SAST is a method of analyzing source code to find potential security vulnerabilities before the application is even run.
SAST can be classified as a security checkup for your code, helping you identify and fix problems early on in the SDLC.
What problems does SAST solve?
SAST identifies security vulnerabilities early in the Software Development Life Cycle (SDLC), even before the application is functional.
By analyzing source code without executing it, SAST helps developers detect and fix vulnerabilities early, preventing them from reaching later phases or the final release.
A key feature of SAST is the real-time feedback it provides during coding. This immediate insight allows developers to address security issues on the spot.
SAST tools often include graphical representations that pinpoint vulnerabilities and offer remediation guidance, even for those without deep security expertise.
Additionally, SAST tools offer customizable reporting, allowing developers to track security issues through dashboards.
This organized approach supports a secure SDLC, ensuring fast issue resolution. Integrating SAST into regular development routines—such as during builds or code check-ins—helps teams continuously monitor and enhance the security of their applications.
How Does SAST Work?
SAST works by analyzing an application’s source code, bytecode, or binary files without executing the program. It scans the code for security vulnerabilities like logic flaws, insecure coding practices, and potential weaknesses that attackers could exploit.
SAST tools operate by parsing the code and matching it against predefined rules and patterns that identify vulnerabilities such as SQL injection, cross-site scripting, and buffer overflows. The analysis occurs early in the development process, allowing developers to detect and fix security issues before the application is deployed.
These tools integrate with the development pipeline, automating the scanning process during code check-ins or builds. SAST generates reports that highlight detected vulnerabilities, enabling teams to prioritize remediation based on severity and risk.
Why SAST is a Key Component of Secure Application Development?
SAST does a marvelous job of enhancing software security with the shift-left approach. Shift-left in cybersecurity refers to the practice of integrating security measures and considerations earlier in the SDLC. This assists developers in identifying and rectifying security issues from the source code itself, reducing future costs and the potential impact that future remediations can have.
SAST not only serves as a gatekeeper for security vulnerabilities but also empowers developers with real-time feedback on code quality. By integrating SAST into the development process, developers receive immediate insights into potential security flaws after each code update.
This approach allows for continuous learning, enabling developers to understand and address security concerns. A continuous feedback loop is created, which helps build a culture of security consciousness and encourages the development of safer and more resilient code for your software.
What are the Steps to run SAST Effectively?

Running SAST efficiently requires a well-structured approach, especially for organizations managing numerous applications across different platforms and languages. Here are the six steps to help you effectively run SAST:
1. Select the Right Tool
Choose a SAST tool that supports the programming languages and frameworks used in your applications. The tool should be capable of performing in-depth code analysis and identifying vulnerabilities in your specific environment.
2. Set Up the Scanning Infrastructure
Deploy the tool by managing licensing, setting up access controls, and ensuring you have the necessary resources, such as servers and databases. This infrastructure will support seamless code scanning across applications.
3. Customize the Tool
Fine-tune the tool to fit your organization’s needs by reducing false positives or creating custom rules for deeper analysis. Also, integrate it into your development pipeline and set up dashboards and reports to track scanning results effectively.
4. Onboard and Prioritize Application
Onboard all your applications into the tool, prioritizing high-risk ones first. Ensure that application scans are aligned with development schedules, such as release cycles, code check-ins, or regular builds.
5. Analyze the Scan Results
Review the scan results, filter out false positives, and ensure the remaining vulnerabilities are assigned to the appropriate teams for remediation. Tracking and timely fixing of these issues are crucial for maintaining secure code.
6. Ensure Governance and Provide Training
Establish governance to ensure the correct use of SAST tools and embed them into the SDLC. Additionally, provide training to your development teams to maximize the effectiveness of the scanning process and foster a culture of secure coding.
Benefits of SAST

SAST scanners and tools have a lot of advantages over other technologies. Let’s go over them one by one.
SAST is a leading application security tool and a crucial element of a comprehensive application security strategy. When integrated effectively into the SDLC, SAST tools offer several key advantages:
1. Shifting Security Left
SAST’s “shift left” approach promotes preventative measures by identifying vulnerabilities early in the software development lifecycle. This reduces the cost and complexity of remediation by addressing issues when they’re easier to fix. SAST’s ability to identify vulnerabilities early helps mitigate risks and ensures the release of a more secure application.
