It can be quite overwhelming for you if you are a company using cloud computing services when acronyms like CNAPP, CWPP, CSPM, and CIEM are thrown at them. Each of these security tools plays a critical role in creating a cloud security infrastructure in your company.
For you to ensure that the integrity and security of your cloud infrastructure are upheld, you must understand what these tools do and how they can be used to address security challenges promptly.
To help you kickstart your cloud security journey, we bring you this comprehensive blog that contains everything you need to know on CWPP, CSPM, CNAPP, and CIEM. This article aims to provide clarity on their purposes and how they contribute to a strong cloud security framework.
Let’s get started without further ado!
The Evolution of Cloud Security Technologies
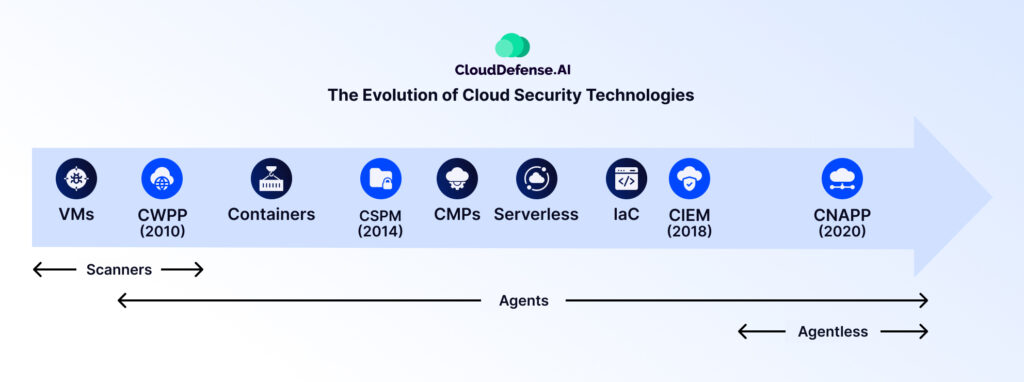
The introduction of cloud computing in 1999 and subsequent innovations like Salesforce’s SaaS and Amazon’s AWS transformed IT service management. This new technology didn’t only bring convenience but also brought forth a range of security challenges. Traditional tools struggled to adapt, relying on outdated methods.
A much-needed change was brought to the industry. Identity and access management, or IAM, systems stepped in, helping IT teams manage user identities and control access to cloud resources. Intrusion detection and prevention, or IDP, systems also joined the scene, allowing companies to scan for and stop attacks.
To tackle security issues with containerization and microservices, new platforms and solutions emerged in the market. Cybersecurity companies grew, providing solutions to the unique problems that cloud services had. Gartner, a technological research firm, started coining terms for different cybersecurity tools and created a market standard for each one. Company owners were introduced to terms like CWPP, CSPM, CNAPP, and CIEM.
Most recently, Gartner came up with Cloud-Native Application Protection Platforms, or CNAPP, a complete solution to all cloud security concerns. CNAPPs help to combine runtime protection, vulnerability management, and visibility in a single all-in-one suite.
It helps simplify security, as experts predict that by 2026, 80% of companies will cut down their cloud-native application security tools to three or fewer vendors, compared to 10 in 2022.
What Is a Cloud Workload Protection Platform (CWPP)?
A Cloud Workload Protection Platform, or CWPP, serves as a solution for companies seeking to strengthen specific workloads and applications in the cloud environment. Designed as a centralized software platform, CWPP acts as a strong defense mechanism against various risks, including malware, ransomware, DDoS attacks, configuration errors, insider threats, and data breaches.
CWPP Features
- Automated security operations
- Securing server workloads
- Container and serverless protection
- Conformity with industry standards
- Comprehensive security monitoring
- Native cloud security services and APIs
- Encryption, dlp, and access restrictions
- Isolation of tasks and runtime protection
- Gartner-defined essential features
CWPP Benefits
- Continuous Monitoring and Rapid Threat Reaction: CWPP ensures the continuous monitoring of workload behavior, detecting any suspicious activity. This enables swift reactions to security problems, reducing the likelihood of unauthorized access and potential data breaches.
