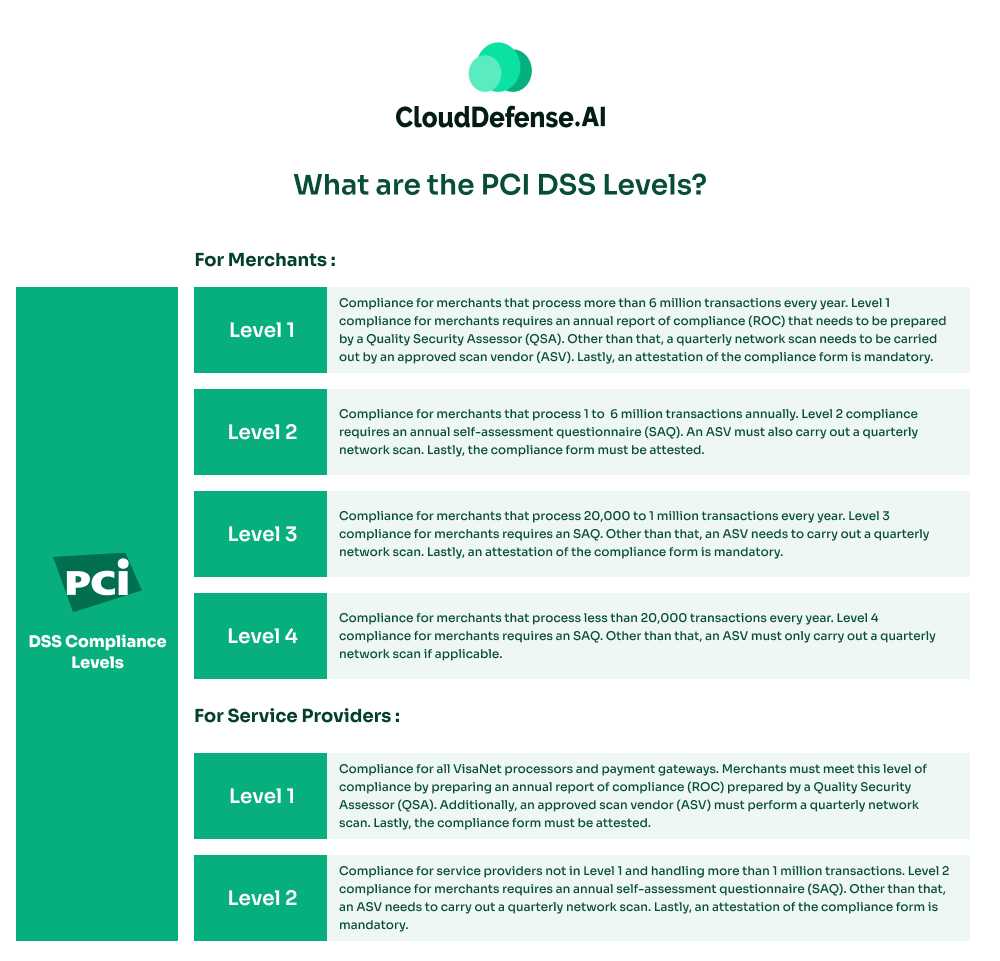
PCI DSS compliance is offered in 4 levels. The levels and the required criteria differ for merchants and service providers.
For Merchants:
- PCI Merchant Level 1: Compliance for merchants that process more than 6 million transactions every year. Level 1 compliance for merchants requires an annual report of compliance (ROC) that needs to be prepared by a Quality Security Assessor (QSA). Other than that, a quarterly network scan needs to be carried out by an approved scan vendor (ASV). Lastly, an attestation of the compliance form is mandatory.
- PCI Merchant Level 2: Compliance for merchants that process 1 to 6 million transactions annually. Level 2 compliance requires an annual self-assessment questionnaire (SAQ). An ASV must also carry out a quarterly network scan. Lastly, the compliance form must be attested.
- PCI Merchant Level 3: Compliance for merchants that process 20,000 to 1 million transactions every year. Level 3 compliance for merchants requires an SAQ. Other than that, an ASV needs to carry out a quarterly network scan. Lastly, an attestation of the compliance form is mandatory.
- PCI Merchant Level 4: Compliance for merchants that process less than 20,000 transactions every year. Level 4 compliance for merchants requires an SAQ. Other than that, an ASV must only carry out a quarterly network scan if applicable.
