What is Managed Detection and Response (MDR)?
Managed Detection and Response (MDR) is a cybersecurity service that provides continuous threat monitoring, detection, and response to security incidents.
It brings together cutting-edge technologies, valuable threat intelligence, and skilled human expertise to detect and address cyber threats in real time. The Managed Detection and Response (MDR) services encompass endpoint detection, network monitoring, behavioral analytics, and thorough incident investigations.
MDR differentiates itself from traditional security by focusing on proactive threat hunting and quick incident response, reducing dwell time and damage. Ideal for organizations lacking in-house security expertise, it provides 24/7 protection and expert remediation, enhancing their defense against evolving cyber threats.
MDR Benefits
MDR services offer a comprehensive approach to cybersecurity, helping organizations effectively detect, respond to, and mitigate cyber threats.
- Real-Time Threat Detection & Monitoring: Continuous monitoring with advanced tools ensures early detection of anomalies and potential threats, enabling proactive defense.
- Rapid Incident Response & Remediation: MDR swiftly neutralizes threats using automated defenses and expert-driven remediation, minimizing damage and preventing recurrence.
- Access to Expertise & Advanced Technology: Organizations gain cybersecurity specialists and cutting-edge tools, enhancing protection against evolving threats.
- Scalability & Flexibility: MDR adapts to an organization’s growth and evolving security needs, providing customized and scalable protection.
- Compliance & Reporting: Ensures regulatory compliance, supports audits, and provides detailed security reports to meet industry standards.
- Enhanced Cybersecurity Resilience: A multi-layered security approach strengthens defenses, facilitates disaster recovery, and improves overall resilience.
- Customizable Security Solutions: Customized MDR features align with specific organizational requirements for optimal security coverage.
- Vulnerability Scanning: Regular scans identify and address security weaknesses, reducing risk exposure and strengthening defenses.
How does MDR work?
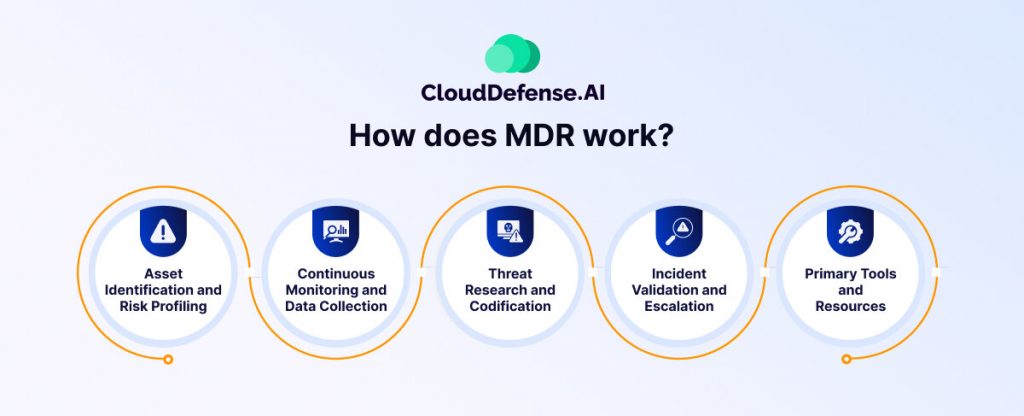
MDR operates through a combination of advanced security technologies, continuous monitoring, expert threat analysis, and rapid response strategies. It is designed to detect, investigate, and respond to cyber threats in real-time, minimizing potential damage to an organization. Here’s a detailed breakdown of how MDR works:
Continuous Threat Monitoring
MDR providers use Security Information and Event Management (SIEM), Extended Detection and Response (XDR), and Endpoint Detection and Response (EDR) tools to monitor networks, endpoints, and cloud environments 24/7. These technologies collect and analyze vast amounts of security data, looking for suspicious activities, anomalies, or malicious indicators.
Threat Detection & Advanced Analytics
MDR uses artificial intelligence (AI), machine learning (ML), and behavioral analytics to detect sophisticated threats. This includes:
- Signature-based detection: Identifies known malware and threats using predefined signatures.
- Anomaly detection: Uses behavioral baselines to detect deviations from normal activities.
- Threat intelligence integration: Leverages global threat intelligence feeds to recognize emerging attack patterns.
Proactive Threat Hunting
MDR includes proactive threat hunting, where cybersecurity experts manually investigate and analyze potential threats that automated tools might miss. This involves:
- Searching for Indicators of Compromise (IoCs) and Indicators of Attack (IoAs).
- Identifying persistent threats that may be hiding within the network.
- Investigating suspicious behaviors before they escalate into full-scale attacks.
Threat hunters use historical data and real-time monitoring to uncover hidden cyber threats, reducing dwell time and exposure.
Incident Investigation & Risk Assessment
Once a potential threat is identified, MDR teams conduct an in-depth investigation to determine:
- The scope and impact of the threat.
- How the attacker infiltrated the system.
- Whether the attack is part of a larger, coordinated effort.
