What is Cloud Data Protection?
Cloud data protection focuses on keeping sensitive company data safe in cloud environments. This involves securing data during storage (at rest) and while it’s being shared or transmitted (in motion).
To achieve this, organizations use tools like encryption, strict access controls, and continuous monitoring to prevent unauthorized access, data breaches, or loss. These protections are vital whether the data is managed internally or by a third-party provider. With more organizations adopting cloud-first strategies, the need for strong cloud data protection is growing.
A 2023 report by Flexera revealed that 89% of enterprises now use multiple cloud services. This shift highlights the importance of protecting data in today’s hybrid and distributed IT environments. As cyber threats grow, it’s more important than ever to keep cloud systems secure, strong, and compliant.
How Data is Protected in the Cloud?
Protecting data in the cloud is not just a technical necessity—it’s the backbone of trust in a digital-first world. As organizations migrate critical information to the cloud, the question isn’t just where data is stored but how it’s protected against threats. A cloud protection strategy involves using cutting-edge security measures to ensure data is confidential, intact, and accessible only to the right people at the right time.
- Encryption: Encryption is a cornerstone of cloud data protection. It transforms data into an unreadable format using complex algorithms, ensuring that only authorized users with decryption keys can access it. This applies both to data stored on cloud servers and data moving between users and applications, protecting it from eavesdropping and unauthorized access.
- Access Control: Restricting access is vital for cloud security. IAM systems assign specific permissions to users and devices, ensuring only those with legitimate needs can reach sensitive data. MFA adds another layer of defense by requiring multiple forms of verification before granting access.
- Continuous Monitoring: Cloud providers deploy advanced monitoring tools powered by artificial intelligence to detect anomalies and threats in real-time. These systems can flag unauthorized access attempts or unusual data activities, allowing organizations to respond swiftly and mitigate risks.
- Data Redundancy: To protect against data loss, cloud platforms maintain multiple copies of information across different locations. This redundancy ensures data availability and recoverability, even in cases of hardware failure or disasters.
These measures work together to protect cloud data while maintaining trust, compliance, and resilience in the face of evolving cyber threats.
Why is Cloud Data Protection Important?
Cloud data protection is critical in today’s digital age because businesses are increasingly storing their data in the cloud, where risks are often underestimated. Here’s why it’s so important:
Data is Scattered Everywhere
Companies aren’t just storing data in one location anymore. It’s spread across multiple environments—public clouds, private clouds, SaaS apps, and hybrid setups. This makes it difficult to know where all the data is, let alone secure it. Without proper safeguards, sensitive information could slip through the cracks.
Cloud Security Comes with Shared Responsibility
Cloud providers do a great job securing their infrastructure, but they aren’t responsible for protecting your specific data or managing access. That’s on the business. If you don’t actively protect what’s in the cloud, you’re leaving it vulnerable to breaches, misuse, or accidental exposure.
Cyber Threats Keep Growing
The rise in ransomware, phishing, and insider threats means businesses face constant risks. Cybercriminals target cloud environments because they’re often undersecured or misconfigured. Strong data protection measures act as a first line of defense.
Regulations Don’t Give You a Choice
Laws like GDPR, HIPAA, and others require companies to handle data responsibly. Protecting cloud data isn’t just about avoiding fines—it’s about staying credible and compliant in a highly regulated world.
Trust is on the Line
Every data breach you hear about erodes customer trust. People want to know their personal and financial information is safe. If a company can’t guarantee that, customers will look elsewhere. Strong cloud data protection reassures them their data is in good hands.
At the end of the day, protecting data in the cloud is about maintaining control, managing risk, and upholding trust. It’s not just a technical task—it’s a business priority.
Cloud Data Protection Statictics
Cloud data protection is essential as organizations increasingly rely on cloud environments for critical business operations. Here are fresh insights and statistics highlighting its importance:
- Cloud Data Breaches are Rising: In 2024, nearly 44% of organizations reported cloud data breaches, with 31% attributing these to misconfigurations or human error, emphasizing the need for strong IAM solutions.
- Multi-Cloud Complexity: The average organization now works with 2.02 cloud providers, and over 60% of them use more than 25 SaaS applications. This growing complexity makes managing consistent security policies and ensuring data privacy more challenging.
- Increased Cyberattacks on Cloud Infrastructure: Cloud management infrastructures have become prime targets for cyberattacks, with 72% of organizations reporting a rise in threats. This includes attacks on identity systems and data privacy breaches.