For Service Providers:
- Level 1: Compliance for all VisaNet processors and payment gateways. Merchants must meet this level of compliance by preparing an annual report of compliance (ROC) prepared by a Quality Security Assessor (QSA). Additionally, an approved scan vendor (ASV) must perform a quarterly network scan. Lastly, the compliance form must be attested.
- Level 2: Compliance for service providers not in Level 1 and handling more than 1 million transactions. Level 2 compliance for merchants requires an annual self-assessment questionnaire (SAQ). Other than that, an ASV needs to carry out a quarterly network scan. Lastly, an attestation of the compliance form is mandatory.
Why is the PCI audit process important?
The PCI audit process is vital for ensuring that businesses handling payment card data follow strict security standards outlined in the PCI DSS. It helps identify and fix vulnerabilities, reducing the risk of data breaches and fraud. Compliance verification is key, as non-compliance can result in penalties and damage to reputation.
Successfully completing a PCI compliance audit builds customer trust and shows a commitment to data security. It also contributes to a positive industry reputation and meets legal requirements in some regions. The process encourages continuous improvement in security measures and addresses potential areas for enhancement. Additionally, many partners and vendors require proof of PCI compliance, making successful audits crucial for business relationships.
PCI DSS Audit Requirements: 12 Fundamentals Requirements
PCI DSS outlines 12 technical and operational requirements that organizations must adhere to to achieve PCI compliance. These requirements are designed to protect cardholder data and maintain a secure environment. Let’s delve into each requirement.
PCI Requirement 1: Firewall Configuration
Establishing and maintaining a strong firewall configuration to protect cardholder data.
PCI Requirement 2: Avoid Default Passwords
Steering clear of provider-provided system passwords and other default security parameters.
PCI Requirement 3: Protect Stored Cardholder Data
Implementing methods such as encryption, truncation, masking, or hashing to protect stored cardholder data.
PCI Requirement 4: Encrypt Transmission of Cardholder Data
Encrypting cardholder data during transmission over open, public networks.
PCI Requirement 5: Malware Protection
Protecting all systems against malware by regularly updating anti-virus software.
PCI Requirement 6: Secure Systems and Applications
Developing and maintaining secure systems and applications by applying vendor-supplied security patches.
PCI Requirement 7: Restrict Access to Cardholder Data
Limiting access to cardholder data to only those individuals who require it for their job responsibilities.
PCI Requirement 8: Identify and Verify Access
Assigning unique identities to individuals with system access, holding them accountable for their actions.
PCI Requirement 9: Restrict Physical Access
Controlling physical access to systems hosting cardholder data to prevent unauthorized entry.
PCI Requirement 10: Monitor Network Access
Monitoring and logging all network resources and cardholder data access.
PCI Requirement 11: Regularly Test Security Systems
Regularly testing security systems, components, and processes to identify and address vulnerabilities.
PCI Requirement 12: Maintain Information Security Policies
Establishing and maintaining policies addressing information security for all personnel.
PCI Compliance Audit Checklist: Key to Expediting PCI
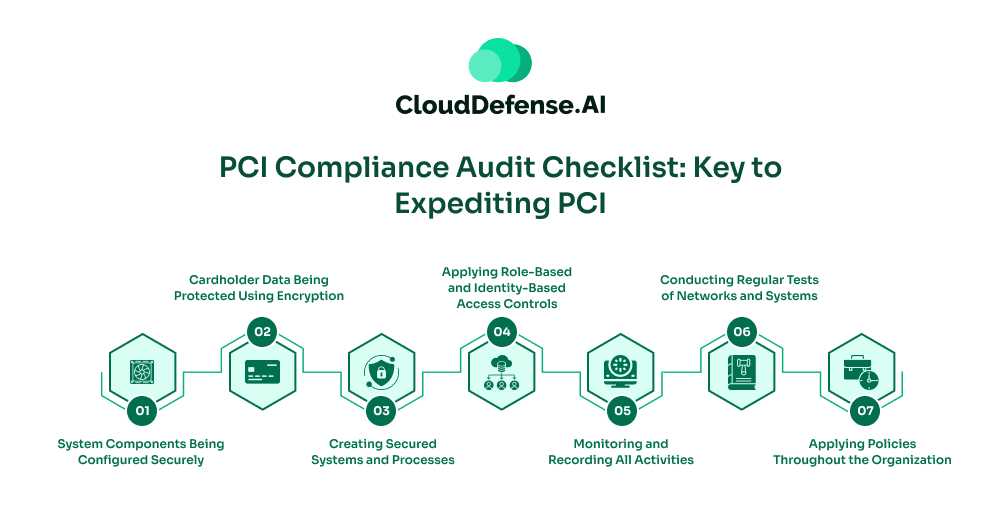
We have prepared a PCI compliance audit checklist for you to meet the 12 PCI requirements smoothly.