2. Promoting Secure Coding
SAST tools detect flaws resulting from common coding errors, helping development teams adhere to secure coding standards and best practices. This ensures that code is more resilient to potential external attacks.
3. Identifying Common Vulnerabilities
Automated SAST tools can reliably detect frequent security issues such as buffer overflows, SQL injection, and cross-site scripting. Flagging these vulnerabilities early helps secure the application with a higher degree of confidence.
4. Encourages Continuous Security Improvement
SAST creates a culture of continuous security by providing developers with real-time feedback as they code. This ongoing guidance helps teams improve their security practices over time, making each development cycle more secure than the last.
Limitations of SAST

While SAST is essential for identifying vulnerabilities in the early stages of development, it has some limitations in its operations.
- Limited Detection in Later Stages: SAST only examines static code, so it may overlook vulnerabilities that arise later in the Software Development Life Cycle (SDLC) or post-deployment. It cannot catch runtime issues.
- Focuses Only on Static Code: SAST analyzes non-executing code, meaning it cannot uncover runtime issues like environmental misconfigurations or vulnerabilities that occur when the application is live.
- Dependency on Source Code Access: SAST requires direct access to the source code. If source code isn’t available, the tool can’t perform its analysis.
- Targeted at Custom Code: Traditional SAST tools primarily assess custom code, failing to cover vulnerabilities in third-party libraries or open-source software components.
- High Rate of False Positives: SAST tools are known for generating many false positives, which can slow down development by focusing attention on non-issues.
Where DAST and SCA Fill the Gaps
Other application security solutions, such as DAST and SCA, can overcome almost all of SAST’s limitations. DAST complements SAST by analyzing applications at runtime and detecting vulnerabilities that SAST tools may miss. SCA focuses on scanning open-source components and third-party dependencies, areas where SAST falls short.
Buying all these tools separately arises concerns of integration with one another and extra costs. This is why to achieve complete application security coverage, a solution like CloudDefense.AI’s CNAPP should be chosen. CloudDefense.AI provides all three—SAST, DAST, and SCA—within a single package, ensuring full security for both custom code and third-party components.
Differences Between SAST and DAST: SAST vs. DAST
There are two key methodologies, SAST (Static Application Security Testing) and DAST (Dynamic Application Security Testing), that help identify vulnerabilities in application development, but they operate in fundamentally different ways.
Understanding the differences between SAST and DAST will help you make informed decisions on when and how to use each, or whether combining them is the optimal choice for complete application security.
| Aspect | SAST (Static Application Security Testing) | DAST (Dynamic Application Security Testing) |
| Testing Approach | White-box testing: Analyzes the source code without execution. | Black-box testing: Tests the application during runtime. |
| Access to Source Code | Requires access to the source code, libraries, and dependencies. | No access to source code is needed; tests from an external perspective. |
| Timing in SDLC | Conducted early in the SDLC during the coding/development phase. | Performed later in the SDLC when the application is functional. |
| Perspective | Tests the application from the inside out (developer’s view). | Tests the application from the outside in (hacker’s view). |
| Focus | Identifies code-level vulnerabilities like logic errors or improper coding practices. | Focuses on runtime issues such as misconfigurations or vulnerabilities exposed during execution. |
| Application State | This can be done before the application is operational or functional. | Requires a working version of the application to test. |
| Vulnerabilities Detected | Detects issues such as insecure code patterns, logic flaws, and issues with third-party libraries. | Identifies runtime vulnerabilities like SQL injection, cross-site scripting, and broken authentication. |
| Cost of Fixing Issues | Cheaper to fix vulnerabilities early in the development process. | Can be more expensive to fix vulnerabilities detected at runtime. |
| Integration with CI/CD Pipelines | Easily integrates with CI/CD for continuous testing during development. | Typically used for testing deployed applications or in pre-release environments. |
SAST and DAST are not competing technologies but complementary ones. SAST ensures that the code is secure from the inside out, while DAST verifies that the application is safe from external attacks.
By implementing both, you can maximize your application’s security throughout the SDLC, addressing potential risks at every stage. Consider reading our blog on DAST if you would like to learn more about it.
How to choose the Best SAST Tool for your Company?
