In today’s digitally connected world, the importance of cybersecurity cannot be overstated. With the increasing reliance on online platforms and services, protecting sensitive user data is of paramount importance. Unfortunately, security breaches are not uncommon, and the latest revelation regarding Internshala’s security breach by CloudDefense.AI has sent shockwaves through the online community. In this article, we will delve into the details of this security breach, how it occurred, and its potential impact on users.
Understanding the Internshala Security Breach
What is Internshala?
Before we dive into the breach itself, let’s briefly introduce Internshala. Internshala, one of the leading online platforms for internships and training, has recently been subjected to a significant security breach. It has gained widespread recognition for its role in helping individuals kickstart their careers.
The Role of CloudDefense.AI
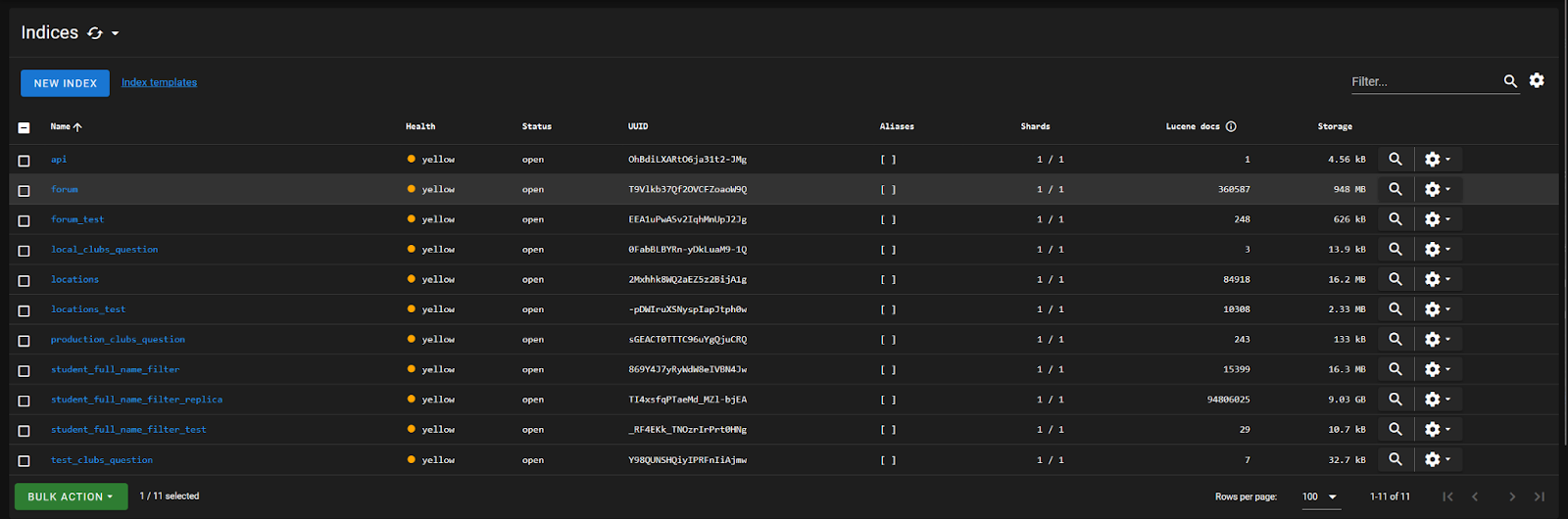
CloudDefense.AI security researchers have discovered a critical vulnerability in the ElasticSearch service hosted on the platform’s asset. This security flaw allows unauthenticated access to the ElasticSearch server, potentially compromising sensitive data and exposing Internshala and its users to various risks.
CloudDefense.AI reached out to the Internshala team on the 6th of April and they have taken the necessary steps to fix the issues.
Unauthenticated Access to ElasticSearch
The security researchers found that the ElasticSearch service hosted on Internshala’s asset was accessible without any authentication. This means that an attacker, without needing to provide valid credentials, could perform a range of sensitive actions on the server. These actions include viewing, modifying, or even deleting data stored within ElasticSearch. The lack of proper access controls significantly increases the risk of unauthorized access and potential data compromise.
Affected Host
The ElasticSearch server vulnerable to the security breach can be accessed through a URL. (We can not share the URL in public)
Proof of Concept
To demonstrate the severity of the vulnerability, the CloudDefense.AI security researchers have successfully conducted a proof of concept, showcasing how an attacker could exploit the unauthenticated access to ElasticSearch.
Impact
If an attacker gains unauthorized access to the ElasticSearch server, several severe impacts may occur:
Sensitive information indexed by ElasticSearch, such as customer data, credentials, or proprietary business data, could be accessed or exfiltrated. This puts Internshala’s users and their confidential information at risk.
An attacker could manipulate or delete data stored within ElasticSearch. This could lead to data integrity issues, potentially disrupting Internshala’s operations and affecting the reliability of the platform.
The absence of access controls enables an attacker to expose data to unauthorized entities or even the public. This can have serious consequences for Internshala’s reputation and trustworthiness among its user base.
Conclusion
The Internshala security breach, uncovered by CloudDefense.AI, serves as a stark reminder of the ever-present threats in the digital landscape. It underscores the critical importance of robust cybersecurity measures for all online platforms. Users must remain vigilant and take precautions to safeguard their personal information in an increasingly interconnected world.
Related Articles:






