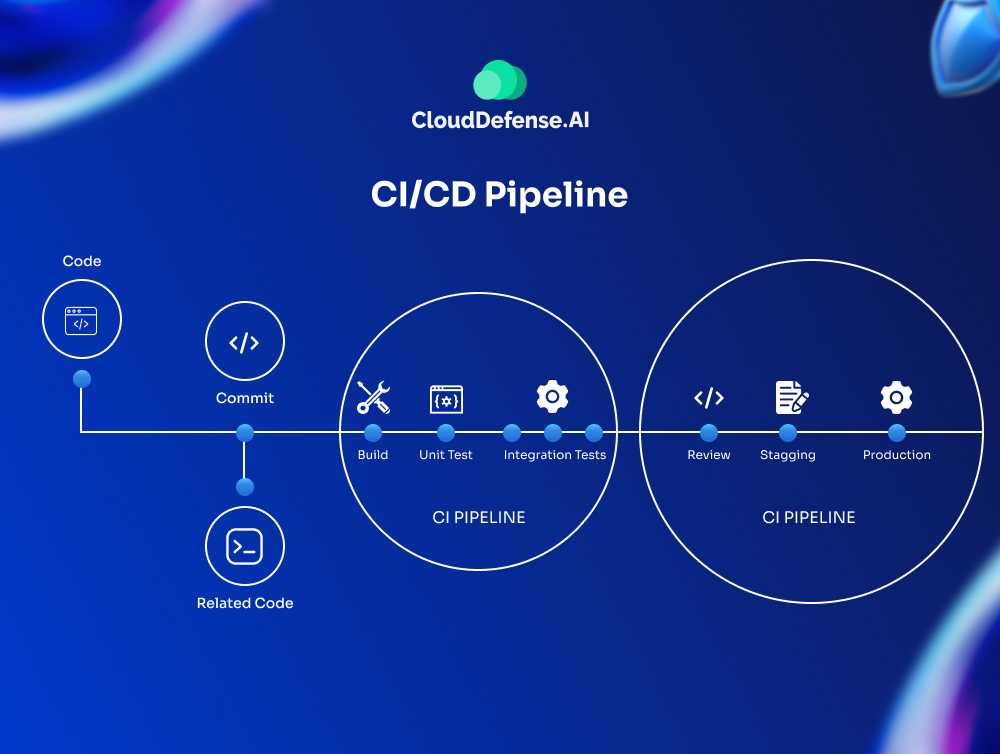
Many enterprises are adopting CI/CD methodologies in order to bolster and streamline their application development life cycles and content delivery cycles.
However, enterprises must adopt CI/CD along with their best practices available in order to fully benefit from these strategies and really leverage them to their greatest extent.
“CI/CD” stands for both continuous integration and continuous delivery. Continuous integration refers to, of course, continuously integrating code, usually utilizing an easy to access repository for an application’s codebase. Such a repository is shared between developers.
Meanwhile, continuous delivery refers to developers taking code stored in said repository and continually delivering it in pieces or manageable chunks all the way throughout a production or development pipeline.
Combined, both strategies can result in a fast and effective development process, helping enterprises beat their competitors to market and increasing customer satisfaction overall.
Both terms are placed next to one another to represent a methodology or series of strategies designed to ensure that software is:
- Continuously improved and that new quality tests are always being implemented
- Built using robust and automated tools when appropriate
- Continually delivered to customers or end-users in as good a state as possible
Basically, CI/CD is a methodology that helps enterprises produce good software with a minimum of coding errors or security flaws. It can result in streamlined and extremely efficient software development lifecycles.
CI/CD methodologies

When properly utilized, CI/CD methodologies will allow an enterprise to benefit from:
Generally Smaller Code Changes
Basically, CI/CD strategies let you integrate smaller pieces of code into your overall application at a time. Small code integrations are simpler and easier than integrating much larger swaths of code.
This has the overall effect of making content delivery more consistent and reducing the number of errors or pipeline lag your team might otherwise experience.
Isolating Faults or Errors
Again, through continuously integrating small chunks of code instead of updating an entire application with a larger piece, it’s much easier for quality assurance teams and developers themselves to identify and locate certain errors, especially repeated ones.
This, in turn, will allow enterprises to take care of those problems before they become hard to control or dominate a development lifecycle, and will heavily improve enterprise cyber protection.
Lower Recovery or Repair Times
In more specific terms, successful CI/CD implementation usually results in a faster MTTS or mean time to resolution.
