For years, cybersecurity experts have been fighting a two-sided, persistent battle. On one side, the security analysts are fighting hard to stay ahead of all modern threats and zero-day attacks. On the other side, they are facing a mountain of security alerts from different security scanners, most of which are noise(false positives).
Even in 2026, when security scanners have advanced significantly, many researchers have indicated that a substantial segment of alerts remains false positives. This tsunami of alerts is not only causing high alert fatigue but also making analysts and developers miss out on real-vulnerability alerts.
Working on reducing false positives has become a goal for organizations as it improves MTTR and prevents real-threats from slipping through cracks. To build robust security, organizations should work to reduce false positives in security tools and focus on real threats.
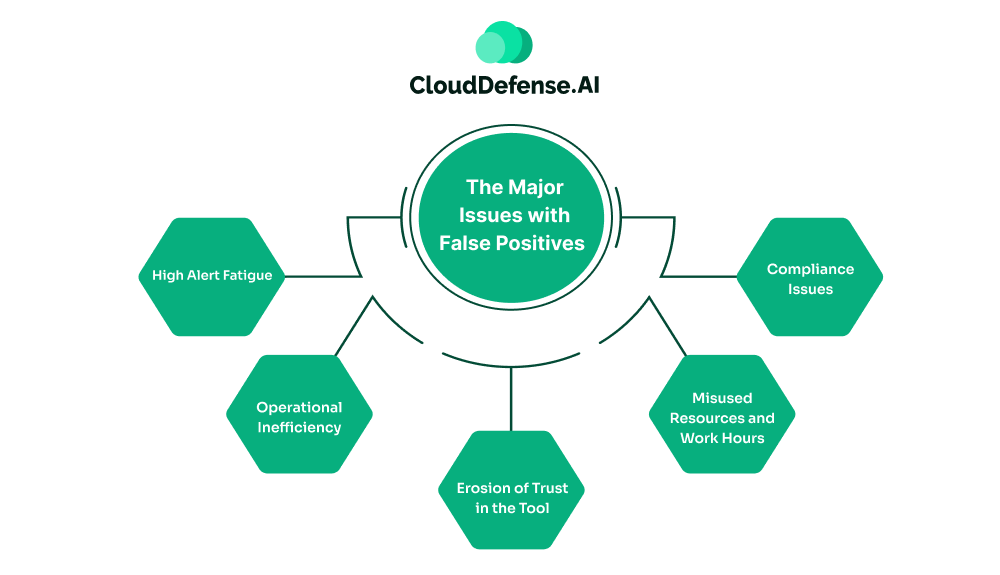
The Major Issues with False Positives
False positives are a bottleneck to modern AppSec that mostly occur when security scanners flag a benign code or legitimate activity as a threat. Different reasons contribute to the noise.
While organizations might feel it is a normal nuisance, the consequences are terrible:
- High Alert Fatigue: Using traditional security scanners exposes security analysts and developers to a plethora of false positives. Triaging these false security alerts daily burns out the experts, which ultimately leads to alert fatigue. The alert fatigue develops a click-through syndrome where skilled individuals dismiss most alerts without properly triaging them. Many high-performing talents often feel distressed and start deprioritizing alerts, causing serious alerts to go unnoticed.
- Operational Inefficiency: False positives create a lot of nuisance that not only leads to confusion but also inefficiency in operation. Since the team constantly faces a large number of alerts, it becomes difficult to identify real security incidents at the right time. Moreover, the mountain of daily life makes it difficult for the team to separate high-impact vulnerabilities from low-risk flaws. It leads to slow response to incidents that ultimately degrades overall operational efficiency of the security strategy.
- Erosion of Trust in the Tool: As the security scanners keep on producing an array of false positives daily, it gradually erodes the trust that teams have in the tools. With time, the team keeps distrusting the alert and starts undermining the effectiveness of the security strategy. The gradual erosion of trust has severe consequences in the end, hampering the overall security posture of the organization.
