In today’s DevSecOps, a major issue with AppSec isn’t identifying vulnerabilities, but prioritizing and remediating them. Cyberthreats are evolving rapidly and increasingly getting sophisticated with the advancement of technology. Thus, response time is of the highest importance. However, security scanners generate a significant amount of security alerts, burning security and development teams under mountains of poorly prioritized warnings.
When teams aren’t able to differentiate between a critical or low-priority alert, it not only slows down the response time but also enables attackers to exploit the vulnerability. Even though modern security tools have evolved with technology, it still utilizes CVSS scores and lacks intelligent contextualization.
Thus, modern organizations are inching towards utilizing AI to prioritize critical vulnerabilities and presenting teams with smart prioritization results. In this guide, we will take a look at how AI helps to prioritize critical vulnerabilities.
Why Traditional Prioritization is Falling Short?
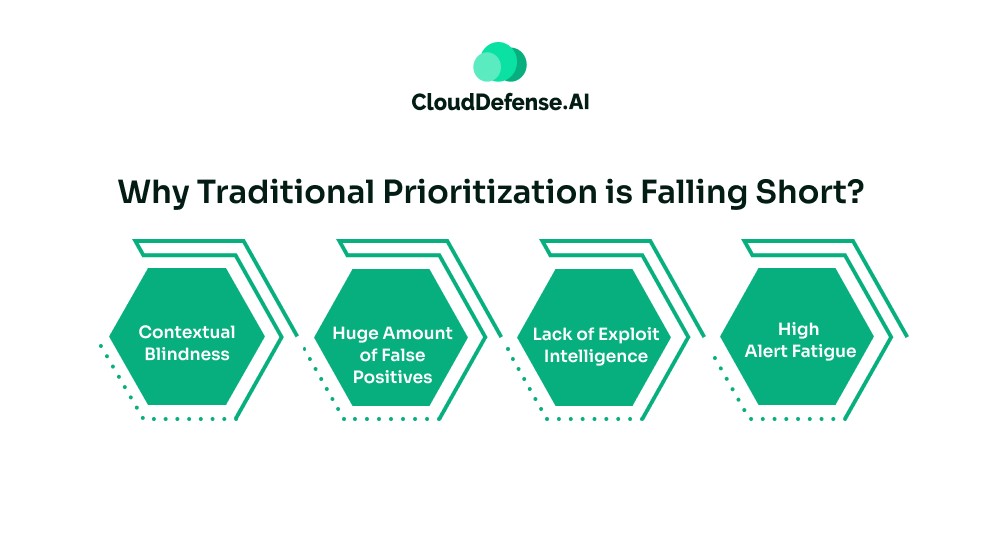
Traditional prioritization has been the basis for most prioritization processes. But as cyberthreats are evolving, it is unable to provide an efficient prioritization.
Here are the primary reasons that have made it fall short:
- Contextual Blindness: The traditional prioritization process depends largely on the findings of CVE and scores the vulnerabilities based on CVSS. While the CVSS scores deliver a benchmark rating, it doesn’t involve context during prioritisation. As a result, it is unable to differentiate whether the alert can truly impact an application or if it is just dead code.
- Huge Amount of False Positives: Many scanners are based on predefined context and rules, causing them to falsely flag many alerts. Security analysts had to spend a lot of time triaging those false positive alerts manually, causing a waste of their time. Moreover, it causes the real threats to slip away and significantly impact the application in production.
- Lack of Exploit Intelligence: Not all vulnerabilities in CVE have a known public exploit available, and there are many instances where specific exploits are sold as a service. Due to a lack of exploit intelligence, many critical threats are poorly prioritized, giving threat actors time to make their move.
- High Alert Fatigue: When security and development teams are bombarded with poorly prioritized alerts where most of them are “critical”, it leads to alert fatigue. It forces developers and security professionals to triage all the alerts to find out about the actual criticality of each vulnerability. This is ultimately leading to high mean time to remediation as teams remain occupied addressing low-impact threats.