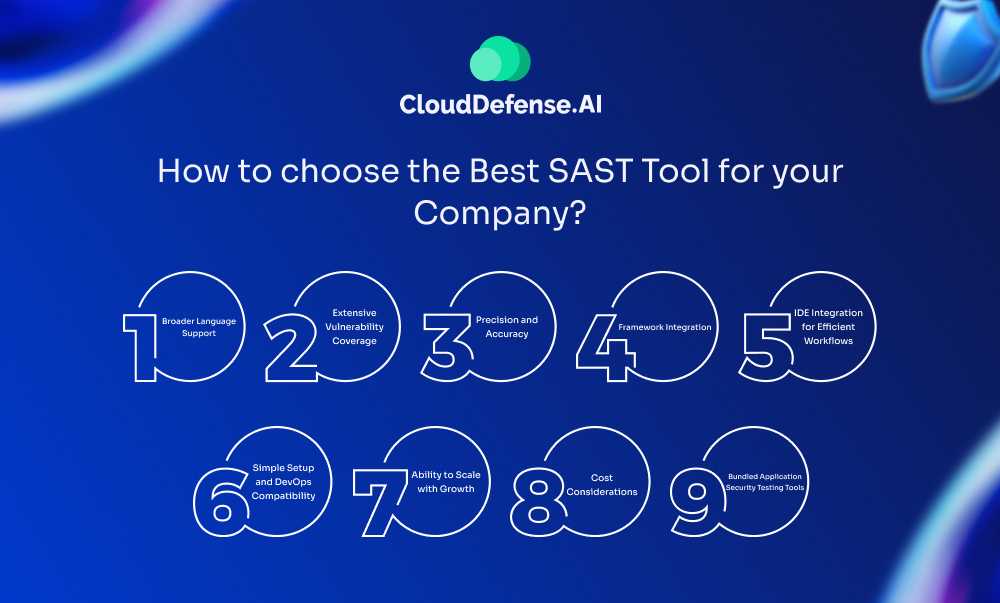
Selecting the right Static Application Security Testing (SAST) tool for your organization can be challenging, given the vast number of options available. To make the right choice, consider these key factors:
1. Broader Language Support
Ensure the SAST tool covers all the programming languages your company uses. A tool with broad language support ensures your entire codebase is protected.
2. Extensive Vulnerability Coverage
Your SAST tool should identify critical vulnerabilities, including all of OWASP’s Top Ten security risks. Comprehensive coverage is crucial for robust application security.
3. Precision and Accuracy
A good SAST tool minimizes false positives and false negatives. High accuracy saves your team from chasing unnecessary issues, allowing them to focus on real vulnerabilities.
4. Framework Integration
The tool should integrate smoothly with the frameworks and development environments you’re already using. This ensures it fits easily into your SDLC without disrupting workflows.
5. IDE Integration for Efficient Workflows
SAST tools that work directly within your Integrated Development Environment (IDE) allow developers to catch vulnerabilities early, speeding up remediation and boosting efficiency.
6. Simple Setup and DevOps Compatibility
Look for a tool that is simple to configure and integrates seamlessly with your DevOps pipeline. A complex setup can slow down adoption and reduce effectiveness.
7. Ability to Scale with Growth
Make sure the SAST tool can scale to support larger teams and projects as your organization grows. It should maintain efficiency whether analyzing small or large codebases.
8. Cost Considerations
Be mindful of how costs will rise as you scale. Pricing models can vary by user, application, or code volume, so find a solution that aligns with your budget and growth plans.
9. Bundled Application Security Testing Tools
Bundled AST tools that include other testing solutions like DAST and SCA provide the best value. These suites allow you to cover all aspects of security, from static code analysis to runtime and third-party dependency checks.
Solutions like CloudDefense.AI offer a full suite, giving you end-to-end security in one package, which simplifies implementation and ensures holistic protection across your entire software lifecycle.
Maximizing Application Security with Integrated SAST Solutions
Integrating SAST, DAST, and SCA creates a failproof security framework that allows developers to identify and remediate vulnerabilities at every stage of the Software Development Life Cycle.
The best SAST tools catch issues early in the code, preventing complex problems later on. DAST tests the application in real-time, uncovering runtime vulnerabilities that could be exploited in production. Meanwhile, SCA monitors third-party components for known vulnerabilities, ensuring a secure software supply chain.
Together, these tools provide complete coverage, enhancing the overall security posture of your applications. With CloudDefense.AI’s CNAPP, you can smoothly integrate SAST, DAST, and SCA into your workflow for unparalleled protection.
Don’t trust us? Book a free demo to see it for yourself.