- Investment in Cloud Security is Rising: About 33% of enterprises are prioritizing investments in IaaS and PaaS security, but many still rely on traditional tools, indicating a gap in adopting advanced, cloud-native solutions.
- Growing Market Value: The cloud data protection market is expected to exceed $158 billion by 2024, driven by the urgency to protect against data loss, privacy violations, and regulatory non-compliance.
These trends highlight the need for effective cloud data protection strategies to mitigate risks, ensure compliance, and protect organizational data while on the internet.
Cloud Data Protection Challenges

With cloud data protection, organization benefits in many ways but securing data in the cloud also brings several challenges. Organizations have to overcome the following challenges to ensure optimum protection:
Encryption
Encryption is a big challenge in cloud data protection because it is not always available in the cloud environment, causing the data to be vulnerable. While the data are in transit, many applications encrypt them making it difficult for the organization to identify any anomaly or potential leaks.
A Google Transparency Report stated Google emphasizes encryption so cloud data protection that doesn’t control the data will lack the sessions, leading to data exposure.
Visibility
Modern organizations operate on multi-cloud infrastructure and lack control over their data hosting infrastructure, resulting in a lack of visibility. Moving workloads and limited information from data protection also limit visibility and make it difficult for the administrator to track what data they store and where they are located.
Without comprehensive visibility, the security team won’t get granular control and can’t identify potential data leaks and access activity.
Configuration Management
Every cloud service provider offers a set of security settings that the user has to properly configure to protect the data in the cloud. However, managing the configuration and ensuring no data is stored in a public repository can be a big challenge because a misconfiguration can lead to data exposure.
Cloud-Focused Design
Like traditional infrastructure, cloud data protection also comes with a unique set of security issues. Organizations have to look for a data protection solution that is designed to protect the data in the cloud; otherwise, it will lead to various security gaps.
Complex Data and Application Interaction
Nowadays, the data of an enterprise is constantly utilized by various applications hosted on various cloud environments.
This leads to complexity in the interaction between application and data storage locations which ultimately makes it challenging to implement effective least-privilege access control. To achieve optimum cloud data protection it is important for a solution to properly define least-privilege control.
Inconsistent Approach By CSPs
When it comes to data protection in the cloud, every cloud service provider has their approach and ability, causing inconsistency in approach. This inconsistency in approach towards cloud data protection leads to many security threats. Cloud data protection solution needs to implement security measures that will address this consistency.
Maintaining Data Confidentiality Level