- Identity-Based Access Controls for Zero-Trust Security: CWPP uses adaptive access controls, assigning permissions based on user identity and work roles. This zero-trust approach ensures that only authorized entities have access, enhancing cloud security and aligning with various data privacy regulations.
- Flexible Policy Enforcement and Compliance Management: With CWPP, organizations can dynamically apply and enforce policies to adapt to changing business requirements. This flexibility includes creating unique security maps and configuring micro-segments, ensuring granular control and compliance with industry regulations.
- End-to-End Visibility into Cloud Environments: CWPP provides deeper visibility into cloud environments, helping to manage vulnerabilities effectively. Organizations gain insights into potential attack paths, the nature of attacks, and how they may expand.
- Automated Security Lifecycle and Enhanced Operational Efficiency: CWPP is tailored to protect cloud workloads. It smoothens the security lifecycle, automating processes for efficient threat response. This automation lowers costs and increases operational efficiency, ensuring faster response times and uninterrupted user experiences in the cloud environment.
CWPP Challenges
- Limited Coverage and Complexity in Large-Scale Deployments: CWPP’s primary focus on specific workloads may result in certain parts of the overall cloud architecture being less well-covered. This specialization can lead to challenges in managing complexity, particularly in large-scale cloud installations where configuring and administering separate workloads becomes a bit complex.
- Integration Challenges for Comprehensive Security: Organizations may need to integrate additional solutions with CWPP. Limited visibility into the cloud control plane, inaccuracies in alert prioritization, and incomplete coverage due to agent-based deployment can require additional security measures.
- Scaling Issues and Maintenance Overheads: Some CWPP tools in the market face difficulties in scaling, impacting their effectiveness as cloud environments expand. Maintenance, including the installation and upkeep of agents on every asset, could lead to increased overhead expenditures. In the end, this might potentially affect the overall efficiency of the security solution.
- Performance Impact on Cloud Workloads: The installation of agents for monitoring and real-time threat detection, a common approach in CWPP deployment, may impact the performance of cloud workloads. This exchange between security measures and performance could pose serious challenges, especially in dynamic and resource-intensive cloud environments.
What is Cloud Security Posture Management (CSPM)?
Cloud Security Posture Management, or CSPM, is a tool dedicated to detecting and remedying misconfigurations, ensuring compliance, and addressing security threats within cloud environments. This strategic approach is important for businesses using cloud infrastructures such as IaaS, PaaS, and SaaS.
CSPM Features
- Data governance and compliance management
- Third-party threat intelligence compatibility
- Risk assessments and vulnerability detection
- Misconfiguration and compliance hazard detection
- Multi-cloud configuration management
- Advice and remediation
- Real-time monitoring and automated assessments
- Risk monitoring and evaluation
- Automation for policy enforcement
- Automated threat intelligence
- Detect and remediate misconfiguration
- Versatile cloud environment compatibility
CSPM Benefits
- Compliance Checks Aligned with Requirements: CSPM carries out compliance checks that are in line with corporate, regional, and industry-specific standards. This greatly helps to reduce the burden on cybersecurity teams in companies.
- Proactive Risk Identification and Recommendations: CSPM identifies potential risks and instantly provides recommendations to enhance the security posture. By pinpointing vulnerabilities and misconfigurations, CSPM gives organizations the power to take preventive measures.
- Real-time Security and Compliance Monitoring: CSPM enhances visibility for other stakeholders by offering real-time security and compliance monitoring. This transparency enables enterprises to respond swiftly to threats.
- Simplified Risk Detection and Remediation through Automation: CSPM simplifies the detection and remediation of risks in complex cloud environments through automation. Organizations can smoothen their security processes by automating routine tasks related to risk identification and mitigation.
- Multi-Cloud Support for Diverse Environments: Supporting multiple cloud environments such as AWS, Azure, and GCP, CSPM offers flexibility and coverage across diverse infrastructures. This adaptability ensures that organizations with multi-cloud strategies can maintain a consistent approach to security and compliance across their cloud providers.
CSPM Challenges
- Integration Challenges with Diverse Cloud Platforms: CSPM may face difficulties integrating with certain cloud platforms or external tools. This limits its effectiveness in environments with specialized cloud services.