- Misused Resources and Work Hours: Triaging hundreds of false positives daily not only wastes organizational resources but also wastes work hours. Development teams are often involved in investigating the false alarms, which forces them to miss out on development tasks. This recursive cycle of tiring false positives not only creates a major security bottleneck but also prevents security teams from focusing on real vulnerabilities. Importantly, teams have limited time and resources, which adds to the pressure.
- Compliance Issues: Companies rely on their vulnerability reports to maintain compliance with different regulatory standards. Auditors, during auditing, require complete evidence to ensure all the security threats are properly managed. However, vulnerability reports stained with multiple false positive alerts can make the organization face compliance issues. Numerous false positives in the reports can make the whole security strategy less trustworthy and create doubt in the minds of the auditors.
The Main Causes of False Positives
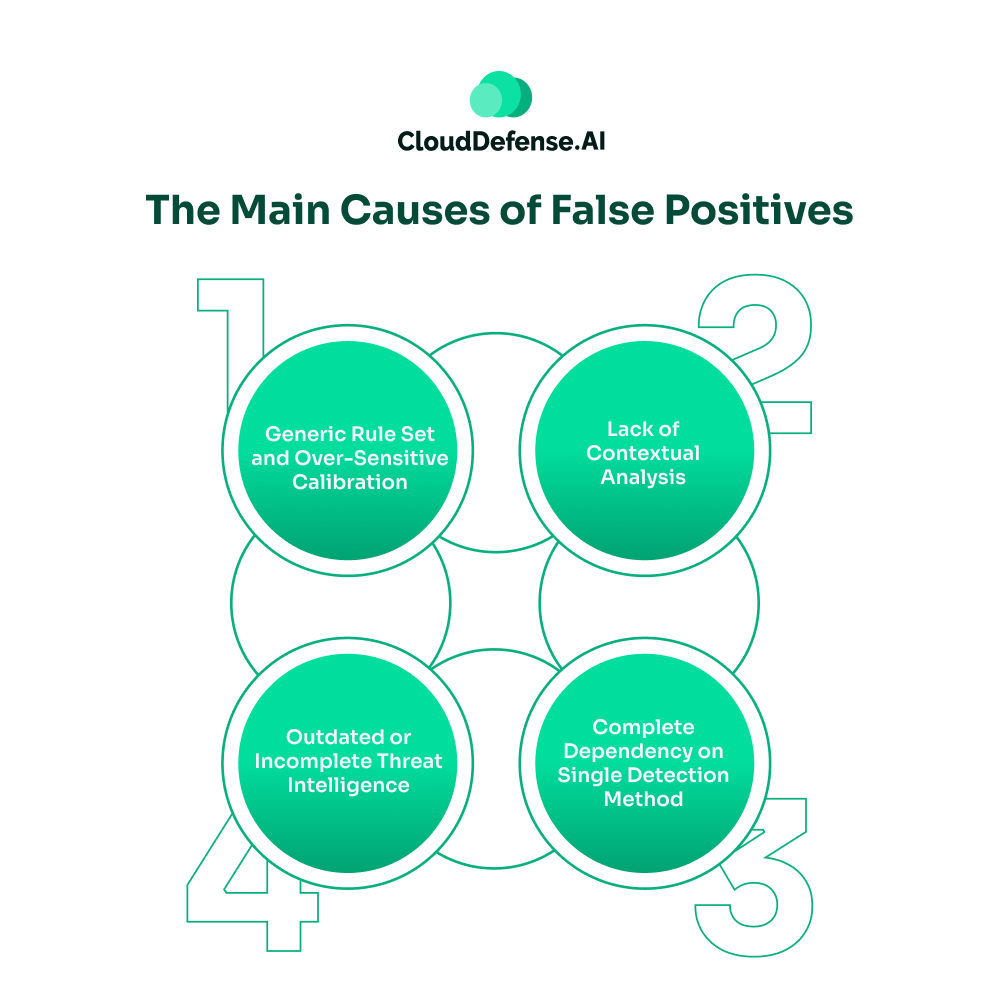
Now, it comes to the query “Why do false positives occur?” False positives are more than just noise; they are a serious threat to modern security strategies.