Another challenge of cloud data protection is maintaining data confidentiality level and limiting access to sensitive data depending upon the requirement. As data is constantly utilized by different entities and devices, maintaining confidentiality levels becomes an issue.
The best way to address this challenge is by developing a strategy that limits access and implements restrictions on access to highly sensitive data.
Benefits of Cloud Data Protection
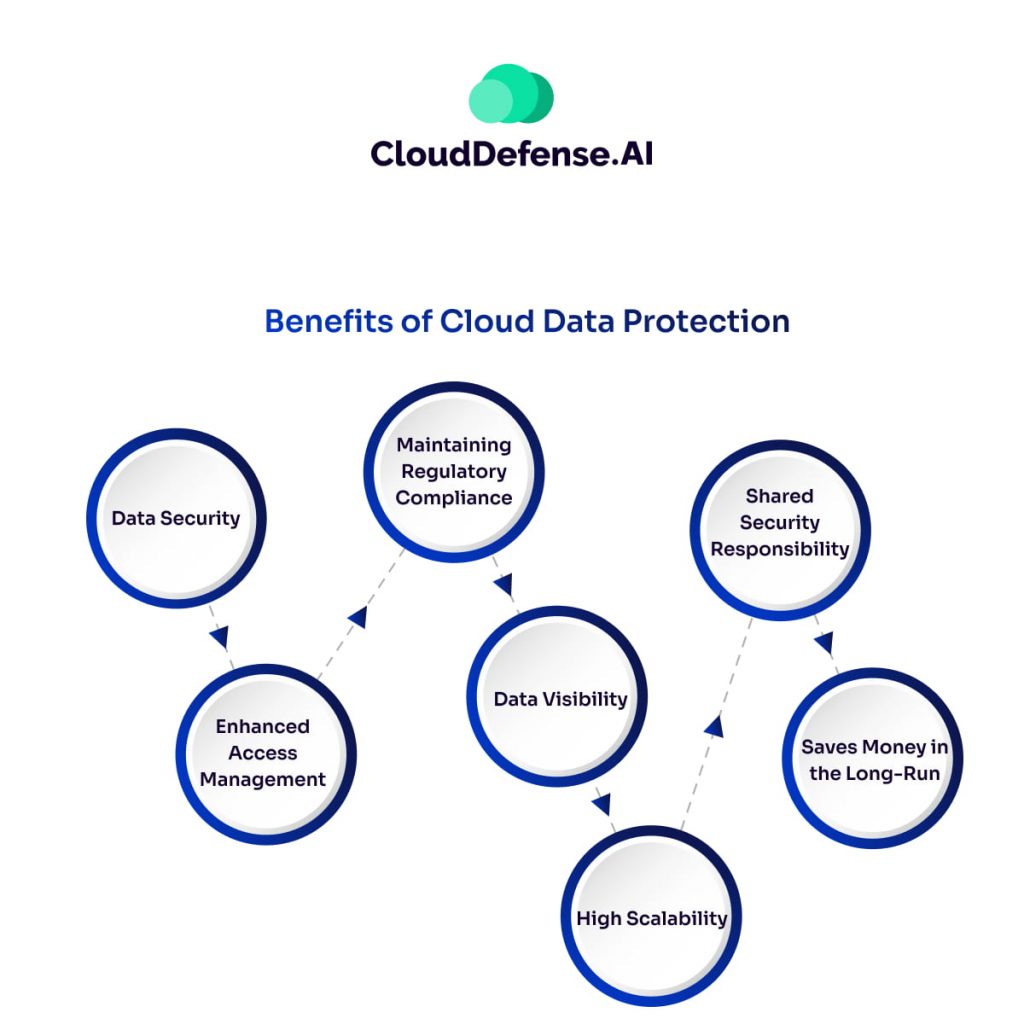
Cloud data protection and cloud computing go hand in hand allowing organizations to ensure optimum safety and protection standards for data without the risk and maintenance of traditional storage options. A robust cloud data protection will offer you many benefits and they are:
Data Security
The biggest advantage of cloud data protection is the data security it has on offer. It utilizes various techniques, tools, and methodologies along with monitoring to discover potential data loss and exfiltration and prevent them from happening.
Proper implementation of this solution ensures all the sensitive data are protected across the cloud while maintaining integrity and availability.
Enhanced Access Management
Cloud data protection is based on least privilege access control and it helps in controlling who can access which data and what they can do with it. Users or devices with the right authorization and adhering to established guidelines can only access the data.
Strong cloud security also helps in limiting access to sensitive customer and corporate financial information.
Maintaining Regulatory Compliance
Every organization has to meet specific industry regulations like GDPR or HIPAA while they store and process sensitive customer information. Optimum data protection is one of the common requirements for every data protection regulation.
Cloud data protection helps in adhering to regulatory requirements by implementing various techniques and enforcing policies. The availability of audit trails and logging details due to complete visibility makes compliance adherence much easier.
Data Visibility
With the implementation of cloud data protection, an organization can implement zero trust access control where all the access requests are assessed based on different criteria. It enables the administrators and security team to get complete visibility into how the data is being used and where they are stored.
High Scalability
Cloud data protection serves as a scalable data security solution that helps you maintain optimum data protection as the data volume grows with time. The best thing is that with high scalability you won’t have to make additional arrangements for hardware and maintenance.
Shared Security Responsibility
Most reputed third-party cloud providers employ robust security measures for the protection of the data in the cloud. Through shared security responsibility, they also help enhance the overall cloud data protection and ensure the cloud data is always protected.
Saves Money in the Long-Run
Having robust cloud data protection helps organizations save money in the long run. As this solution takes a proactive approach to identifying threats, it not only helps in saving additional resources but also the workforce required to mitigate an issue and eliminate impact after a breach.
How Companies Can Protect Data in Their Cloud Environments?