1. System Components Being Configured Securely
Regularly update and patch systems to ensure they adhere to secure configurations, minimizing vulnerabilities.
2. Cardholder Data Being Protected Using Encryption
Encrypt stored cardholder data and implement access controls to protect sensitive information from unauthorized disclosure. Ensure data is also encrypted during transmission, reducing the risk of interception by malicious entities.
3. Creating Secured Systems and Processes
To ensure ongoing system security, employ secure coding practices, conduct regular security assessments, and promptly address vulnerabilities. Deploy antivirus software, firewalls, and best practices to defend against malware, reducing the risk of system compromise.
4. Applying Role-Based and Identity-Based Access Controls
Implement role-based access controls, limiting access to sensitive data to only those individuals who require it for their specific roles. Implement strong authentication methods, including unique user IDs and secure passwords, to verify the identity of users accessing the system.
Implement physical security measures, such as access controls and surveillance, to prevent unauthorized access to areas containing cardholder data.
5. Monitoring and Recording All Activities
Maintain detailed logs of user activities, regularly review them, and implement monitoring systems to detect and respond to suspicious behavior promptly.
6. Conducting Regular Tests of Networks and Systems
Conduct regular vulnerability assessments and penetration testing to identify and address security weaknesses, ensuring the ongoing effectiveness of security measures.
7. Applying Policies Throughout the Organization
Establish comprehensive security policies and procedures, conduct regular security awareness training for employees, and enforce adherence to security protocols.
In developing a strong PCI DSS compliance plan, organizations must align with this checklist and objectives, building a secure payment card environment and instilling confidence in stakeholders regarding the protection of sensitive financial information. This approach ensures continuous improvement and adaptability in the data security process.
How does a PCI DSS audit work?
A PCI audit is a systematic evaluation to ensure that organizations handling payment card data comply with established security standards. Here’s a simplified overview of how a PCI audit works.
Determine Scope
Identify the systems, networks, and processes involved in payment card data handling to establish the audit’s scope.
Engage a Qualified Security Assessor
Employ an independent QSA, certified by the PCI Security Standards Council, to conduct the audit.
Pre-Assessment
Some organizations opt for a pre-assessment to identify potential issues before the formal audit, allowing proactive remediation.
Documentation Review
Gather and review security policies, procedures, and technical configuration documentation.
Assessment of Security Controls
The QSA evaluates the effectiveness of security controls in place, ensuring alignment with PCI requirements.
Report Generation
The QSA compiles findings into a detailed report, highlighting areas of compliance and any identified non-compliance. Recommendations for improvement may be included.
Remediation
Organizations address identified issues and implement necessary changes to achieve compliance.
Validation Assessment
A follow-up assessment may be conducted to validate that remediation efforts have been successful and that the organization is now in compliance.
Attestation of Compliance (AoC)
Once compliance is achieved, the organization submits an Attestation of Compliance (AoC) to relevant parties, affirming adherence to PCI.
Submission of Reports
Submit all reports that include AoC, SAQ, and RoC. We will explain what these are in detail.
- The Self-Assessment Questionnaire (SAQ) serves as a self-declaration tool for organizations undergoing PCI DSS audits, allowing them to assert their compliance status and methods. Organizations at Levels 2-4 can use the SAQ as an alternative to external audits, while Level 1 companies require external audits. Various SAQ types cater to different organizations.
- Report on Compliance (RoC) is a documentation for PCI DSS assessments, completed by a QSA or Internal Security Assessor (ISA) for Level 1 and some Level 2 organizations.
- The PCI Attestation of Compliance (AoC) validates compliance through either SAQ or RoC.
Annual Renewal Audits
PCI compliance is typically validated annually through renewal audits to ensure continued adherence to security standards.
7 Tips for Preparing PCI Compliance Audit
The many security controls in place to regulate the handling of cardholder data can be overwhelming for your IT admin team. Do not worry as we have prepared 7 tips for you that will assist you in passing your PCI audit process with flying colors.