The false positives occur due to:
- Generic Rule Set and Over-Sensitive Calibration: Many SIEM, SAST, DAST, and other security tools come with a default set of generic rules that flag any unusual activity as a threat. Moreover, in many situations, organizations tweak the security scanners to be highly sensitive, which adds to the number. Any slight deviation or a benign activity that is used by developers for testing is flagged as a threat. Many teams fail to find the right balance when tweaking the sensitivity of the security scanners.
- Lack of Contextual Analysis: A lot of security scanners leveraged by enterprises lack contextual awareness needed to differentiate between benign and malicious activity. Usually, these security scanners don’t consider the business logic, the developer’s intent, and the application architecture while assessing any code or activity. A malicious activity in the test environment will lead to high alerts due to a lack of contextual understanding.
- Complete Dependency on Single Detection Method: A major reason behind the huge number of false positives is over-reliance on a single detection method. On many occasions, organizations only leverage a single detection method, which may be a tool or anomaly detection technique to identify vulnerabilities. However, no singular method or tool is 100% efficient, and they come with their own drawbacks. Since it has a narrow identified scope, it leads the tool to consider many benign activities as malicious.
- Outdated or Incomplete Threat Intelligence: Security scanners rely on the threat intelligence to accurately identify threats. Any security tool that uses outdated or incomplete threat intelligence can cause the tool to falsely identify a benign code or activity as a threat. Ultimately, at the end, the tool generates a huge number of false positives in the IDE.
Reduce False Positives in Security Tools: Numerous Effective Strategies
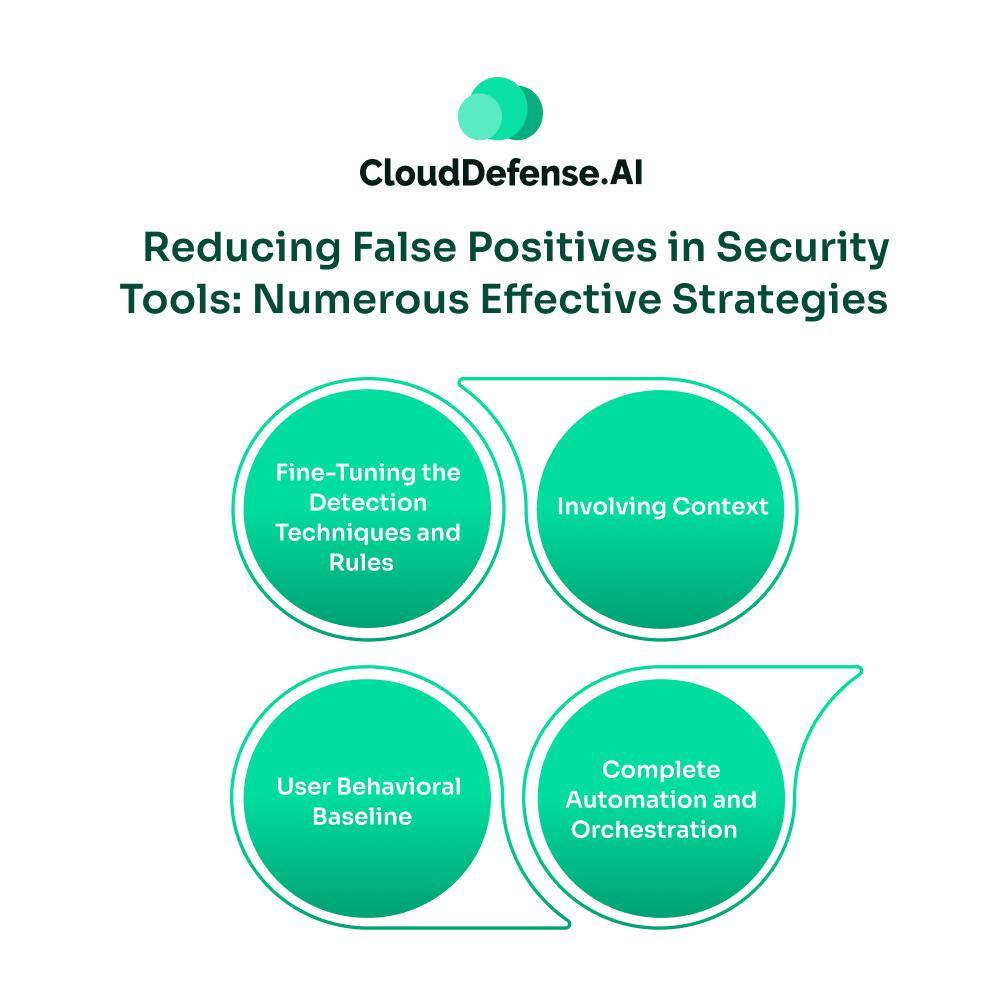
Reducing false positives in security tools requires a strategic approach. Enterprises need more than just fine-tuning the process and adding more tools. They need to adopt strategies that identify threats that only matter.