Using forensic analysis, log correlation, and attack pattern recognition, MDR specialists assess the level of risk and potential damage.
Rapid Incident Response & Remediation
MDR services provide rapid incident response to contain and neutralize threats. This process includes:
- Automated response actions: MDR systems can isolate infected endpoints, block malicious IPs, and terminate suspicious processes.
- Expert-guided intervention: Security analysts provide actionable recommendations and assist in manual remediation.
- Patch management & vulnerability fixing: MDR teams help organizations apply necessary patches and mitigate security gaps.
By responding in real-time, MDR reduces the risk of data breaches and operational disruptions.
Post-Incident Analysis & Reporting
After an incident is resolved, MDR providers conduct a thorough post-mortem analysis, which includes:
- Root cause analysis: Identifying vulnerabilities that led to the attack.
- Security posture recommendations: Providing guidance on improving cybersecurity measures.
- Detailed reporting: Delivering audit-ready reports that outline the attack, response actions, and future prevention strategies.
This step helps organizations strengthen their defenses and prevent similar incidents in the future.
Compliance & Regulatory Support
MDR helps organizations maintain compliance with industry regulations such as:
- GDPR (General Data Protection Regulation)
- HIPAA (Health Insurance Portability and Accountability Act)
- PCI-DSS (Payment Card Industry Data Security Standard)
- ISO 27001 (Information Security Standard)
By ensuring regulatory adherence, MDR assists organizations in avoiding legal penalties and reputational damage.
Continuous Improvement & Security Optimization
MDR is not just a one-time service; it evolves alongside emerging threats. Continuous improvement efforts include:
- Regular security assessments and tuning of detection rules.
- Updating threat intelligence databases.
- Enhancing incident response playbooks.
- Conducting security awareness training for employees.
This ongoing process ensures organizations stay resilient against evolving cyber threats.
MDR is an all-in-one cybersecurity solution that combines cutting-edge technology, human expertise, and automated response mechanisms. It enables organizations to detect, analyze, and respond to cyber threats efficiently while improving their overall security posture.
Managed Detection and Response (MDR) Service Functions
MDR services provide organizations with continuous monitoring, threat detection, and rapid response capabilities to defend against cyber threats. By combining advanced technology, expert analysis, and automated response mechanisms, MDR enhances an organization’s security posture. Below are the key functions of MDR:
24/7 Threat Monitoring & Detection
MDR continuously monitors an organization’s network, cloud environments, and endpoints using advanced security technologies like Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and Extended Detection and Response (XDR). These systems analyze massive amounts of security data in real-time to detect:
- Suspicious activity and unauthorized access attempts.
- Anomalies and deviations from normal behavior.
- Indicators of Compromise (IoCs) that signal potential attacks.
By ensuring round-the-clock surveillance, MDR helps prevent security incidents before they escalate.
Advanced Threat Analytics & Intelligence
To combat evolving cyber threats, MDR employs artificial intelligence (AI), machine learning (ML), and behavioral analytics. These technologies allow MDR providers to:
- Detect complex attack patterns and distinguish between legitimate activities and malicious behaviors.
- Integrate with global threat intelligence feeds to recognize zero-day vulnerabilities and emerging threats.
- Use sandboxing and heuristic analysis to identify unknown malware and sophisticated cyberattacks.
This data-driven approach enhances an organization’s ability to detect and respond to both known and unknown threats.
Proactive Threat Hunting
Unlike traditional security solutions that rely on automated detection, MDR includes proactive threat hunting. Security analysts manually investigate potential threats that may bypass automated tools. This process involves:
- Searching for Indicators of Attack (IoAs) that signal an ongoing intrusion.
- Identifying Advanced Persistent Threats (APTs) and stealthy cyberattacks.
- Conducting forensic analysis to trace attack vectors and prevent future breaches.
Threat hunting helps organizations stay ahead of attackers by detecting hidden threats before they cause harm.
Incident Investigation & Risk Assessment
When a potential security incident occurs, MDR teams conduct an in-depth investigation to determine its severity and impact. This includes:
- Analyzing logs, network traffic, and system behaviors to understand the attack.
- Identifying the origin and scope of the threat.
- Evaluating business risks and providing recommendations for mitigation.
By offering a clear picture of security incidents, MDR enables organizations to take informed actions to protect their systems.
Rapid Incident Response & Containment
MDR services ensure that threats are neutralized as quickly as possible. When an attack is detected, MDR teams:
- Automatically isolate compromised endpoints and affected systems.
- Block malicious IP addresses, domains, and unauthorized access attempts.
- Provide expert guidance on additional containment measures.
Fast and effective response minimizes damage and prevents the spread of cyberattacks.
Threat Remediation & Recovery
Beyond containment, MDR helps organizations fully recover from security incidents by:
- Removing malware and closing security gaps.
- Applying patches and updating configurations to prevent re-exploitation.
- Assisting in disaster recovery planning to restore normal operations.