Since faults can be more easily isolated and tracked using CI/CD methodologies, your quality assurance team will also be able to fix those faults more quickly.
Better Test Reliability
Since CI/CD relies on developers implementing bite-sized code changes or using smaller, more localized tests, any testing tools utilized will be more reliable and consistent.
Continuous reliability usually rises significantly, which also helps teams push out the best version of an application possible at the end of every software development deadline.
Faster Release Rates
By leveraging CI/CD to the best of their abilities, enterprises will usually benefit from faster lease rates for their applications.
That’s because fewer errors will make it to the end of the development pipeline, causing errors or faults that take a long time and a lot of money to fix before the application is released to the end-user.
Better Customer Satisfaction
Above all else, CI/CD methodologies are about improving applications when they reach their end-users.
Fewer bugs, faster release cycles, and generally more secure code all combine to create a better end-user experience and greater customer satisfaction for enterprises
While CI/CD as a methodology has many potential benefits, successfully implementing these strategies requires serious consideration and adaptation of best practices. This guide will break down the best CI/CD practices for enterprises to use to help them adopt CI/CD as their primary methodology.
CI/CD Best Practices – Our Top Picks

There are many good practices that CI/CD strategies rely on for successful and effective implementation. Fortunately, DevOps teams often utilize many of these same practices, so many developers won’t have too much trouble adopting them.
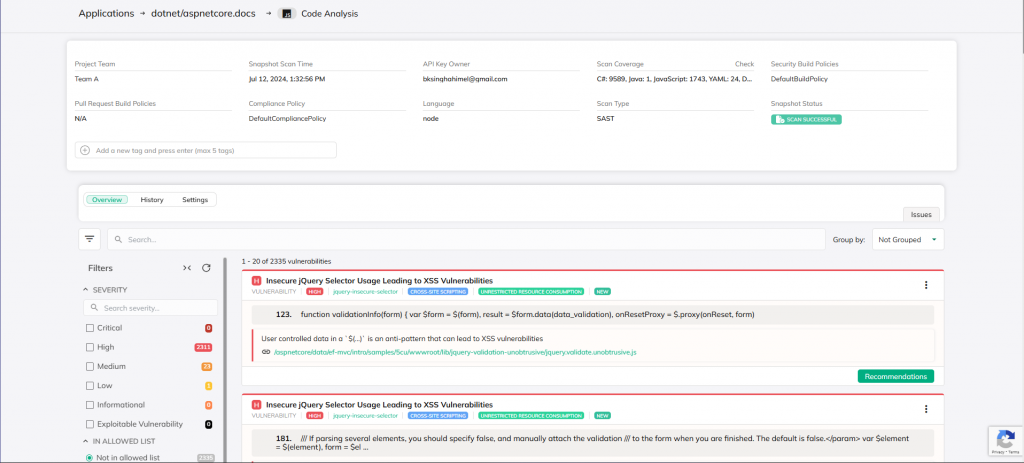
Focus on Security First and Foremost

The best initial practice to adopt is focusing on security above other factors, and especially shifting security to the “left” of your development pipeline.
In simpler terms, this means allowing your security team to prioritize security tests and analyses of written code earlier in the development process.
It also means training your developers themselves to implement security tests and write code more securely in the first place.
This is an important practice because it can help enterprises detect web application security breaches and potential vulnerabilities before more code is written on top of an embedded security risk.
Emphasizing Prevention, Rather Than Amending
By detecting security flaws early, they can be taken care of and solutions can be integrated before more code is written. Fixes are always easier to implement before an application becomes too complex.
Lots of security issues end up becoming difficult to deal with later down the road because they allow hackers access to an application in such a way that a quick and easy patch is not possible.
By adopting security tests and other procedures earlier in a development pipeline, more errors will be caught earlier, costing an enterprise less time and money to take care of any security flaws.
To really dig deep into this practice, enterprises would be wise to train their developers in security procedures as part of their regular educational updates.