Some of these strategies can efficiently help teams with false positive reduction:
Fine-Tuning the Detection Techniques and Rules
Security teams can’t just tune the security scanners once and forget them. Such tuning is one of the major reasons behind the huge number of false positives. Security analysts need to regularly assess the SIEM and EDR signatures along with the identification logic.
Efficient alert tuning can help the team to focus on security alerts that matter most. If any of the signatures is generating a huge number of false positives, it needs to be restricted or tweaked to specific settings.
Involving Context
In modern times, context in security alerts offers security analysts and developers a significant advantage needed to cut through noise. The security scanners must be integrated with asset management databases, IAM systems, and all security tools so that the system can understand the context of all the security alerts.
It must be able to pull data from threat intelligence to identify whether a particular security alert is a threat or a false alarm. When an alert tells the teams about how the threat originated and what the severity level is, it improves the incident response.
User Behavioral Baseline
For reducing false positives in security tools, organizations need to move beyond systems that only use signature-based threat detection. It should involve security tools that leverage machine learning to automatically create a baseline for security flaws based on the user’s and device’s behavior and the organization’s infrastructure. It not only enables the system to trigger alerts when there is a deviation from the baseline but also overlooks any repetitive testing activity.
Complete Automation and Orchestration
Implementing complete automation through AI-powered security tools will help enterprises with automated triage. It will smartly prioritize alerts while eliminating all the false positives.
An organization can also involve advanced SOAR tools that will assist teams with initial automated triaging. It will not only help teams eliminate all known false positives but also avoid getting involved in the triaging process.
QINA Pulse: Helping Enterprises with Smart Prioritization
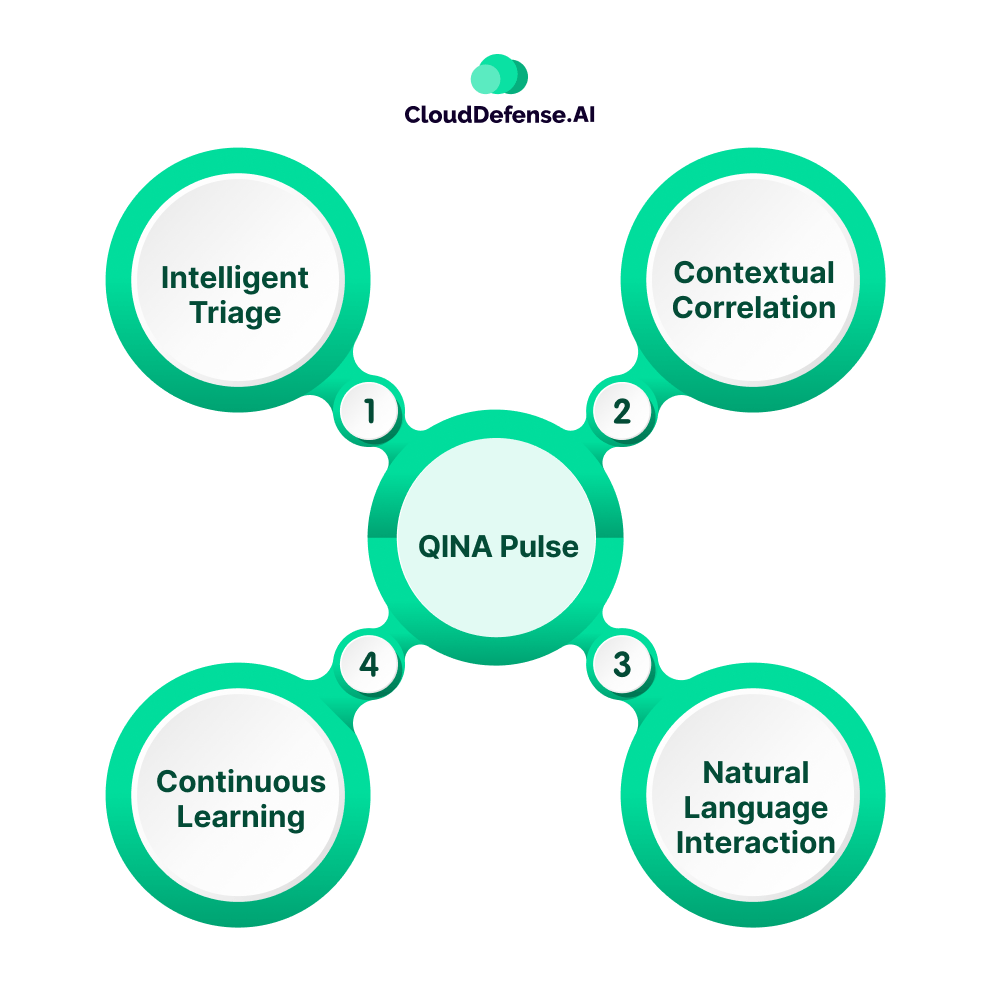
Alert tuning and implementing a behavioural baseline helps organization to strategically reduce false positives. But in today’s evolving threat environment, organizations need an AI-driven system that not only provides fewer alerts but also provides teams with prioritized alerts.
This is where QINA Pulse comes in and helps enterprises with significant false positives reduction through AI-powered intelligent and context-aware prioritization. Unlike other tools, Pulse serves as an intelligent security co-pilot that allows the team to prioritise alerts through simple commands.
It not only smartly prioritises the alerts but also details the reason behind the alerts along with remediation guidance. Pulse streamlines the false positives reduction process by involving:
- Intelligent Triage: A major feature of Pulse is its intelligent triaging process that utilizes a unique 4-stage analysis pipeline. It eliminates all the dead code and harmless activities, and presents the team with smart prioritised threat reports. It leverages AI and ML to understand the context behind each alert, minimizing false positives by almost 40%.
- Contextual Correlation: Pulse natively integrates with the organization’s environment, along with all the security, to ingest all the related data in one place. It helps the security assistant to correlate all the security findings and eliminate any redundant alerts.
- Continuous Learning: Pulse is always learning from all the decisions and discussions made by the team. When developers or security analysts mark a specific type of alerts as false positives or benign activity, it automatically adjusts to minimize similar noises in the future.
- Natural Language Interaction: Devs and security teams can interact with Pulse in plain English. Instead of switching to multiple dashboards, it provides the team with a real-time dashboard where they can put commands and minimize false positives in their alert queue. Developers can simply command “What are the top priority alerts in the queue?” It provides the team with a smartly prioritised list.
Bottom Line
False positives are a bane to modern application security, that is disrupting modern enterprises ‘ ability to cope with evolving cyberthreats. It not only damages an efficient security strategy but also allows real threats to get a delayed response.
In 2026, organizations with a clear vision of their threat posture will be the ones who can cope with modern threats. Organization by implementing context enrichment, intelligent tuning and behavioural baseline can help in reducing false positives in security tools.
However, enterprises that aim to achieve complete security resilience not only require false positives reduction but also intelligent prioritization with remediation guidance. Adopting AI-powered security assistants like QINA Pulse, organizations can stop going after false alarms and focus on security alerts that matter most.