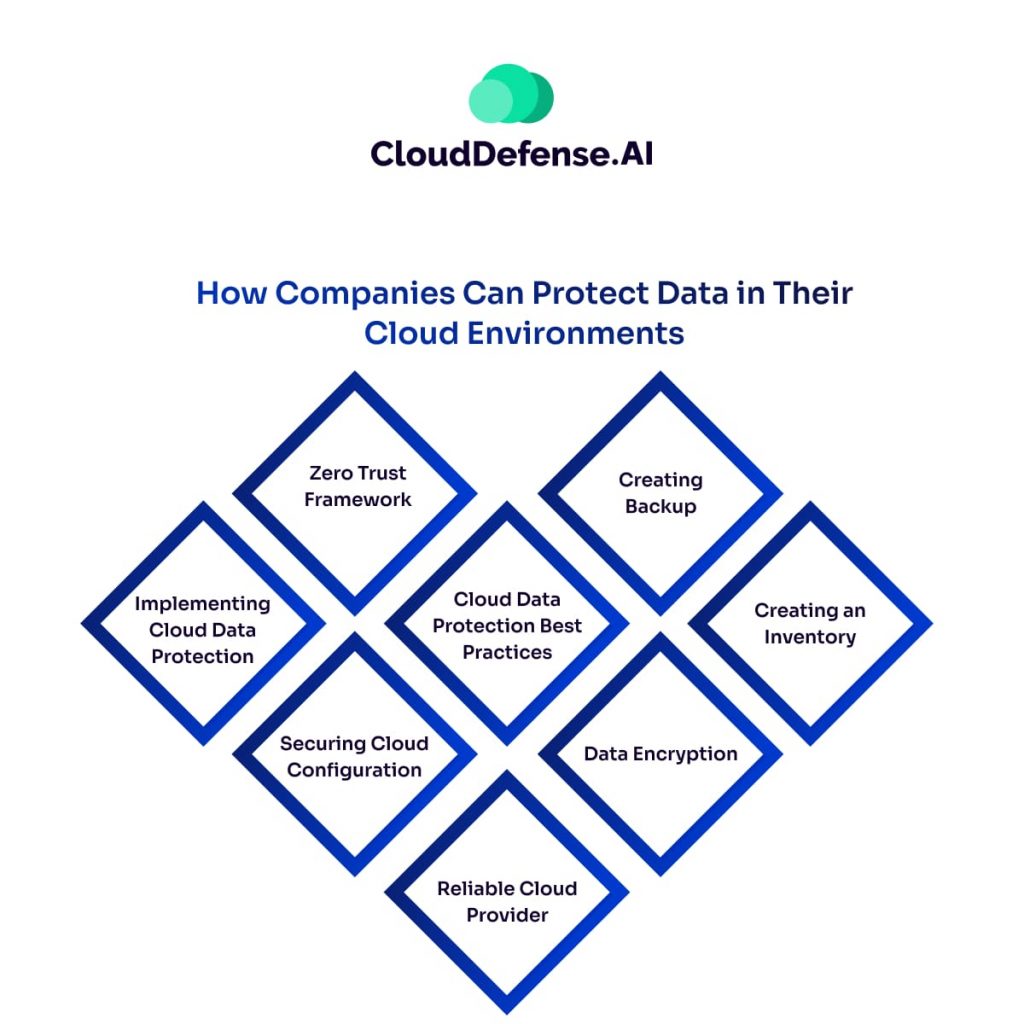
When it comes to protecting data in your cloud environment, you can opt for the following ways:
Implementing Cloud Data Protection
The best way for an organization to protect its data in the cloud environment is by employing a robust cloud data protection solution. The solution that you will implement should offer performance and scalability which will ensure it offers consistent data protection through the multi-cloud environment.
Zero Trust Framework
For comprehensive cloud data protection, organizations need to establish a zero-trust framework that will help you in ensuring only trusted users have access to sensitive information.
A Zero Trust framework will utilize all the context associated with users and applications to build trust for a secure connection. Moreover, the Zero Trust framework will also ensure that only authorized users will have access to the organization’s resources and data will be safeguarded from cyber threats.
Securing Cloud Configuration
Along with the Zero Trust framework, having a cloud security posture management solution will help in protecting the cloud data.
It performs monitoring across the infrastructure and remediates any misconfiguration, as a result, it prevents any risk that will enable cyber attackers to get access. It also ensures cloud environments are always securely configured because it will maintain a data security posture.
Reliable Cloud Provider
Choosing a reliable cloud provider is also a criterion for enterprises because a cloud provider with robust policies and security technology will help in safeguarding the data. They should meet your organization’s security requirements and adhere to industry standards.
Data Encryption
Data encryption is often utilized by organizations to protect them from exploitation and unauthorized access. If your organization deals with a high volume of data that are processed, stored, and transmitted for business operation, encryption can help you protect them.