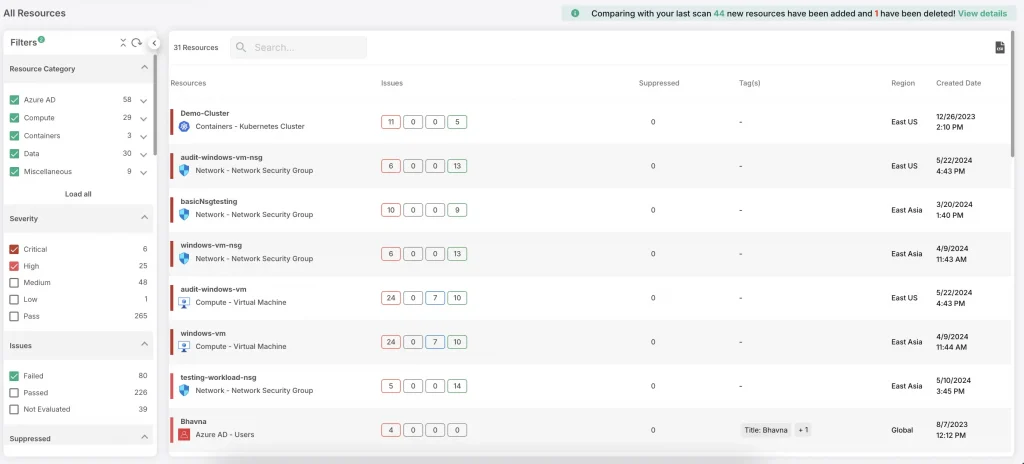
Keep Your CI/CD Environment Secure

Another excellent practice for CI/CD pipelines is to isolate and secure the CI/CD environment or repository. This is because your CI/CD systems or repository have some of the most critical digital infrastructure and enterprise can protect.
After all, a CI/CD repository will have complete access to a shared code base and likely include lots of credentials used to deploy code in various environments.
Thus, it’s essential that enterprises safeguard their internal data and keep their CI/CD environments as airtight as possible.
It’s particularly important as well because your CI/CD might have automatic access to multiple different networks in order for your developers to easily deploy code to different environments.
Isolating Your CI/CD Repository
Therefore, if your CI/CD repository isn’t properly isolated, any intruders or hackers might be able to reach multiple different networks from a single entry point just by gaining access to your CI/CD environment.
This can cause a cascade of security failures and lead to the total collapse of an application and related code.
It’s a good idea to deploy CI/CD to internal and protected networks that can’t be reached or accessed by outside parties. Enterprises might also consider setting up network access control technology, like VPNs, to ensure that only authenticated operators can access said repositories.
What Is the Solution
Of course, your particular solution to this problem will vary significantly depending on your network’s topology and other factors. For instance, maybe you have other management or development requirements that make utilizing a VPN a no-go.
But the bottom line is the same: your CI/CD environment should be as isolated as possible. Shield all external access to your servers if you can and make sure that the people who can access your CI/CD repositories are trusted and practice good digital hygiene.
This includes changing your passwords regularly, not giving out company information, and so on.
Keep Parity with Production
What does parity with production mean?

In a nutshell, many CI/CD pipelines produce code changes through a number of deployment environments and associated testing suites.
When bite-sized chunks of code pass certain requirements for one stage, they are often automatically deployed or queued for deployment into subsequent environments, even if they are more restrictive.
This is done because, if CI/CD methodologies are being followed correctly, any code pushed to production should be vetted for security flaws and general functionality anyway.
In the later stages of your development pipeline, it’s a good idea to reproduce your production environment as closely as you can in any subsequent testing environments.
How Does Parity Help?
This will ensure that the tests can accurately reflect how any code changes or errors might actually appear when deployed for the end-user of your application. This is important so you avoid finding accidental but significant differences between your staging and production environments.
More importantly, it stops you from producing a solution to a problem that only occurs in a test environment.
In other words, limit the number of differences between your testing environment and your hypothetical live environment. The more differences you have, the less stable your code will be and the less reliable your tests will be as you try to measure code performance or potential security flaws.
It’s crucial to keep any differences (and there will undoubtedly be at least several) as manageable as possible.
One potential idea is to utilize blue-green deployments – these allow enterprises to swap traffic between two almost identical environments and alternate those environments between being for staging and designated production.
Or you can use scaling to your advantage. For instance, an enterprise could deploy identical code and infrastructure from a production environment to a staging environment, just at a lower scale, to see any possible effects or vulnerabilities.
Run Fast Tests Early and Locally in the Pipeline
There are several CI/CD practices concerned with testing frequency and timing.
For one, it’s a great idea to run all of your fastest tests early. Most developers will undoubtedly discover that parts of their testing suites will be faster than others.
Since CI/CD systems serve as pipelines or conduits for any changes into your application or system, it’s vital to discover problems as early as you can so it takes less manpower and money to fix any problematic code.
