What Is a Next-Generation Firewall (NGFW)?

Firewalls work on inspecting traffic to a system and block any activity that it identifies as a threat. Generic firewalls identify malicious traffic based on pre-defined policies. Next-generation firewalls, on the other hand, are a notch higher by providing additional security to the system. So, what is a next-generation firewall? A Next-Generation Firewall, or NGFW, […]
Understanding The Shared Responsibility Model

A shared responsibility model divides security responsibilities between cloud providers and users, where providers secure the infrastructure, and users protect data, applications, and configurations. What is a Shared Responsibility Model? The shared responsibility model is a fundamental framework in cloud computing that defines security and operational responsibilities between the cloud service provider (CSP) and the […]
What is Cloud Workload? Types, Challenges & Best Practices

The cloud has completely changed the way we access and utilize computing resources. But with the rise of this technology comes a new vocabulary, and “cloud workload” is often tossed around without a clear explanation. This article aims to demystify this term and provide a clear understanding of what it entails. In simple terms, a […]
What is a Ransomware Attack? How Does it Work?

A ransomware attack is a type of cyberattack where malicious software, or ransomware, encrypts a victim’s files or locks them out of their system. What is Ransomware? Ransomware is a type of malicious software (malware) designed to block access to a computer system or data until a ransom is paid. It encrypts files or locks […]
What is CI/CD Security?

CI/CD security is all about keeping your software development pipelines safe. It protects code, secures sensitive data, and prevents vulnerabilities as your team builds, tests, and deploys updates. Definition — What is CI/CD Security? CI/CD Security means integrating security checks and controls directly into the continuous integration and delivery pipelines. It’s about protecting every step […]
What is SOC 2 Compliance? Definition, Principles, Types & More
SOC 2 is a security standard for organizations handling sensitive data. It ensures compliance with strict privacy and security practices, focusing on data protection, confidentiality, and integrity to safeguard customer information. What is SOC 2 Compliance? SOC 2 compliance is a set of security standards for organizations that manage sensitive customer data, ensuring they maintain […]
What is Vulnerability Management?

Vulnerability Management is the process of identifying, assessing, prioritizing, and addressing security weaknesses in systems and software to reduce risks, enhance protection, and maintain a secure IT environment. What is Vulnerability Management? — Definition Vulnerability Management is all about finding and fixing security vulnerabilities in an organization’s systems and software. It involves identifying potential risks […]
What is a DDoS attack? How to Prevent DDoS?
A DDoS attack floods a server or network with overwhelming traffic, disrupting service and denying users access.
What Is a Denial-of-Service (DoS) Attack?

A Denial-of-Service (DoS) attack is a malicious attempt to disrupt the availability of a targeted server, network, or service by overwhelming it with excessive traffic or resource requests. What Is a Denial-of-Service (DoS) Attack? A Denial-of-Service (DoS) attack is a malicious attempt to disrupt the normal functioning of a website, online service, or computer system […]
What is Attack Path Analysis? Understanding Your Cloud Security Blind Spots
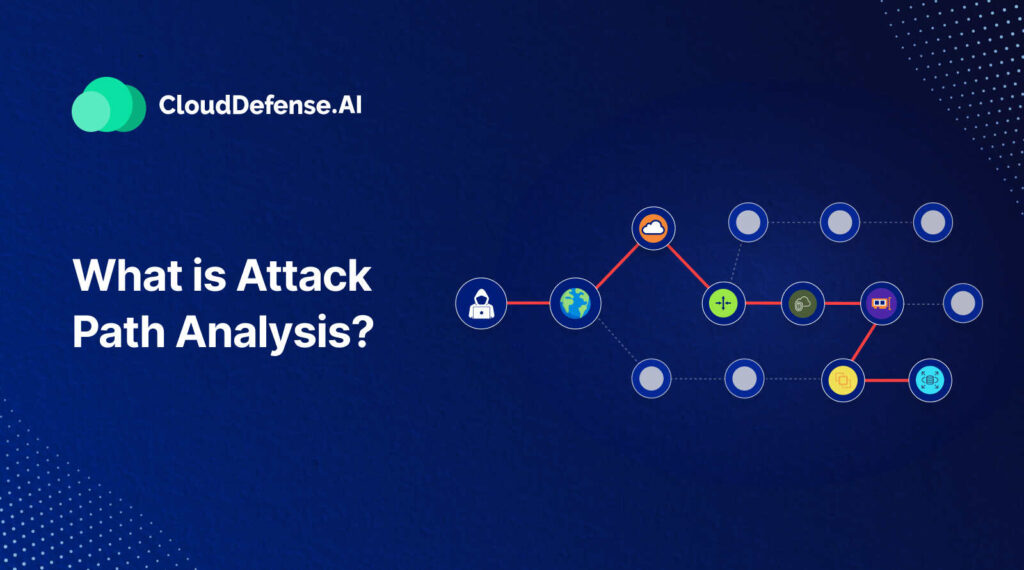
Attack path analysis (APA) is a cybersecurity method used to identify and map potential attack routes that threat actors could exploit to infiltrate systems or networks by targeting vulnerabilities. What is Attack Path Analysis (APA)? Attack Path Analysis Explained Attack path analysis offers a visual representation of the routes attackers can exploit to navigate both […]



