Unified Threat Management, or UTM, stands as a pivotal solution, offering a consolidated approach to network security.
Defined as a singular security appliance or solution, UTM provides a centralized point for various security functions, ranging from anti-spyware and antivirus to intrusion detection and prevention, network firewall, content filtering, and leak prevention.
As the technological space continues to become more sophisticated, UTM emerges as a comprehensive defense mechanism against diverse cyber threats.
In this article, we explore the essence of UTM, exploring its features, benefits, and challenges. Keep reading to be equipped with essential insights to strengthen your network security strategies.
So, let’s dive right in!
Unified Threat Management Definition
Unified Threat Management, or UTM, is an information security system that integrates various security features and services into a single device or solution within a network. Unlike traditional antivirus tools, which focus on individual devices, UTM provides comprehensive protection for entire networks and individual users.
By scanning all network traffic, filtering potentially harmful content, and blocking intrusions, UTM defends against a wide number of threats, including viruses, worms, spyware, malware, and network attacks. This consolidation simplifies network management, particularly beneficial for small and medium-sized businesses.
UTM typically includes features such as antivirus, anti-spyware, anti-spam, network firewalling, intrusion detection and prevention, content filtering, and leak prevention. Some UTM appliances also offer additional services like remote routing, network address translation, and VPN support.
The appeal of UTM lies in its simplicity, allowing organizations to manage multiple security tasks under one vendor, with support from a single IT team or segment, and through a unified console. This streamlined approach enhances security while reducing complexity and administrative burden.
Benefits of Using a Unified Threat Management Solution
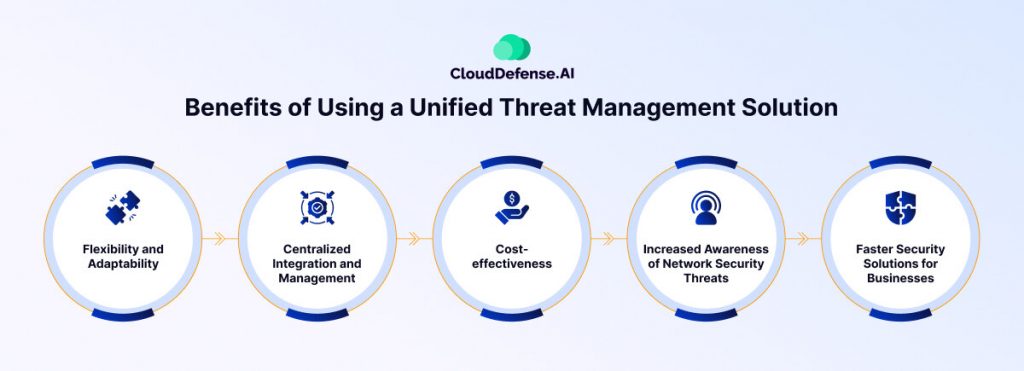
Using a UTM solution offers several key benefits for organizations looking to enhance their network security:
- Flexibility and Adaptability: UTM solutions provide flexibility by offering a range of security management tools that can be tailored to meet the specific needs of a network. Organizations can choose from various security technologies and licensing models, allowing them to deploy multiple security measures as needed. Automatic updates ensure that systems remain prepared to tackle the latest threats.
- Centralized Integration and Management: With a UTM, organizations can consolidate multiple security components into a single management console. This centralized approach simplifies monitoring and management, saving time and resources for IT teams. It also enables organizations to address threats impacting multiple network components more effectively.
- Cost-effectiveness: By reducing the number of devices needed to protect the network and streamlining management processes, UTM solutions can result in significant cost savings. Additionally, fewer staff are required to monitor the system, further reducing manpower costs.
- Increased Awareness of Network Security Threats: UTM solutions enhance awareness of network security threats by centralizing security functions and enabling faster operation. This allows organizations to implement advanced threat protection and better manage modern dangers such as advanced persistent threats.
- Faster Security Solutions for Businesses: UTM solutions streamline data processing and resource utilization, leading to higher efficiency compared to independent security components. This efficiency frees up resources that can be allocated to other critical network-dependent processes, enhancing overall business operations.