How the Arrival of Artificial Intelligence is Transforming Vulnerability Prioritization
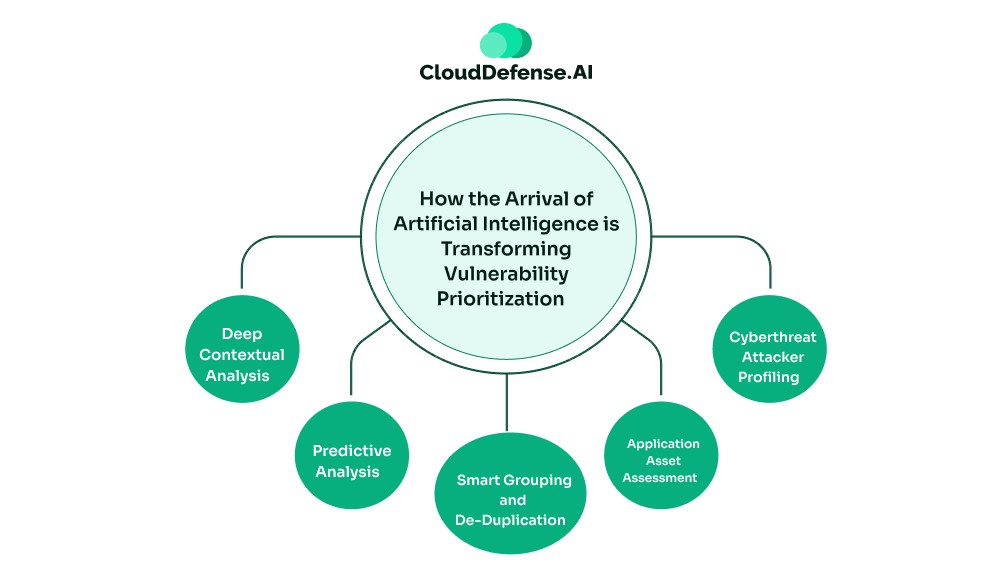
The integration of AI in vulnerability triaging has transformed how threats are prioritized. AI enables enterprises to bring a contextual understanding to the triaging process that legacy tools lack.
Modern security platforms with AI to prioritize critical vulnerabilities don’t just identify a vulnerability, but it performs analysis to identify whether the vulnerability is exploitable and how much impact it can make.
Here is how AI for prioritize critical vulnerabilities is transforming triaging:
Deep Contextual Analysis
AI-powered security tools don’t just identify a threat, it utilizes ML to analyze the data flow and determine whether a vulnerability is exploitable. It analyses the business context, developers intent, reachability, and many other contexts before it prioritizes the vulnerability.
Unlike the standard security system, it doesn’t just scan the syntax. Rather, it evaluates whether the particular vulnerability existing in a code can be triggered through user input. Based on the contextual understanding, it identifies the reachability and severity of the vulnerability and prioritizes the threat intelligently.
Predictive Analysis
Modern security scanners based on AI are continuously ingesting threat data from threat intelligence feeds, threat pattern databases, and OWASP benchmarks. It enables the security system with AI to prioritize critical vulnerabilities to predict whether a flawed code can be exploited.
For smart prioritization, it visualizes the attack path and predicts how an attacker would move laterally to exploit a compromise for a major breach. This predictivity analysis enables the security platform to properly prioritize a vulnerability that might seem as a low severity can become more critical than its scores indicate.
Smart Grouping and De-Duplication
In many instances, a group of attackers doesn’t exploit a severe vulnerability; they exploit a chain of low-impact flaws to make a major impact. To ensure smart prioritization, the AI-powered security tools group those low-level threats and highlight the critical attack path that should be immediately fixed.
Security tools with AI to prioritize critical vulnerabilities also help with de-duplicating similar threats spread across the application. It helps in connecting the dots and helps in properly prioritizing those threats at once.
Application Asset Assessment
An application has multiple assets associated with it, where some of the functions may be publicly exposed while some of them are internal. Security tools with AI to prioritize critical vulnerabilities continuously tally all the security findings against inventory data from API, network scans, repositories, and many others.