Follow the Latest Standards of PCI
PCI DSS regulations are constantly changing with time. New policies are added, and older ones are discarded when deemed futile. The Security Standards Council keeps updating the standards to take into account new security threats in the industry.
For example, the latest standard of PCI is PCI v4.0, which will stay relevant until 2025. The last version of PCI, v3.2.1, will stay active until March 2024. Keep yourself updated with the latest compliance standards. This will help you to identify any compliance gaps that you have.
Conducting a Risk Assessment
Assess the risks you have to all the cardholder data you store. Analyzing the risks enables you to identify all potential vulnerabilities that you have. Risk assessment can provide valuable data to your security team so that they can implement the required measures to secure the data.
Identifying the Scope and Planning Accordingly
Before you choose to get a PCI audit, it is essential to identify the scope of the audit. You can do so by pinpointing multiple factors, such as geographic location, payment applications, third-party vendors, and your services, to create a narrowed-down scope for your PCI audit.
Ensuring Network Security
You must implement network security, including employing firewalls, encrypting transmitted cardholder data, segmenting networks, and enforcing strict access controls. This will help you to create a strong network security infrastructure and ensure compliance with PCI DSS.
Monitor The Activity of Users
Monitoring user activity is essential for maintaining a secure and compliant environment with payment card data. It aids in protecting sensitive information, detecting threats, and proving PCI DSS adherence during audits. You can detect unauthorized access, identify unusual transactions, mitigate insider threats, and demonstrate compliance by monitoring.
Ensure Third-party Vendors Are Compliant
Many data breaches stem from vulnerabilities introduced by third-party service providers. Organizations outsourcing their cardholder data environment (CDE) share responsibility for PCI DSS compliance. Regularly assessing third-party PCI compliance identifies potential weaknesses, enabling the enforcement of necessary security measures.
Train Your Staff
Once you have all the required controls in place, it is time to focus on the employees of your organization. It is highly recommended to train your employees on password protection and detecting any malicious activities such as ransomware or social engineering methods.
The Future of PCI DSS: Prepare for PCI 4.0
If you are a company looking to get PCI DSS compliance, then you need to get familiar with version 4.0, which will be implemented on March 31, 2024. As a company dealing with payment card data, it’s important for you to take steps to protect the sensitive financial data of your clients.
Stay in the loop by regularly checking the PCI SSC website and other trusted sources for updates on PCI DSS 4.0 requirements, guidelines, FAQs, and deadlines. You can collaborate with your stakeholders to assess your current cardholder data environment, pinpointing any gaps or weaknesses that need addressing.
Start by conducting a thorough risk assessment, prioritizing mitigation efforts based on severity, and then develop a detailed compliance plan for PCI 4.0. It’s all about implementing those necessary security controls, from encryption to access controls, tailored to meet PCI 4.0 standards.
Most importantly, you should ensure that your staff is well-versed in the updated requirements, and don’t forget to engage a QSA if needed. Keep a watchful eye on your systems, validate compliance, and document everything – from risk assessments to system changes. Get ready because PCI DSS 4.0 is just around the corner with more security controls in place.
FAQ
Who performs PCI audits?
Qualified Security Assessors (QSAs) perform PCI audits. QSAs are external entities certified by the PCI Security Standards Council. Audits can also be conducted Internally with the help of an Internal Security Assessor, or ISA.
How often are PCI DSS audits required?
PCI DSS requires all companies that conduct 300,000 transactions every year to undergo a PCI DSS audit. Therefore, a minimum of one audit per year is required, and it is best to conduct two audits annually.
Is PCI DSS still applicable if I only accept credit cards over the phone?
Most payments need to be made through a payment gateway or a portal. However, if an entity accepts payment through a phone, it must still adhere to PCI DSS regulations.
How much does PCI DSS compliance cost?
PCI compliance costs depend on the number of payments being processed in an enterprise. Larger companies that process millions of payments yearly need to spend at least $50k to $200k annually. Smaller companies need to spend around $20k to complete a SAQ and AoC.
Conclusion
A PCI DSS compliance audit is a must for your enterprise if you extensively deal with payment card data. Threat actors target users’ financial data so they can unethically access their cards. PCI is essential in protecting sensitive information and card users from financial damage.
If you are looking to expedite your PCI compliance audit process, implement the required security controls, implement security policies, carry out employee training, and collaborate with auditors in accordance with the PCI compliance audit checklist. We hope the 7 tips that we have provided in this guide will help you to streamline your PCI DSS audit process.