Next-generation Firewalls vs. UTM (Unified Threat Management)
Next-generation Firewalls (NGFW) and UTM solutions are both essential components of modern network security infrastructure, yet they differ in their approach and capabilities.
| Aspect | Next-generation Firewalls (NGFW) | UTM |
| Definition | Combines traditional firewall capabilities with additional features such as application awareness and advanced intrusion prevention systems. | Integrates multiple security features and services into a single device or service, including firewall, antivirus, VPN, and web filtering. |
| Flexibility | Offers flexibility in feature activation, allowing users to select specific functionalities based on their requirements. | May lack flexibility as services are bundled, potentially resulting in users receiving services they don’t necessarily need. |
| Management | Often involves managing a wide range of security functions through a single management console, which streamlines administration. | Managed through a single unified console, simplifying the complex management of multiple security components. |
| Scalability | Suitable for larger enterprises, offering scalability and integration with other security systems for enhanced cyber threat intelligence sharing. | Provides simplicity and consolidation of security services into a single platform, potentially limiting scalability for complex enterprise environments. |
| Key Features | – Deep packet inspection – Intrusion prevention systems- SSL inspection – Identity management integration – Advanced threat intelligence sharing | – Firewall protection – Antivirus – VPN functionality- Web filtering – Automatic updates |
| Target Audience | Larger enterprises require advanced security features and scalability. | Small to medium-sized businesses (SMBs) seeking simplicity and consolidation of security services. |
| Cost-effectiveness | Generally higher initial investment but may offer long-term cost savings through flexible feature activation and scalability. | May provide cost savings by consolidating multiple security functions into a single device, reducing the need for multiple separate devices. |
| Use Case | Ideal for organizations with complex network infrastructures and diverse security needs, requiring advanced threat protection capabilities. | Suited for organizations seeking simplicity and ease of management in their network security solutions, particularly SMBs with limited IT resources. |
How does UTM Work?
UTM employs two inspection methods to Protect networks: flow-based and proxy-based inspection. Flow-based inspection samples incoming data for malicious activity like viruses and intrusions. Meanwhile, proxy-based inspection scrutinizes packet contents passing through network security devices, aiding in threat detection. UTMs offer centralized security management by integrating various security functions into one platform.
This consolidation simplifies security protocols and reduces complexity for administrators. Continuously monitoring network traffic, UTMs ensure comprehensive protection against diverse cyber threats. With regular updates to counter emerging threats, UTMs are favored by small to medium-sized businesses seeking effective cybersecurity solutions with minimal oversight.
Features of a Unified Threat Management Platform
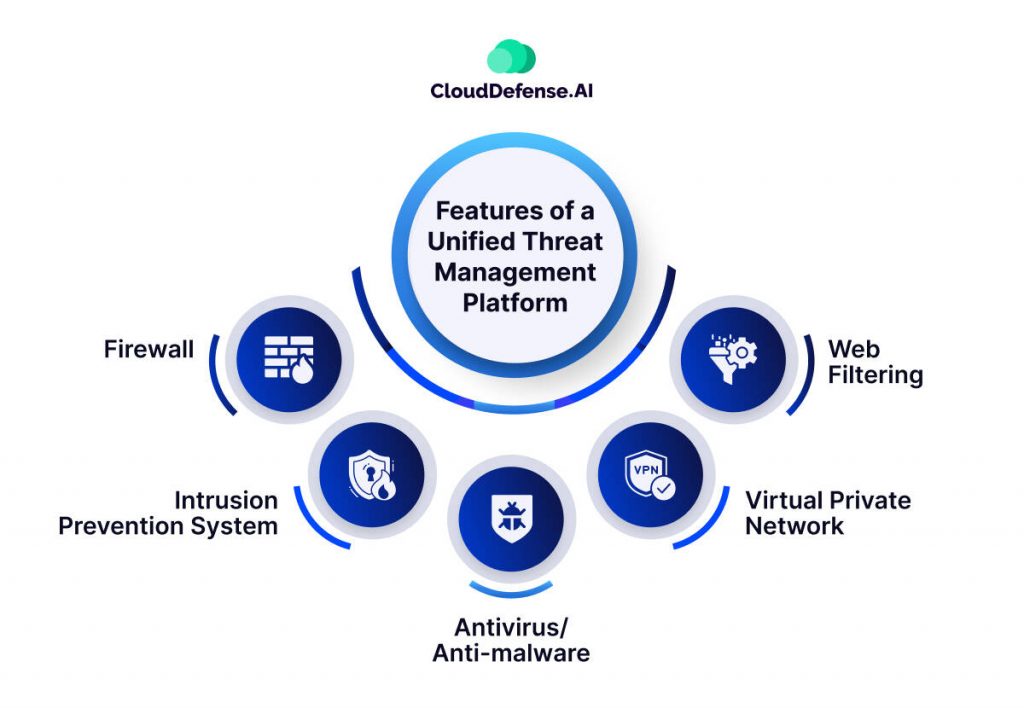
UTM solutions offer a comprehensive set of security features to protect organizations from various cyber threats. Here are the five key features typically included in a UTM:
1. Firewall: Acts as a barrier between trusted and untrusted networks, enforcing security policies for incoming and outgoing traffic.