Based on the assessment, it provides a risk score for a vulnerability. A high-impact vulnerability in a sandbox system will be scored low, whereas an issue in a customer-facing endpoint will be scored with a high severity rating.
Cyberthreat Attacker Profiling
Modern AI-powered security tools often perform cyberthreat attacker profiling during smart prioritization. It continuously scans for threat intelligence from different sources that involve government portals and dark web telemetry.
It enables the tool to identify and correlate cyberthreat attackers with CVEs they target. Based on the threat actor’s interest in exploiting a specific type of vulnerability, the security system enhances the severity scoring when it finds similar types of threats.
QINA Pulse: A Powerful Security Assistant for Smart Prioritization
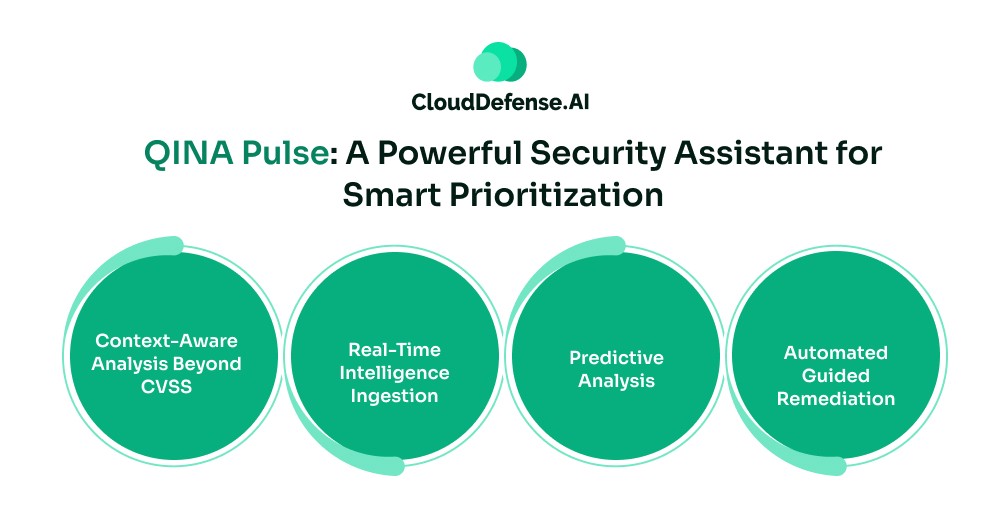
To utilize AI to prioritize critical vulnerabilities, organizations are slowly inching towards a powerful AI security tool: QINA Pulse. It is an AI-driven security assistant that is meticulously designed to help teams with smart prioritization of all the alerts. Rather than providing the team with a long list of security findings, it provides a prioritized alert report with an appropriate severity tag.
By delivering the report directly into the IDE, it enables the team to properly focus on threats based on their real-world impact. Pulse utilizes a proprietary process that eliminates all the dead code by understanding the context, helping to drastically reduce the false positives. But how does QINA Pulse helps to prioritize critical vulnerabilities before attackers do?
Here are some key characteristics that assist in the prioritization process:
- Context-Aware Analysis Beyond CVSS: QINA Pulse doesn’t just prioritize security alerts based on CVSS score or preset factors. It takes all the alerts through context-aware analysis, which involves AI and ML to understand the context behind each flawed code. It understands business context, application infrastructure, the developer’s intent, and where it will be used. The security assistant also understands the role and checks all the conversation history. Based on the analysis, it prioritizes the security alerts and delivers the reports.
- Real-Time Intelligence Ingestion: A speciality of QINA Pulse is that it continuously ingests data from all the security tools and databases. It also ingests threat data from real-time threat intelligence feeds associated with open-source databases, government repositories, and other commercial sources. It maps all the security findings against the threat intelligence to identify the possible impact of each flawed code.
- Predictive Analysis: A unique characteristic of Pulse that makes it stand apart is its capability to predict how a flawed code can be exploited. It utilizes predictive analysis where the machine learning models predict how an identified vulnerability can reach execution point through user input. It creates a code flow of the execution, which enables the tool to understand and predict how a specific vulnerable code can impact the application.
- Automated Guided Remediation: Along with smart prioritization, Pulse also enables teams to quickly remediate any high-impact threat before it is exploited by attackers. The prioritized alert report also provides the team with actionable remediation guidance they can execute. It also provides teams with detailed code snippets so that they can locate the flawed code and fix the flaw before attackers can make their move. In some cases, it automates the remediation process of fixing the flawed code when commanded by developers or security professionals.
Critical Metrics Improved Through AI-Powered Vulnerability Prioritization
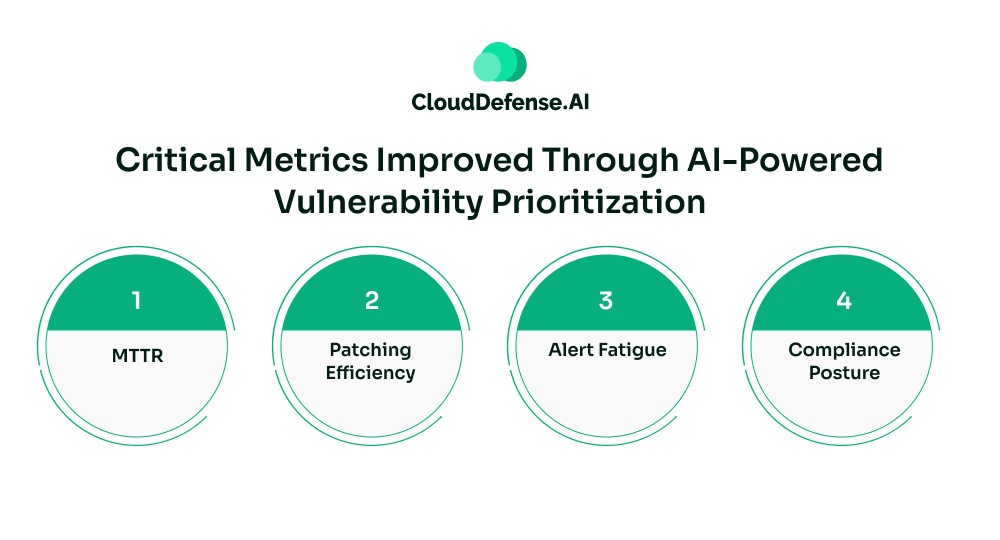
When an enterprise implements a security tool with AI to prioritize critical vulnerabilities, it significantly makes improvement in all the key security metrics:
- MTTR: Through AI-powered triaging processes, organisations are able to improve the Mean Time to Remediation(MTTR) by a large margin. It eliminates all the bottlenecks and minimizes the time needed to remediate vulnerabilities.
- Patching Efficiency: Achieving smart prioritization through advanced tools like QINA Pulse helps teams to focus on actual threats that require immediate response. Through quick response, teams can remediate more threats, improving the patch efficiency ratio.
- Alert Fatigue: Modern AI-powered security tools deliver intelligent alert reports with appropriate prioritization of each threat. Some reports even provide the reasons behind the priority of each vulnerability along with remediation guidance. This creates an environment where teams can easily address security threats without facing alert fatigue.
- Compliance Posture: When an enterprise implements AI-based vulnerability prioritization, the compliance posture improves by a large margin. AI-powered security tools provide real-time compliance monitoring through automated gap assessment, threat prioritization, and automated remediation. Moreover, all the security evidence is automatically collected to ensure adherence to security standards like SOC II, PCI-DSS, GDPR, HIPAA, and others.
Bottom Line
For most modern organization manual alert triage has been a key roadblock to achieving an optimum application security posture. It not only delayed response to threats but also affected the application development pace. However, modern security tools with AI to prioritize critical vulnerabilities have helped enterprises eliminate most of the issues associated with the traditional AppSec approach.
Tools like QINA Pulse help teams to focus on threats that matter most and eliminate all the false positives. Most importantly, through smart prioritization, teams are able to eliminate threats and secure their application before an attacker can exploit it.