- Insights and Coverage Limitations: CSPM may encounter limitations in providing insights into workloads and may exhibit a lack of coverage at the application level. This constraint could impact its ability to offer an overall view of security across the entire cloud infrastructure.
- Operational Challenges and Skill Dependency: Managing complex and rapidly evolving cloud systems using CSPM may pose operational challenges. Efficient utilization of the tool requires a highly skilled workforce capable of understanding and effectively lactating upon its findings. This dependency on skilled personnel can present a barrier for organizations seeking to maximize the tool’s potential for risk detection and mitigation.
What is Cloud Infrastructure Entitlements Management (CIEM)?
Cloud Infrastructure Entitlement Management, or CIEM, focuses on identity and access management in the cloud. It serves the need for enterprises to manage and protect access to important resources. Cloud environments can be sophisticated with an increasing number of users and permissions. This is where CIEM plays a major role by preventing unwanted access and potential data breaches.
CIEM Features
- Examination of multi-cloud permissions.
- Compliance implementation and least-privilege access.
- Behavioral analysis for security concerns.
- Strong identity governance.
- Regular review of entitlements.
- Enforcement of access restrictions.
CIEM Benefits
- Enhanced Visibility and Proactive Vulnerability Management: CIEM solutions provide enhanced visibility into identities, resources, and permissions in public cloud environments. This visibility allows identifying potential vulnerabilities that need to be remediated. On top of that, risk prioritization ensures that security teams focus on addressing the most critical threats first.
- Remediation and Automated Risk Mitigation: CIEM simplifies fixing security issues by automating the process. It quickly corrects high-risk permissions and dangerous combinations seamlessly within established workflows. This speeds up the resolution of IAM security problems, making complex cloud challenges easier to handle.
- Reduced Attack Surface: CIEM solutions are crucial in reducing the attack surface by removing inactive users, controlling excessive permissions, detecting unusual behaviors, and revoking standing privileges. This strategy minimizes vulnerability periods, enhancing overall cloud security.
CIEM Challenges
- Limited Full IAM Features: Certain CIEM solutions may lack all IAM features, potentially leading to incomplete context and visibility and hindering organizations from fully understanding and managing their cloud identities.
- False Alerts: CIEM systems may introduce challenges related to false alerts, potentially causing confusion and diverting security teams’ attention from genuine threats. This impacts the overall effectiveness of threat detection and response mechanisms.
- Complex Implementation: Implementing CIEM in extensive cloud settings might be complex. It demands precise design considerations and integration with existing IAM solutions, which further adds complexity to deployment processes.
What is a Cloud Native Application Protection Platform (CNAPP)?
A Cloud Native Application Protection Platform, or CNAPP, is a comprehensive solution that includes CWPP, CSPM, CIEM, IaC scanning, and more. This platform ensures thorough protection for cloud workloads, applications, identities, access management, and development environments, protecting against vulnerabilities and cyber attacks.
Specifically tailored for containerized and serverless environments, CNAPP solutions offer targeted security for cloud-native applications and their supporting infrastructure. It helps in addressing challenges posed by microservices, serverless architectures, and containerized environments.
CNAPPs provide organizations with essential tools and best practices to secure applications built on cloud architectures.
CNAPP Features
- Complete cloud security protection.
- Cloud path analysis for attack points.
- Serverless environment security.
- Real-time detection with threat intelligence.
- Automated compliance assessments.
- End-to-end security for microservices.
- Seamless DevOps interaction.
- Strong container security features.
- Integration with various security signals.
- Coverage of multiple security domains.
CNAPP Benefits
- All-in-one Cloud-Native Security: CNAPP offers a complete security solution for cloud-native applications. It surpasses the individual focus of CSPM, CIEM, and CWPP, ensuring protection for cloud-native workloads and applications.
- Specialized and Tailored Focus: Unlike broader-reaching solutions, CNAPP is purpose-built for cloud-native settings. It provides specialized security measures exclusively designed for the unique challenges of cloud-native applications and workloads.
- Advanced Threat Intelligence: CNAPP can detect and mitigate threats in real-time by using sophisticated threat intelligence techniques such as machine learning algorithms and behavioral analytics.
- Seamless DevOps Integration: It integrates smoothly with DevOps methods, ensuring security measures are incorporated at the outset of the software development lifecycle.
- Enhanced Visibility and Governance: CNAPP delivers increased visibility and governance capabilities customized for the specific requirements of cloud-native apps, providing end-to-end security for microservices-based architectures, containers, and serverless applications.
CNAPP Challenges
- Training and Familiarization Requirement: Admins and security teams might need training to use CNAPP tools fully. This is crucial for configuring and using the platform effectively.
- Resource Intensiveness of Advanced Features: Using advanced threat intelligence in CNAPP may need more system resources, impacting overall performance. Organizations need to balance this by evaluating their infrastructure capabilities for system performance while ensuring security.
Comparing cloud security solutions: CSPM vs CWPP vs CNAPP vs CIEM
| CWPP | CSPM | CIEM | CNAPP | |
| Focus Area | Securing specific workloads and applications in the cloud. | Configurations, compliance, and security posture of cloud services. | Identity and access management for cloud resources. | Complete security for cloud-native applications. |
| Benefits | Continuous workload monitoring.Identity-based access controls.Multiple layers of protection. | Compliance checks and enforcementDetection of misconfigurations.Log management and monitoring. | Enhanced visibility into identities and permissions.Streamlined access management.Countering insider threats and data exfiltration. | Sophisticated threat intelligence for real-time detection.Integration with DevOps for secure development.Increased visibility and governance for cloud-native apps. |
| Challenges | Limited coverage beyond workloads.Difficulty in scaling. | False alerts and manual review challenges.Complexity in large-scale deployments. | Difficult to learn for administrators.Limited application-level security coverage. | Training for administrators and potential resource impacts.Careful planning for integration in complex settings. |
Which solution should I choose?
Each of the tools mentioned in this article caters to specific needs that a company might have. Choosing the right cloud security platform can be done by comprehensively evaluating every feature that the tools provide and by judging whether they line up with the unique challenge that your company is facing.
However, you might’ve noticed how an individual tool cannot provide a complete cloud security solution. Most people choose to buy different tools from multiple vendors. This introduces complexities involved with integrating different tools from different vendors into your company’s cloud infrastructure. This is why companies all over the world have shifted their focus towards CNAPPs.
CNAPPs offer you a comprehensive set of features under one umbrella that is more than you need to cater to all your cloud protection requirements. This unique selling point is one major reason that has resulted in the CNAPP market getting bloated quickly, as market analysts predict the CNAPP market value will stand at $19.3 billion by 2027.
There are loads of CNAPP tools available in the market, but a specific one stands out the most with its unique capabilities.
Meet CloudDefense.AI
CloudDefense.AI is a leading CNAPP platform that ensures the complete security of cloud-native applications and has 360-degree visibility into all the components in a cloud infrastructure. CloudDefense.AI, through its CNAPP platform, aims to curb all the cybersecurity risks associated with your application and infrastructure at scale.
The agentless solution integrates with your cloud infrastructure and Kubernetes to automate scanning and generate reports regarding vulnerabilities, allowing your team to address them in real-time.
CloudDefense.AI, through its integrated platform, combines multiple security tools that you may need to fortify your organization. These include:
- SAST
- DAST
- SCA
- CIEM
- CWPP
- CSPM
- Hacker’s View™
- Noise Reduction
All these tools are integrated into a single solution that makes it possible to have a unified approach to the security of applications and multi-cloud environments.
What makes this platform stand out? It is the use of real-time AI capability to detect and investigate threats. Using behavior indicators and programmable automation, it detects deviations from best practices and identifies threats that jeopardize 20+ compliances. The platform is built around Gartner’s recommendations to ensure top-notch security of all major cloud services.
CloudDefense.AI promotes collaboration between your DevOps, operations, and security teams through Slack, Jira, Webhooks, and others and allows you to enhance the speed of application development. Book a free demo right now to test out the immense power that CloudDefense.AI hands you.