2. Intrusion Prevention System: Monitors network and system activities for malicious behavior or policy violations, reacting in real time to block or prevent them.
3. Antivirus/Anti-malware: Scans network traffic and connected devices for malicious software, taking action to isolate or remove detected threats.
4. Virtual Private Network: Enables secure remote access to the network by encrypting data sent over the internet through a tunnel, ensuring data privacy and integrity.
5. Web Filtering: Offers access controls to websites and content on the internet based on policies, preventing access to inappropriate content and mitigating security risks.
In addition to these core features, advanced UTM solutions may include capabilities such as network sandboxing, wireless security controls, WAN optimization, email encryption, and application control, providing organizations with a multi-layered defense against cyber threats.
Challenges of Using UTM

UTM solutions were once popular for their integrated security features but now face several challenges in this new era of remote work and cloud-based infrastructure. Let’s explore some of them below.
- Lack of scalability: UTM appliances may struggle to keep up with the growth of a business, leading to performance issues and constraints as the number of users and network demands increase.
- Performance bottlenecks: High traffic volumes and resource-intensive functions can overwhelm UTM devices, causing network latency and impacting overall performance and user experience.
- Latency: Remote traffic must be backhauled to the data center for inspection by UTM devices, leading to delays in data transmission and user access.
- Cost: Initial investments in comprehensive UTM solutions can be significant, with ongoing expenses for updates, licensing, and potential hardware upgrades adding to the total cost of ownership.
- Feature redundancy: UTM solutions may overlap with existing security tools, resulting in unnecessary redundancy and underutilization of some features.
- Update management: Regular updates are essential to stay protected against emerging threats, requiring time and effort from information security teams to manage effectively.
- Integration challenges: Integrating UTM systems with existing infrastructure and software can be complex, leading to compatibility issues and potential disruptions in network operations.
As a result of these challenges, organizations are increasingly turning to cloud-native threat management systems that offer scalability, performance, and unified protection for users, regardless of their location or device.
How CloudDefense.AI can help?
CloudDefense.AI emerges as a formidable alternative to traditional unified threat management systems, offering a comprehensive suite of features customized to modern cloud infrastructures. Its end-to-end threat visibility empowers organizations to detect and mitigate potential threats across all layers of their cloud environment.
Using machine learning-based anomaly detection, CloudDefense.AI identifies zero-day attacks and irregular activities, protecting assets from evolving threats. Continuous activity monitoring ensures timely detection of both known and unknown threats, strengthening their overall security posture.
Additionally, real-time user behavior analysis enables the identification of insider threats and unusual activities, further enhancing security resilience. With risk validation capabilities, CloudDefense.AI prioritizes remediation efforts based on the severity of identified risks, ensuring efficient threat mitigation.
Its ability to detect misconfigured APIs adds an extra layer of protection, addressing modern security challenges effectively. In essence, CloudDefense.AI’s advanced threat detection and comprehensive security features position it as a strong replacement for traditional UTM systems, particularly in cloud-centric environments where agility and scalability are essential.