To more quickly and consistently identify issues, it’s therefore wise to run all of your fastest tests first. Your developers can then identify and fix any small issues that might have come up with longer and more complex tests anyway. This provides a number of big benefits:
- It helps developers understand the performance impact for certain tests
- It allows developers to complete the majority of their testing requirements early
- It catches particularly easy or basic code flaws early that might have otherwise led to more complex failures
It’s also a good idea to run any tests locally if possible before you commit a chunk of code to your CI/CD system pipeline. Indeed, developers should be encouraged to run local tests before they commit code to the shared CI/CD repository in order to avoid hampering or inconveniencing fellow team members.
While it’s true that most developers won’t be able to run an entire test suite in a fully production identical environment, developers should be able to run at least some basic tests. They’ll feel more confident about code they contribute to the shared repository if they take this step.
One good idea is to make sure that developer testing suites can be run with simple commands from almost any environment. This makes for easy testing for developers and can potentially be integrated into automated tests later down the road.
Similarly, Automate Tests Where Possible

Speaking of automation, CI/CD systems could benefit from developers taking a page out of the DevOps book and utilizing automated tests wherever possible.
There are plenty of automated CI/CD tools and testing suites for testing code both from an inside perspective and from an outside perspective. Check out our guide on DevOps.
Why focus on automated testing? In short, because developers are often more focused on producing code and moving on to the next thing than they are focused on making sure any existing code is airtight and works as well as possible.
This isn’t necessarily a flaw, but it is a tendency that most developer teams share as opposed to quality assurance teams.
By automating security and coding flaw tests, your developers will be alerted to potential issues as they write code, making it easy for them to go back and make necessary changes without feeling overly slowed down or inconvenienced.
It also helps ensure that quality CI/CD standards are being maintained throughout your team, even if you have some developers who are taking a little while to adopt the new methodology.
Run Your Tests in Ephemeral Environments
If you want to make sure that your tests all run the same regardless of the coding stage, your best bet is to use a clean and ephemeral testing environment if you can. Many CI/CD practitioners will run tests in specific containers.
This removes the differences between host systems. You might also consider providing a standard or shared API that developers can use to link different components together at different scales.
This methodology provides a lot of benefits. For instance, it makes your testing infrastructure much more portable. Furthermore, developers will have a much easier time replicating certain configurations for tests that can be used later in the pipeline.
Containers can also be spun up relatively easily as soon as they are needed, then destroyed when the testing is done. This, in turn, means that developers can make their testing environment much more accurate without having to consider wider changes.
All in all, ephemeral environments make testing a lot easier and more “compartmentalized” for your developers.
Utilize Tracking and Version Control Tools
Another great CI/CD practice that enterprises can implement is the utilization of version control and tracking CI/CD tools.
Tracking tools are particularly advantageous – examples include Bugzilla and Jira, both of which can help your teams achieve better visibility into how a particular application is progressing.
Furthermore, these tracking tools can help your developer teams collaborate with distribution teams fairly easily as well.
Tracking Codes With Git
There are other fantastic version control tools, too, like Git. Git creates one collaborative source for tracking code changes and version checking.
Many enterprises have already discovered that it’s fantastically useful whenever code rollbacks are required or whenever a particularly deeply-embedded bug is wreaking havoc on a current version of software.
These CI/CD tools make your team’s quality assurance tasks a lot easier and help your teams collaborate with one another. Plus, many version control and tracking tools work naturally with the shared repository that’s at the heart of most CI/CD strategies and pipelines.
Build Code Only Once

With CI/CD, the goal for enterprises should always be to build code once. By building multiple versions of code, your team encourages branching and makes maintenance or security testing an exponentially more difficult task.
Other workloads can also grow exponentially if your team builds code multiple times.
If you want to most successfully implement CI/CD strategies, get your developers to include the building process as their first step in their development cycle.
This will get your team in the habit of packaging your written software in an overall clean environment that can reduce the chance for errors and eliminate multiple oversights, as well as make future errors less likely.
Don’t Branch! Commit Daily Instead

Similarly, CI/CD adherence would do well to reduce or eliminate branching as much as possible.
Branching basically refers to writing slightly different versions of code that eventually branch out into wildly different codebases that take a lot of time to reconcile and integrate with one another.
Remember, this is anathema to the entire CI/CD philosophy, which focuses on bite-sized integration of code through continuous integration and continuous development and delivery.
Developers Commitment to the Job
Developers should commit directly to the main branch of code, or merge changes with the main branch from their local branches at least once per day.