With expert-led remediation, businesses can resume operations quickly and securely after an attack.
Compliance Management & Reporting
MDR services help organizations meet regulatory requirements and maintain industry compliance by:
- Ensuring adherence to standards like GDPR, HIPAA, PCI-DSS, and ISO 27001.
- Generating detailed, audit-ready reports documenting security incidents and response actions.
- Providing continuous monitoring and breach detection to support compliance efforts.
With clear reporting and compliance assistance, MDR minimizes regulatory penalty risks and improves data protection.
Security Posture Improvement & Optimization
MDR is not just about responding to threats—it also helps organizations strengthen their overall security strategy by:
- Regularly refining security configurations and detection rules.
- Conducting security assessments and penetration testing.
- Providing cybersecurity awareness training for employees.
Through continuous improvement, MDR ensures businesses stay resilient against evolving cyber threats.
MDR integrates technology, expertise, and real-time monitoring to detect and respond to cyber threats. By combining proactive threat hunting, automated response, and compliance support, MDR strengthens security and reduces risk. Organizations using MDR can outpace attackers and decrease security incidents resilience.
Business Challenges for MDR Adoption?
Businesses encounter several challenges when adopting Managed Detection and Response (MDR) solutions, which can hinder their ability to effectively combat cyber threats. Below are some of the key challenges organizations face:
Staffing and Resource Limitations
A major challenge in MDR adoption is the shortage of skilled cybersecurity professionals. Many organizations struggle to staff security teams, complicating the management of MDR solutions. Even with advanced security tools, they often lack the time and expertise to maximize effectiveness. This gap can weaken overall security posture.
Alert Fatigue
As organizations deploy more security tools, teams often face a flood of alerts, many being false positives or low-priority warnings. This makes it hard to distinguish between routine and critical threats. Without enough personnel and expertise to manage alerts, burnout increases, raising the risk of missing serious threats. Consequently, this challenge may delay responses or overlook vulnerabilities, risking security breaches. Read more about it here.
Budget Constraints
Small to mid-sized businesses find investing in MDR financially challenging. While they understand the need for strong cybersecurity, costs of implementation, maintenance, and skilled personnel are burdensome. Justifying these to stakeholders with other priorities complicates MDR adoption, often resulting in delayed upgrades or less comprehensive solutions, leaving them vulnerable to cyber threats.
Complex and Evolving Threats
Cyber threats evolve, with attackers using new tactics to bypass defenses. Organizations must adapt strategies to detect and mitigate threats like ransomware, phishing, insider attacks, and data breaches. Keeping pace requires ongoing monitoring, updates, and advanced threat intelligence, increasing pressure on security teams and needing continuous cybersecurity investments.
Increasing Attack Surface
Cloud computing, IoT devices, and remote work have expanded organizations’ attack surfaces, complicating visibility and control over cyber threats. As IT environments grow more complex and interconnected, security teams find it challenging to monitor and respond to threats across platforms. Without proper measures, businesses face increased vulnerability to cyberattacks.
MDR vs. EDR
MDR is a cybersecurity service that monitors and manages security across an organization’s IT environment. It uses state-of-the-art solutions, including EDR, to provide improved visibility and threat response capabilities with a dedicated security team.
EDR, or Endpoint Detection and Response, is a cybersecurity tool deployed to protect specific endpoints within an organization’s network. It relies on software agents or sensors to capture endpoint data for analysis, serving as the baseline monitoring and threat detection foundation in cybersecurity strategies.
Here is a table for you to understand the differences between these two security approaches:
| Aspect | EDR | MDR |
| Capabilities | Monitors endpoints for threats bypassing antivirus measures. | EDR “as a service” that offers similar capabilities with 24/7 managed services. |
| Components | Real-time endpoint monitoring, Behavioral analysis, Threat database, Network containment, and remediation recommendations. | Adds 24/7 managed services, Human threat hunting, Managed investigation, Guided response, Prioritization, and Communication hub. |
| Methods/Tools | Software-based EDR solution. | Endpoint protection platform (EPP), Network analysis, Next-gen firewall, Email security, IAM, CWPP, CASB, DLP. |
| Threat Visibility | Endpoints. | Endpoints, users, network assets, cloud workloads, email, data, and other assets. |
| Protection | Baseline for cybersecurity, core for advanced solutions | Combines real-time monitoring with proactive actions via skilled cybersecurity professionals. |
Selecting an MDR Solution
MDR is an irreplaceable security strategy that can not only halt ongoing attacks but also ensure resilience against future threats, providing peace of mind against recurring cyber incidents. To select the right MDR solution for your company you first need to assess the provider’s in-house expertise. Check whether they have a 24/7 security operations center and incident response teams that are skilled in diverse platforms.
Equally important is evaluating the security tools in their arsenal. The MDR provider should offer complete network visibility, strong data analytics capabilities, and swift incident response mechanisms. A solution with both expertise and cutting-edge tools ensures effective threat detection and mitigation, providing your company with optimal protection.