Creating Backup
Every organization should create a backup of all their data and they should be protected at a similar level as the original one. Having a secure backup will be useful in the event of a data breach or natural disaster.
Creating an Inventory
To effectively protect all the data, an organization needs to create an inventory by performing an audit of all the data stored in the cloud. It is vital for your organization to know what all the data they store because then only they can completely protect the cloud data.
Cloud Data Protection Best Practices

When you are using the cloud to store all the data of your organization, you need to follow certain best practices.
Incorporating these practices into your security strategy will not only keep them safe but also prevent unauthorized access. Here are the best practices you should follow:
Backup All The Data
While protecting all the cloud data, it is a good practice to create a secure backup of all that data and store it in a remote location. The cloud data should be backed up at regular intervals and using automation is the best way to carry out the backup process.
Having a backup is vital for regulatory compliance and it will help you recover the data in the event of a data breach, system failure, or natural disaster.
Utilizing Authentication and Encryption Together
Many organizations prefer to use authentication to keep the data protected from unauthorized access. However modern attackers are coming up with ways to impersonate identities and gain access to sensitive data.
However, when authentication is coupled with encryption, it provides an additional layer to the data as users will need an encryption key to access the data.
Assess the Inbuilt Security
The security provider looking after the security posture of your organization must come equipped with technologies, tools, controls, and policies that will ensure the protection of the data all the time. The cloud provider should communicate about their compliance policy with your organization and help you build the security strategy accordingly.
Robust Credential Policies
Another best practice that you should follow is to maintain a robust credential policy that will limit the access of users to sensitive information. Having such a policy in place, will not reduce attack surface but also prevent data breaches.
Utilizing File-Level Encryption
To enhance the protection of cloud data, you can make use of file-level encryption for the additional layer of security. File-level encryption helps in fragmenting the data and storing them in an alternate location, helping your organization to minimize security breaches.
Select a Reliable Cloud Service Provider
Always select a cloud service provider with a high reputation and offer best-in-class security measures to protect the data of the clients in the cloud.
Ensure the cloud service provider is transparent about their security policies and uses all the necessary tools and measures to prevent any attack. Even if there is a security breach, they should have plans to handle those breaches. You can expect such commitment and optimum security from CloudDefense.AI.
Monitoring the Cloud Activity
It is vital to monitor all the cloud activity, especially what users do with the data. You should review the logs of all the activity and uncover any suspicious activity that might comprise the sensitive information. Having the support of real-time monitoring will help you with constant monitoring and quickly get a report when it identifies any anomaly.
Secure all the Devices
To protect all your cloud, you also need to secure all the devices, especially endpoint devices in a network, because they are vulnerable to attacks and data leaks.
The endpoint devices are connected to the network of the organization, so a breach in one endpoint will infect all the devices and the data they store. You should implement additional security protocols and endpoint protection to prevent attackers from breaching the security perimeter.
Conclusion: Cloud Data Protection with CloudDefense.AI
Cloud data protection is a necessity for every organization as they store, process, and transmit data. CloudDefense.AI has emerged as the trusted vendor that has not only helped organizations build top-notch data protection in the cloud but also helped them implement a zero-trust network.
Why Choose CloudDefense.AI?
- Comprehensive Security Features: CloudDefense.AI provides real-time monitoring, rapid incident response, and advanced threat detection to safeguard your data against evolving threats. By employing a Zero Trust policy, the platform ensures backdoor data access is eliminated, intrusion points are minimized, and roles are segregated effectively across team members to reduce risks.
- Compliance Made Simple: Compliance failures can be costly, but with CloudDefense.AI, you’re always audit-ready. The platform leverages its AirTight Checklist to help you easily meet regulatory requirements, ensuring your organization stays compliant with frameworks like GDPR, HIPAA, and PCI DSS.
- Third-Party and Application Protection: CloudDefense.AI extends its protection to third-party applications, preventing attackers from exploiting vulnerabilities to infiltrate your network. This added layer of security ensures end-to-end protection for all your cloud assets.
- Advanced CSPM Solution: As an industry leader in Cloud Security Posture Management (CSPM), CloudDefense.AI excels in detecting multi-cloud threats, identifying misconfigurations, enforcing custom security policies, and deploying AI-driven remediation. Its holistic approach ensures your cloud infrastructure remains resilient against threats and vulnerabilities.
By choosing CloudDefense.AI, organizations can confidently protect their data from every angle, ensuring safety, compliance, and resilience in today’s cloud-driven world.