This helps developers stay on track and maintains a collaborative spirit, while also forcing developers to deal with smaller but more manageable integration challenges instead of allowing exponentially more difficult integration pain from piling up over time.
It’s a lot harder to merge tons of different branches into a single main branch during crunch time than it is to merch a local branch that varied a little bit during the day every day, even if it takes a few minutes from each developer at the end of their shift.
Again, this type of change may get some pushback from developers used to doing things a certain way, but it’s overall worth it in the end.
Release More Often
One other way you can implement CI/CD practices for success is to release your software as often as possible. Of course, this is only an option if your software is in a release-ready state and it has been thoroughly tested for security flaws and other major vulnerabilities.
Still, if an enterprise’s software is at this stage, releasing more frequently is a great strategy.
Enterprises with software that isn’t at a release-ready state can also add an additional deployment stage to their pipeline that almost identically resembles the production environment.
Either way, enterprises can:
Practice Canary Deployment
Which involves releasing software to a specific subset of users. The users then test the software base and check it for errors. If none are found, the software can then be rolled out to the wider population or rolled back if the reverse is true and more iteration is required.
Blue-Green Deployment
Which involves using two identical production environments. The first is idle while the other is alive and in production. As soon as a new release is rolled out, any changes should be moved to the idle environment.
The enterprise can then switch the environments so the formerly idle one is now active. This has the effect of creating a “safe” version of the software that can be immediately rolled back to if something goes wrong with the new release.
But if everything goes smoothly, both environments can be brought to parity for the next development cycle.
A/B Testing
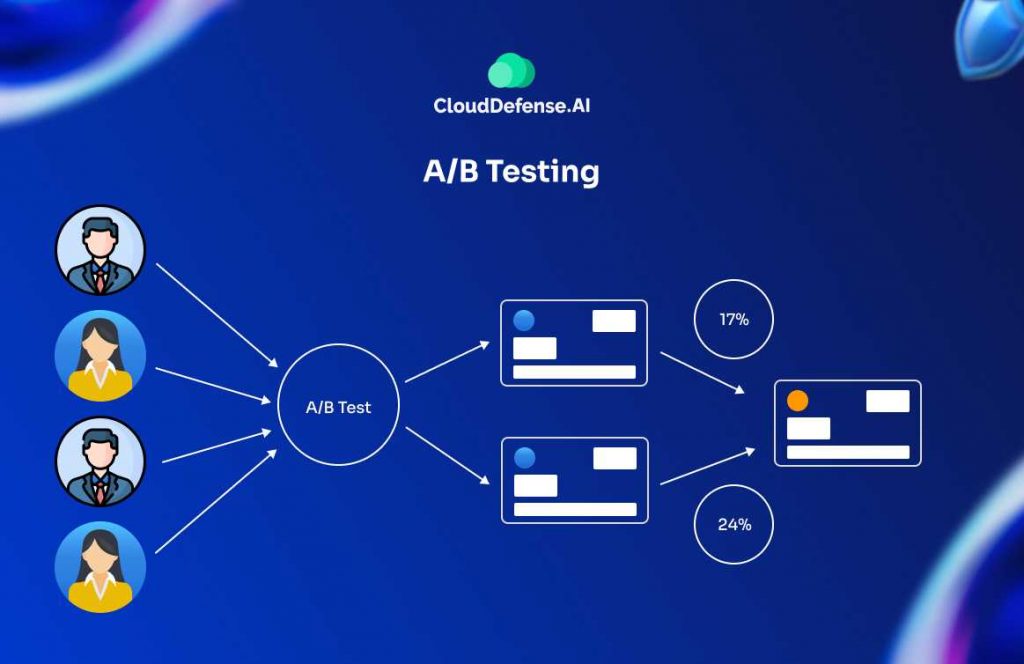
Which is similar to blue-green deployment, though it’s different in other ways as well.
A/B testing focuses more on testing specific features within an application for things like user-friendliness or security. Enterprises can utilize this kind of testing to see which version of a feature, for instance, performs better overall
Bottom line: releasing your software more frequently gives you valuable data with which you can iterate future efforts and utilize to make sure each new version of the application is better than the last.
Conclusion
Overall, CI/CD practices are intended to help enterprises and development teams produce the best software possible and minimize the pains common with integrating multiple branches or checking for security flaws.
It’s an attractive philosophy because it breaks down many of the largest and most time-consuming aspects of a development cycle into more manageable chunks.
Consider utilizing CI/CD practices for your own enterprise to see the benefits described earlier in action.







